System and method for evaluating network safe state
A network security and state assessment technology, applied in the field of information security, can solve problems such as the difficulty of accurately quantifying the threat level of network attack behavior, the inability to make an attack situation, and only considering the number of alarms, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0034] The implementation of the present invention will be described in detail below in conjunction with the accompanying drawings and examples, so as to fully understand and implement the process of how to apply technical means to solve technical problems and achieve technical effects in the present invention.
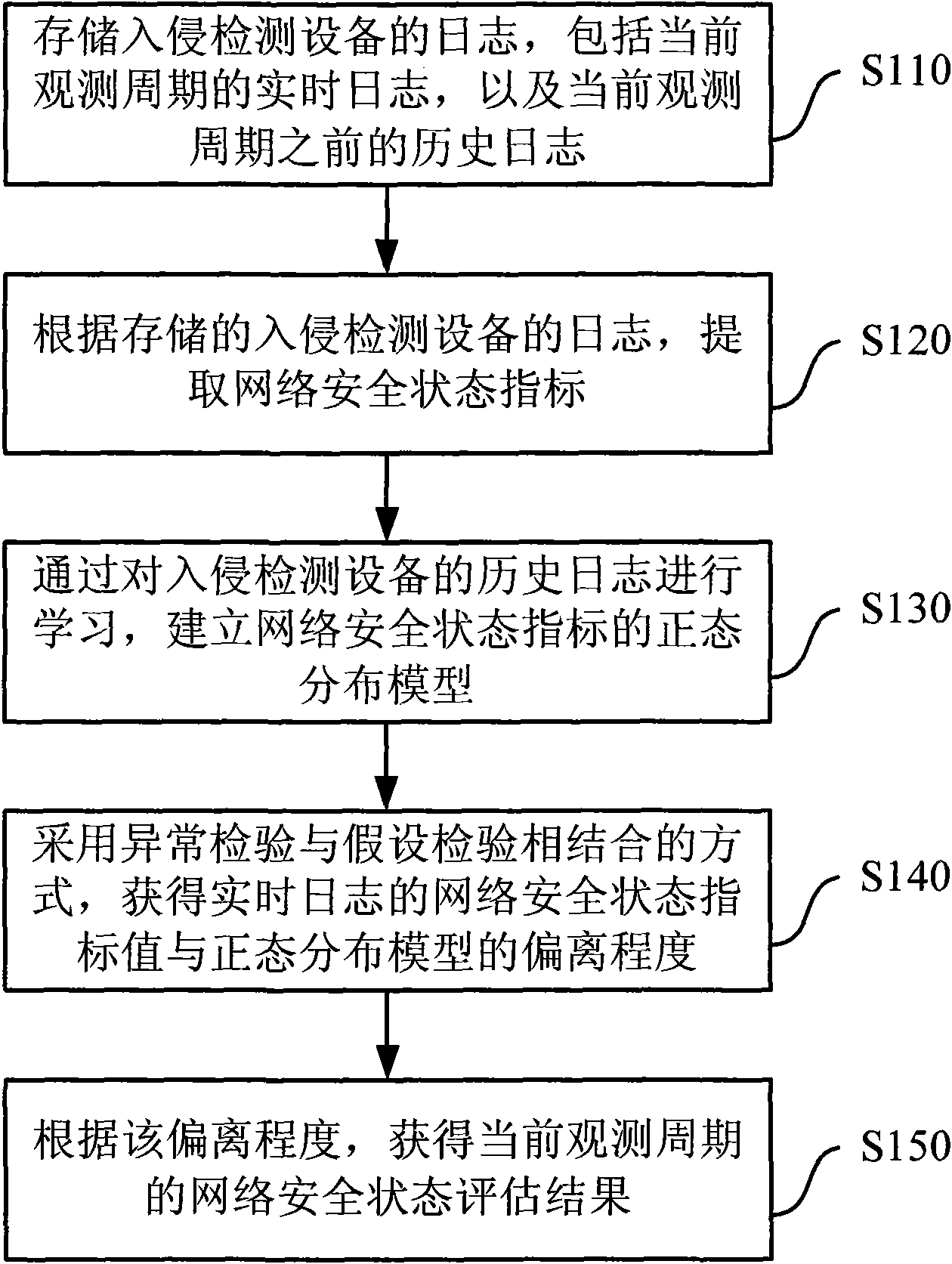
[0035] figure 1 It is a schematic flowchart of an embodiment of a network security state assessment method in the present invention. Such as figure 1 As shown, the method embodiment mainly includes the following steps:
[0036] Step S110, storing the log of the intrusion detection device, including the real-time log of the current observation period, and the historical log before the current observation period;
[0037] Step S120, according to the log of the stored intrusion detection device, extract the network security status indicator, and obtain the network security status indicator value, including the network security status indicator value of the historical l...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More