Security system and method based on data exchange between cloud end and edge end
A data exchange and security system technology, applied in the field of information security, can solve problems such as production safety hazards, lack of safety protection, and inadequacy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
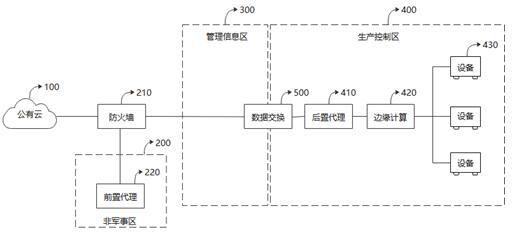
[0045] The technical solution of the present invention will be clearly and completely described below in conjunction with the accompanying drawings. Apparently, the described embodiments are some, but not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0046]According to the principle of network security defense in depth, enterprise networks are usually divided into multiple security zones. For the convenience of description, this embodiment assumes that the enterprise network is divided into three security areas: the demilitarized zone (DMZ), the management information area, and the production control area: the demilitarized zone (DMZ) is located between the enterprise intranet and the extranet. It separates the sensitive internal network from other networks that provide...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More