Block chain-based scenic spot passenger dishonest list updating method and related device
An update method and block chain technology, applied in the field of block chain, can solve the problem that other scenic spots cannot share the update of passenger dishonesty list, and achieve the effect of accurate and objective evaluation results
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
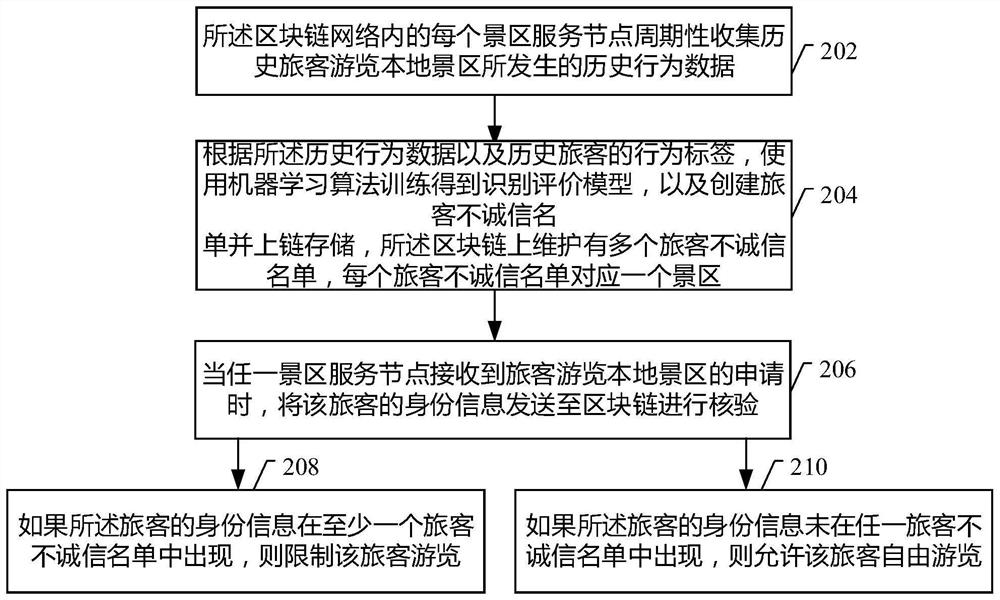
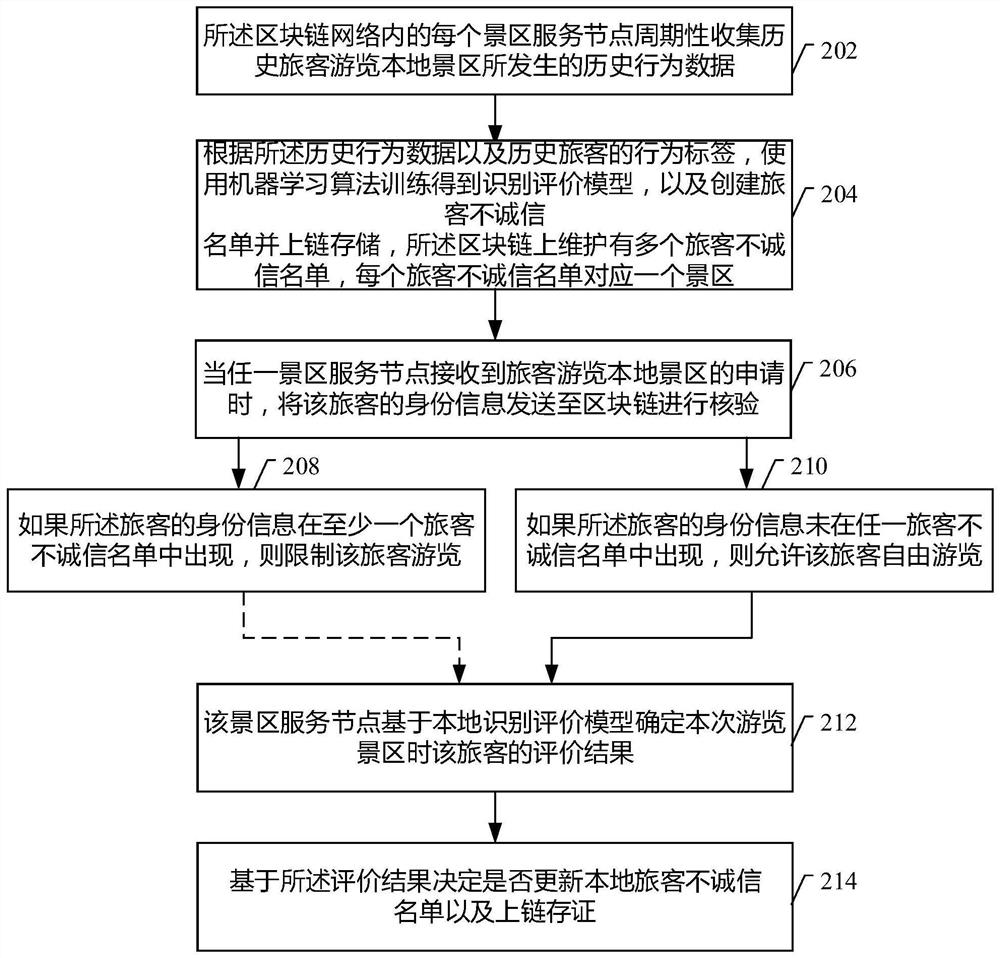
[0036] refer to figure 2 As shown, it is a schematic diagram of the steps of a blockchain-based method for updating the tourist dishonesty list of scenic spots provided by the embodiment of this specification, which is applied to a blockchain network containing multiple scenic spot service nodes. The method may include the following steps:
[0037] Step 202: Each scenic spot service node in the blockchain network periodically collects historical behavior data of historical tourists visiting local scenic spots.
[0038] In this embodiment of the specification, the passenger's behavior data may include: consumption information, trajectory information, length of stay, and violation screen information.
[0039] It should be understood that when collecting passenger behavior data, it can be collected through external devices such as cameras, scanners, and vending terminals. These behavioral data can be uniformly stored in the corresponding database, and can be obtained purposeful...
Embodiment 2
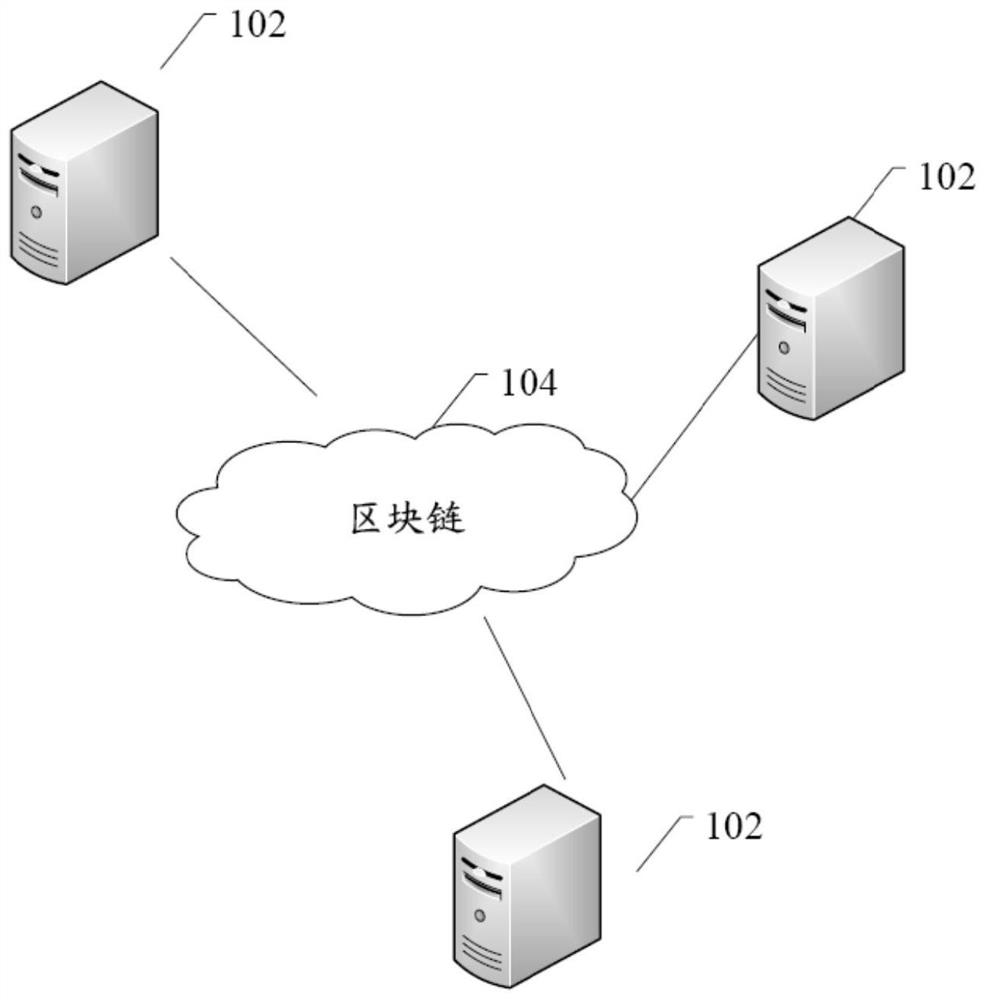
[0083] refer to Figure 4 As shown, the system 400 for updating the dishonesty list of tourists in scenic spots based on block chain provided by the embodiment of this specification includes: a plurality of scenic spot service nodes 402 and block chain 404;
[0084] Each scenic spot service node 402 in the block chain network periodically collects historical behavior data of historical tourists visiting local scenic spots;
[0085] According to the historical behavior data and the behavior labels of historical passengers, a machine learning algorithm is used to train the identification and evaluation model, and a passenger dishonesty list composed of the passenger's identity information is created and stored on the chain. Each dishonest list of passengers corresponds to a scenic spot, and the identity information of the same passenger is allowed to appear in different lists of dishonest passengers;
[0086] When any scenic spot service node receives an application from a passen...
Embodiment 3
[0112] Figure 5 It is a schematic structural diagram of an electronic device according to an embodiment of this specification. Please refer to Figure 5 , at the hardware level, the electronic device includes a processor, and optionally also includes an internal bus, a network interface, and a memory. Wherein, the memory may include a memory, such as a high-speed random-access memory (Random-Access Memory, RAM), and may also include a non-volatile memory (non-volatile memory), such as at least one disk memory. Of course, the electronic device may also include hardware required by other services.
[0113] The processor, the network interface and the memory can be connected to each other through an internal bus, which can be an ISA (Industry Standard Architecture, industry standard architecture) bus, a PCI (Peripheral Component Interconnect, peripheral component interconnection standard) bus or an EISA (Extended Industry StandardArchitecture, extended industry standard archi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com