Method for establishing encrypted/decrypted storage space by virtue of personnel computer external secrete key
A storage space and computer technology, applied in internal/peripheral computer component protection, digital data protection, etc., can solve problems such as not providing users with encryption/decryption operation interface
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0072] Further details will be given below in conjunction with various embodiments shown in the accompanying drawings.
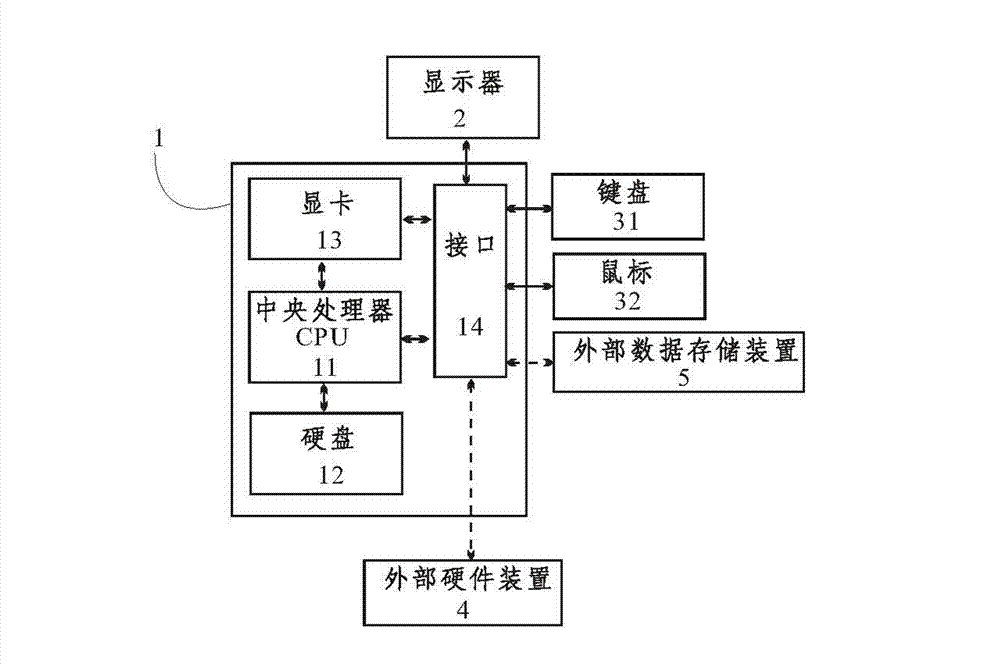
[0073] The present invention proposes a method for establishing an encryption / decryption storage space by means of a peripheral key of a personal computer, such as figure 1 As shown, the method is based on a personal computer, and an external hardware device 4 that is independent of the personal computer and has storage capacity; the personal computer includes a host 1, an input device and an output device, and a central A processor CPU 11, and a hard disk 12 storing an operating system and data therein. In the first embodiment of the present invention, the input devices are a keyboard 31 and a mouse 32 , which are electrically connected to the host 1 through the interface 14 . The output device adopts a display screen 2, which is electrically connected to the graphics card 13 in the host computer 1 through an interface, and the graphics card 13 completes d...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More