Strategy conflict processing method and device based on complex network
A conflict resolution and complex network technology, applied in the computer field, can solve problems such as difficult maintenance, restricted access, and failure to consider the factors of the subject and object of the strategy, and achieve the effects of scientific and reasonable selection, automation, and reduced workload
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0048] In order to make the purposes, technical solutions and advantages of the embodiments of the present invention clearer, the technical solutions in the embodiments of the present invention will be clearly and completely described below with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments These are some embodiments of the present invention, but not all embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those of ordinary skill in the art without creative efforts shall fall within the protection scope of the present invention.
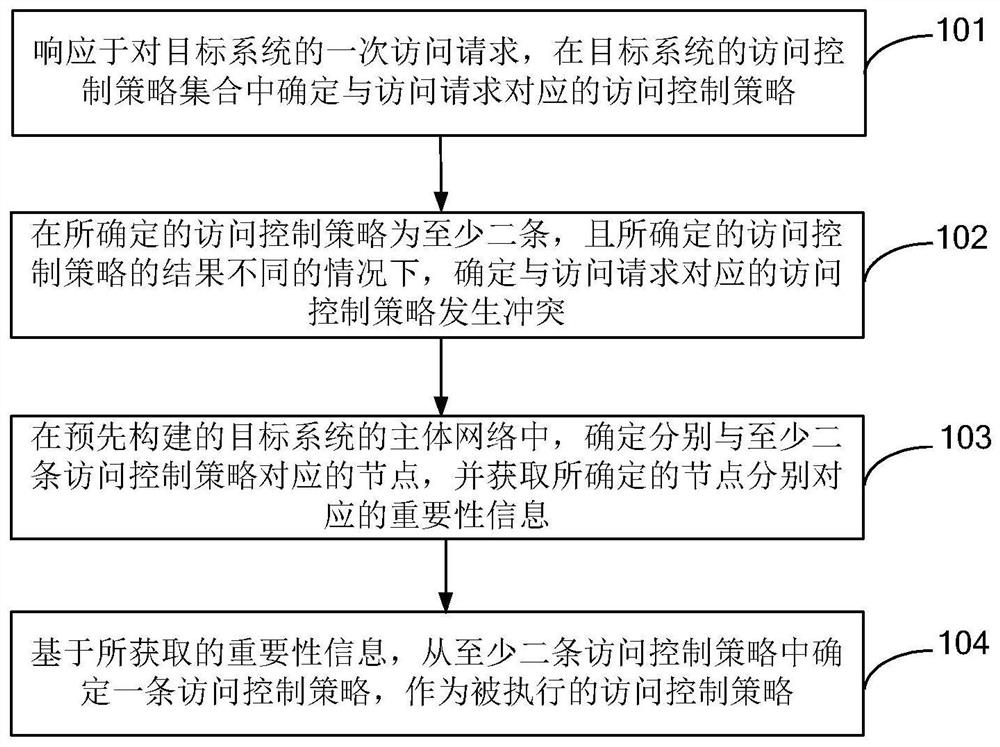
[0049] Combine below Figure 1-Figure 5 Describe the complex network-based policy conflict processing method of the present invention.
[0050] see figure 1 , figure 1 is a schematic flowchart of the complex network-based policy conflict processing method provided by the present invention, figure 1 The shown complex network-base...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More