Method for ciphering wireless mobile terminal communication
A mobile terminal and communication encryption technology, which is applied in the field of information security and communication, can solve the problems of security loopholes, no key update and management mechanism, no cryptographic identity authentication and key management mechanism, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0066] A specific embodiment of the method is given here, and the specific embodiment is as follows.
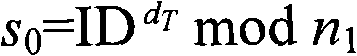
[0067] 1. KGC generates public parameters, and announces the service number and public parameters: KGC selects two prime numbers p and q with at least 5 12 bits, and calculates n=pq, where n is 1024 bits, and KGC generates its own private key d and public key e, satisfying e=d -1 mod(p-1)(q-1), then KGC selects g and the hash function Hash, etc., and g and n are mutually prime.
[0068] KGC publishes public parameters through the website: e, n, g and hash function Hash, etc.
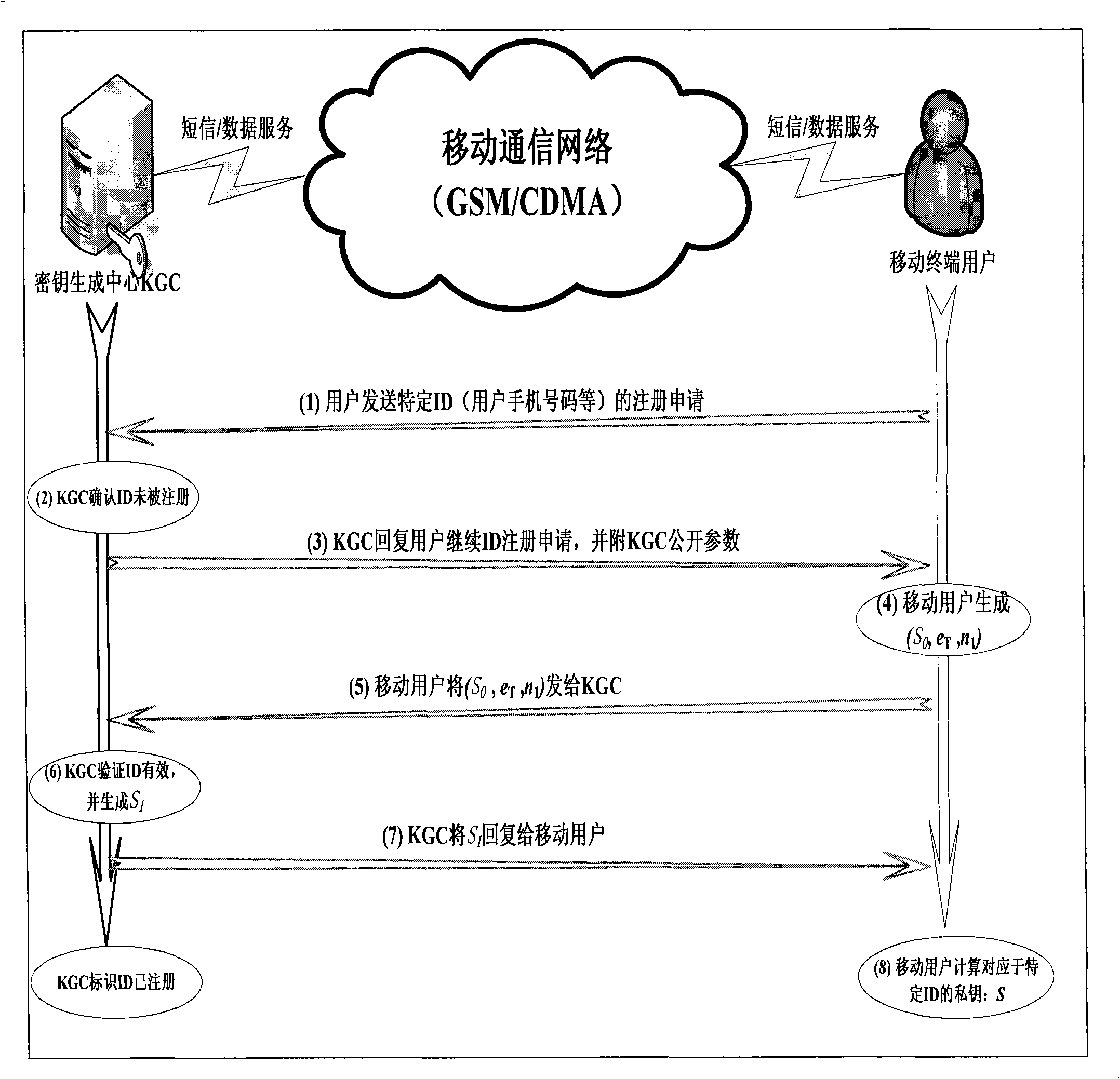
[0069] 2. Mobile user registration and private key acquisition: such as figure 1 As shown, the process of user registration and private key acquisition is as follows, in which the interaction between KGC and mobile users is carried out through SMS:
[0070] (1) The mobile user sends a registration application to KGC through a short message, and the application includes a user identity ID. In this emb...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More