Method and system for managing security tiers
a security tier and management system technology, applied in the field of data protection, can solve the problems of significant greater element of risk to the confidentiality and integrity of information, inaccessible to the public, and unauthorized person or machine may intercept any information
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
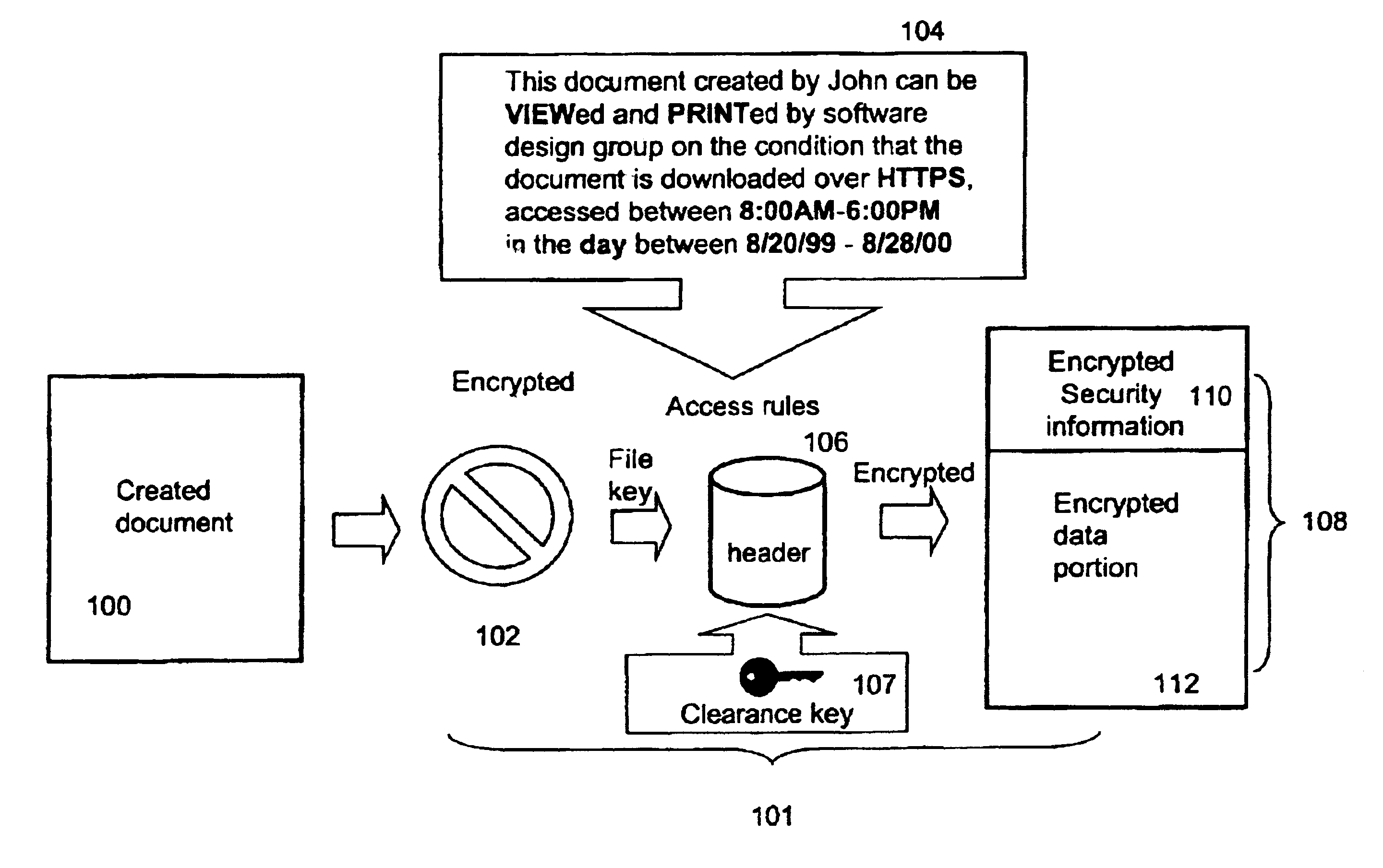
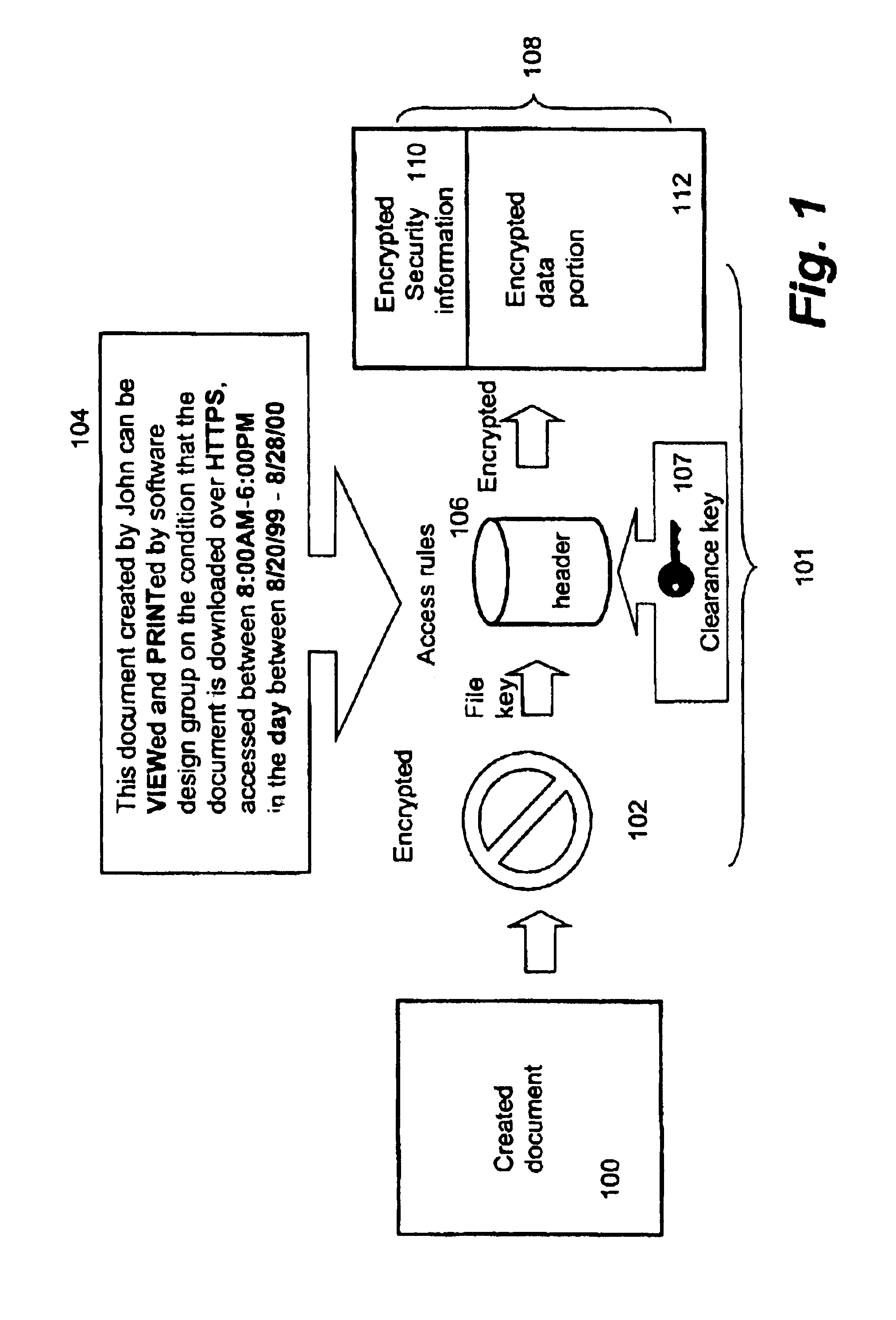
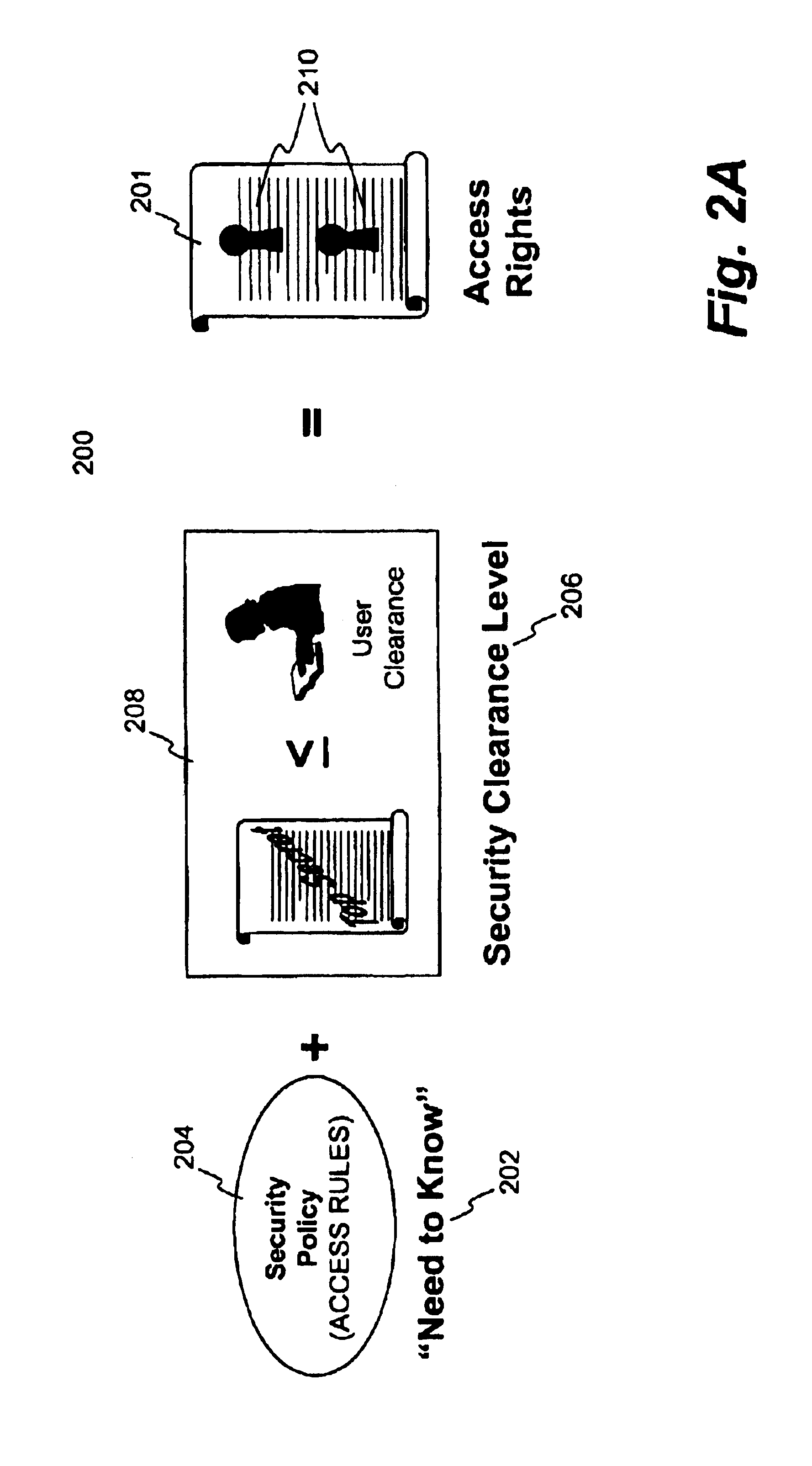
[0032]The present invention pertains to a process, a system, a method and a software product for securing electronic data or digital assets. According to one aspect of the present invention, a new security level is to be inserted into a set of existing security levels. Without implicating the accessibility to secured files classified at one of the existing security levels, the controllability or restrictiveness of the new security level is determined with respect to the most restrictive security level or the least security level in the existing security levels. A set of proper security parameters are generated for the new security level and subsequently the existing security levels are mapped to accommodate the new security level. According to another aspect of the present invention, a security level is removed from a set of existing security levels. The security parameters for the security level to be deleted are either folded up or down to an immediate next security level, dependi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More