Double CPU protection information shared system and information processing method based on double port RAM
A technology for protecting information and sharing systems, applied in the field of hardware systems, can solve problems such as large space occupied by computing programs, less program space, and device inheritance limitations, so as to reduce research and development costs and production costs, smooth the development process, and shorten the development cycle Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
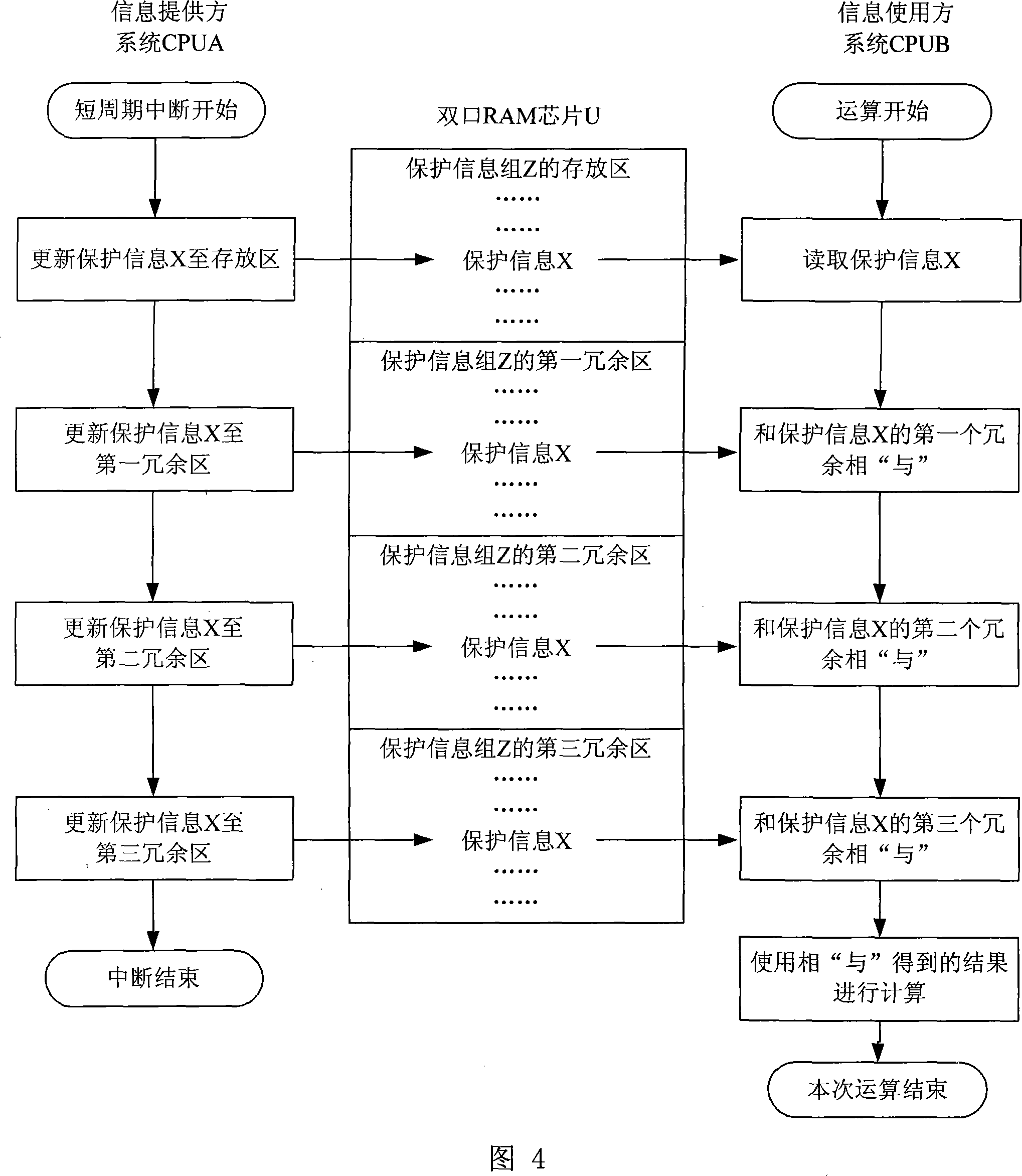
[0022] When the dual-CPU protection information sharing system based on dual-port RAM in this embodiment is used in situations where protection information requires high real-time performance and low reliability requirements, the specific working process is shown in FIG. 3 . The information providing system (such as the system CPUA) stores the protection information group Z in the dual-port RAM chip U in real time during the 600Hz or 1200Hz periodic interrupt; the information using system (such as the system CPUB) uses any protection information in the protection information group Z When X, the information will be read from the dual-port RAM chip U, and the algorithm with strong anti-interference ability will be used for protection calculation, which satisfies the information sharing between the two CPUs and ensures the real-time performance of the information. .
Embodiment 2
[0024] This embodiment is a technical solution formed by further analysis and changes based on embodiment 1, and it is used in situations where the protection information group requires high real-time performance and high reliability. The specific working process is shown in FIG. 4 . The system CPUA stores the protection information group Z in the dual-port RAM chip U in real time during the 600Hz or 1200Hz periodic interrupt, and redundantly stores the protection information group three times in the adjacent area of the dual-port RAM chip; the system CPUB uses the protection When any protection information X in the information group Z is used, the result obtained after "ANDing" the protection information X and its corresponding three redundant information is used for protection calculation, so as to ensure that the information will not cause system error when the protection information X is wrong. move.
[0025] In this way, since the system CPUA is constantly updating the ...
Embodiment 3
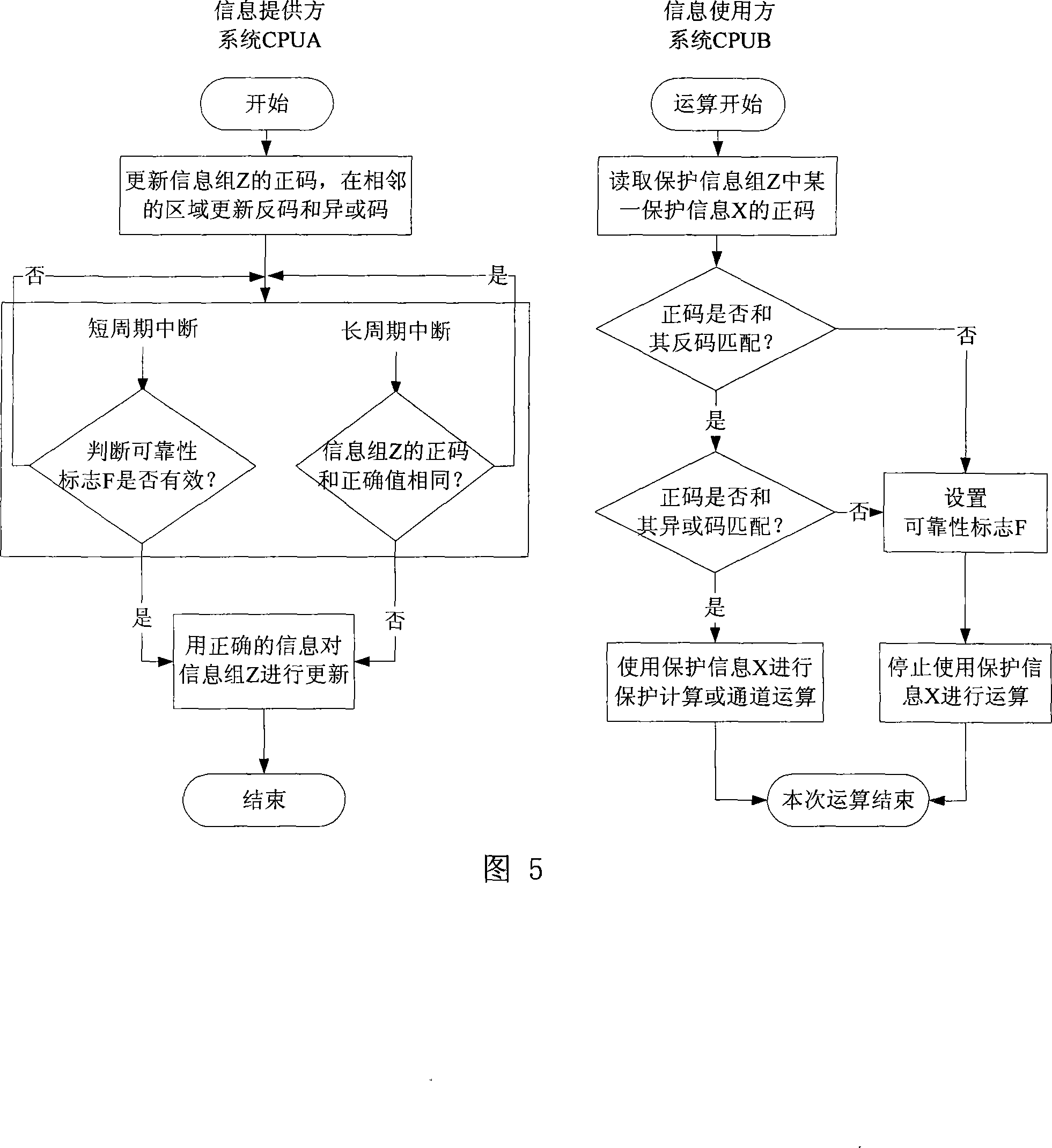
[0027]This embodiment is a technical solution further modified on the basis of the above embodiments, and is used in situations where the real-time performance of protection information is not high and reliability is important. The specific working process is shown in FIG. 5 . When the system starts or the protection information is modified, the system CPUA stores the protection information group Z in the dual-port RAM chip U, and stores its inverse code and XOR code in the adjacent area. When the system CPUB uses any protection information X in the protection information group Z, it checks the protection information X by inverse code and XOR code. If the check is correct, it will continue to run. If the check is incorrect, the system CPUB will Automatically stop using the protection information X, and set the reliability flag F to inform the system CPUA. The system CPUA uses two methods to check the reliability of the protection information group Z during operation: 1. Scan t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More