System and method for confirming number of computer rogue program sample families
A malicious program and computer technology, applied in computer security devices, computing, electrical digital data processing, etc., can solve problems such as no commonality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
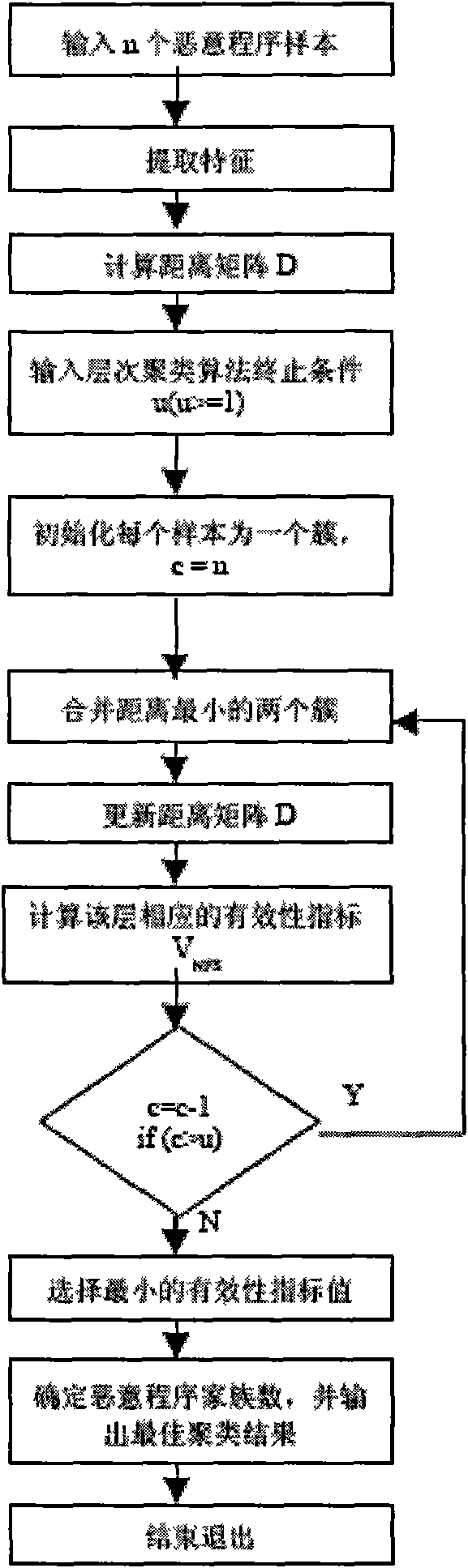
Method used
Image
Examples
Embodiment Construction
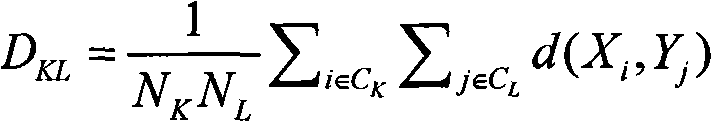
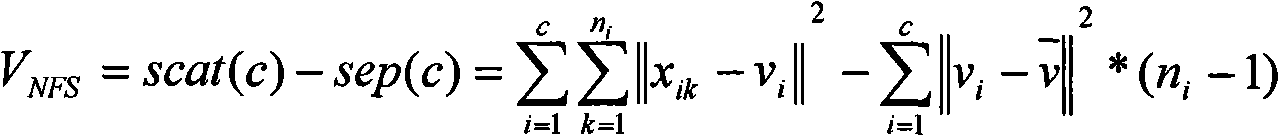
[0036] A system for determining the number of computer malware sample families, including:
[0037] The malicious program sample feature extraction module, which extracts the features of the malicious program samples and calculates the distance between every two malicious program samples through the following malicious program sample distance calculation module to obtain the distance matrix D. The characteristics of malicious program samples can be represented in various ways, such as: byte content based on N-Grams, Windows API sequence, instruction frequency, etc.
[0038] a) N-Grams-based byte content: N-Grams refers to a sequence of n consecutive byte subs in an executable file. For example, the string "text" may consist of the following N-Grams:
[0039] bi-grams: _T, TE, EX, XT, T_
[0040] tri-grams: _TE, TEX, EXT, XT_, T__
[0041] quad-grams: _tEX, TEXT, EXT_, XT__, T___
[0042] After extracting N-Grams, count the frequency of each N-Grams, and use this
[0043] as...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More