Method, system and equipment for implementing end-to-end encipher of mobile cluster set call
A group call and trunking technology, applied in the field of communication
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0037] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
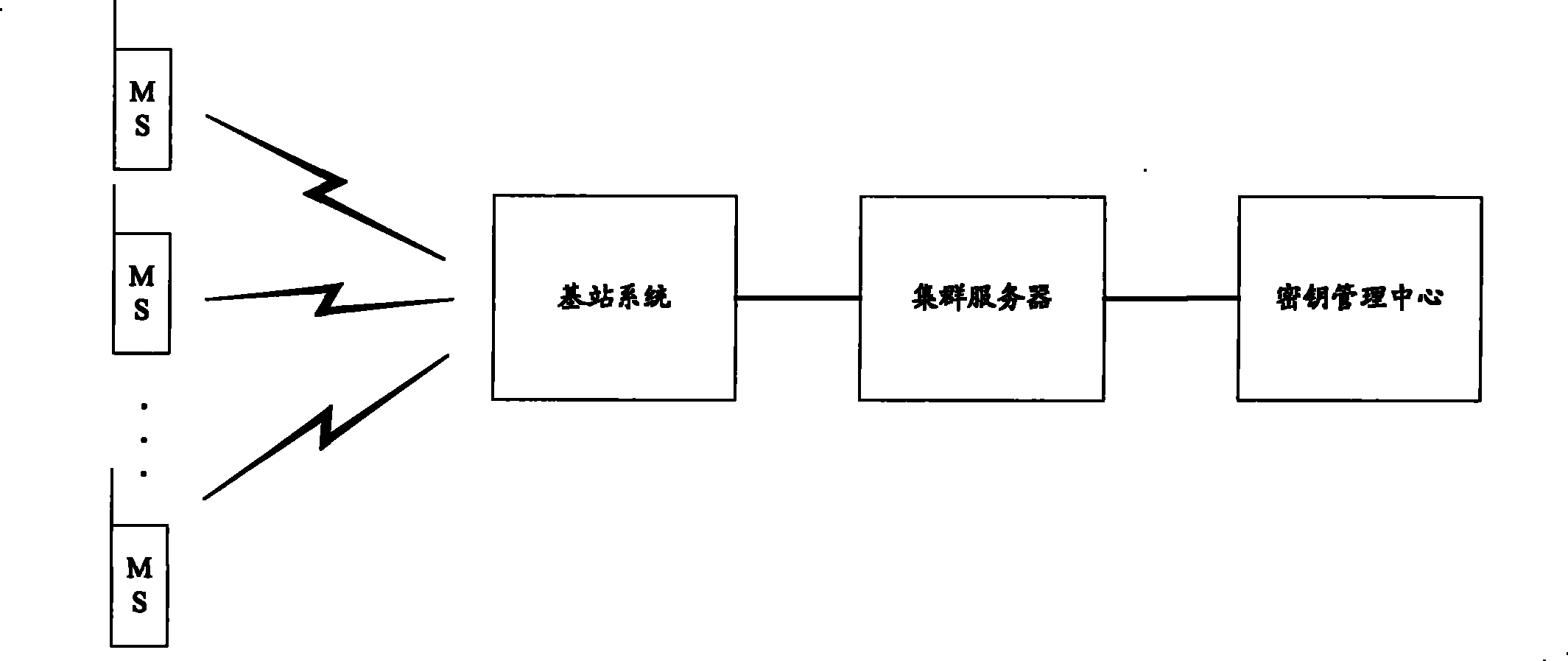
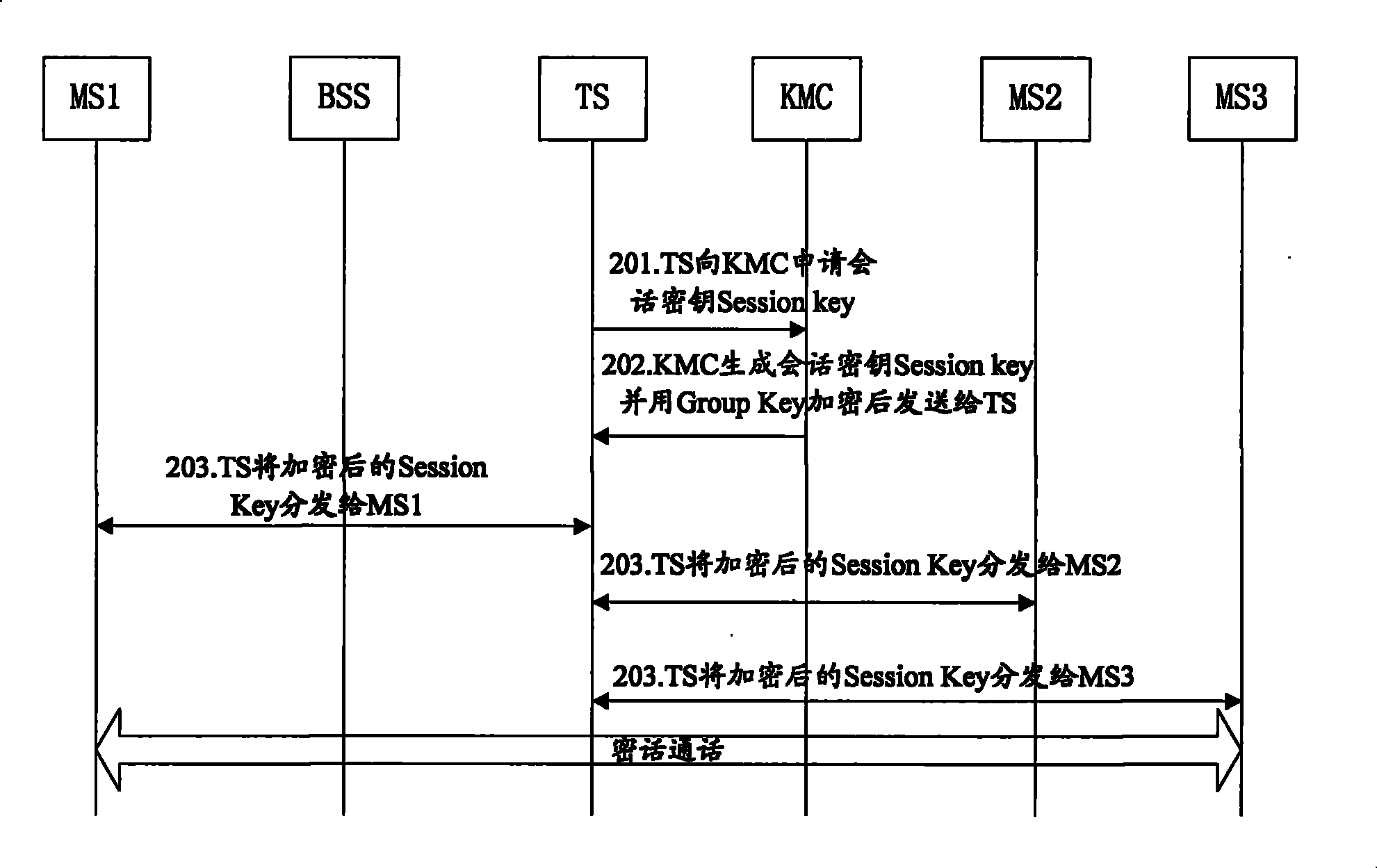
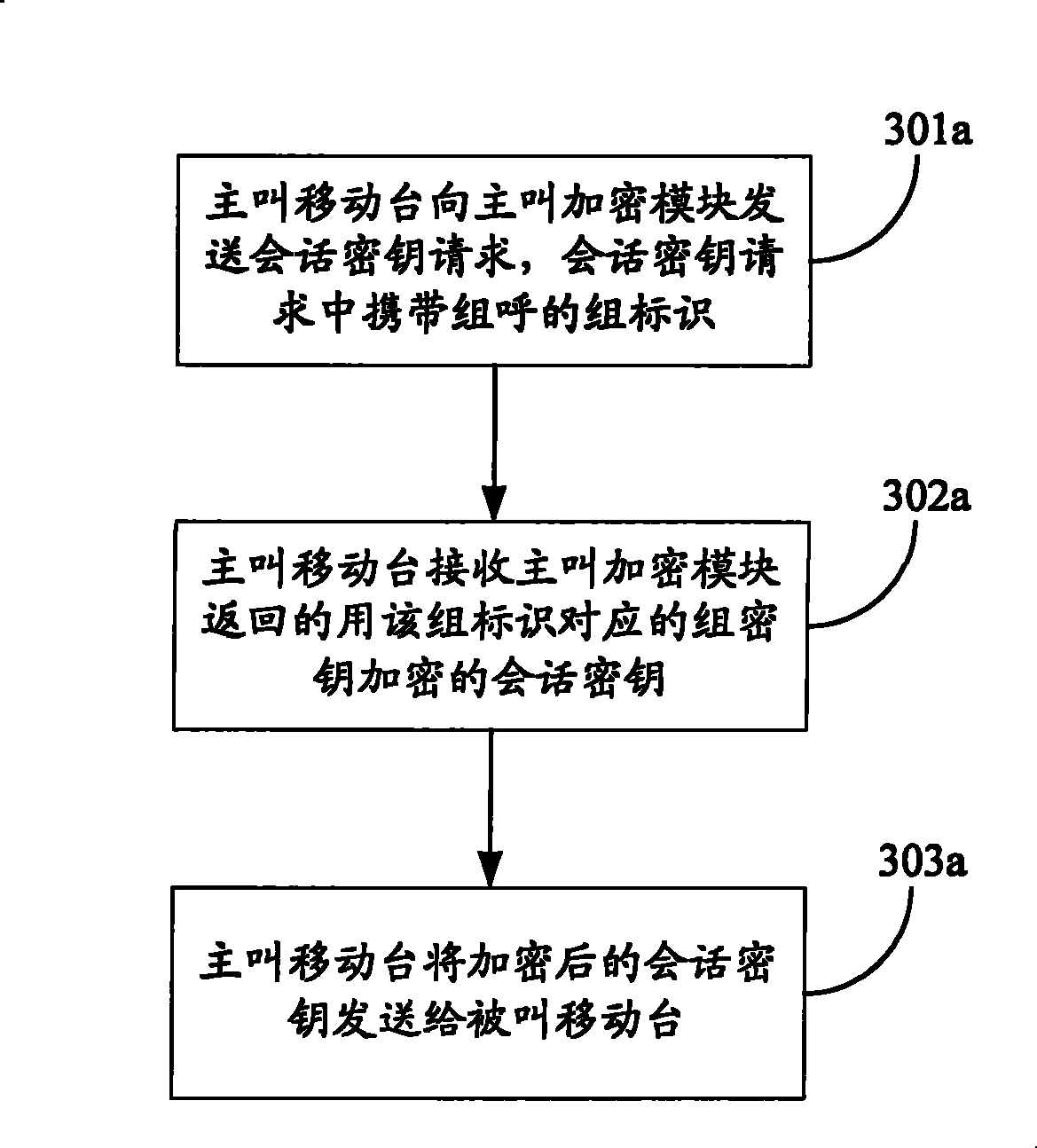
[0038] The embodiment of the present invention discloses an implementation method applied to end-to-end encryption of trunking group calls, which is especially suitable for single-station trunking mode (or failure weakening mode) or KMC failure (or communication interruption between the system and KMC) scenarios End-to-end encryption of trunking group calls. The calling mobile station generates a session key SK (Session Key, session key) through the encryption modu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More