Security management method for database information
A management method and database technology, applied in the fields of digital data protection, user identity/authority verification, electrical components, etc., can solve the problems of neglecting information data security, information leakage, database system crash, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
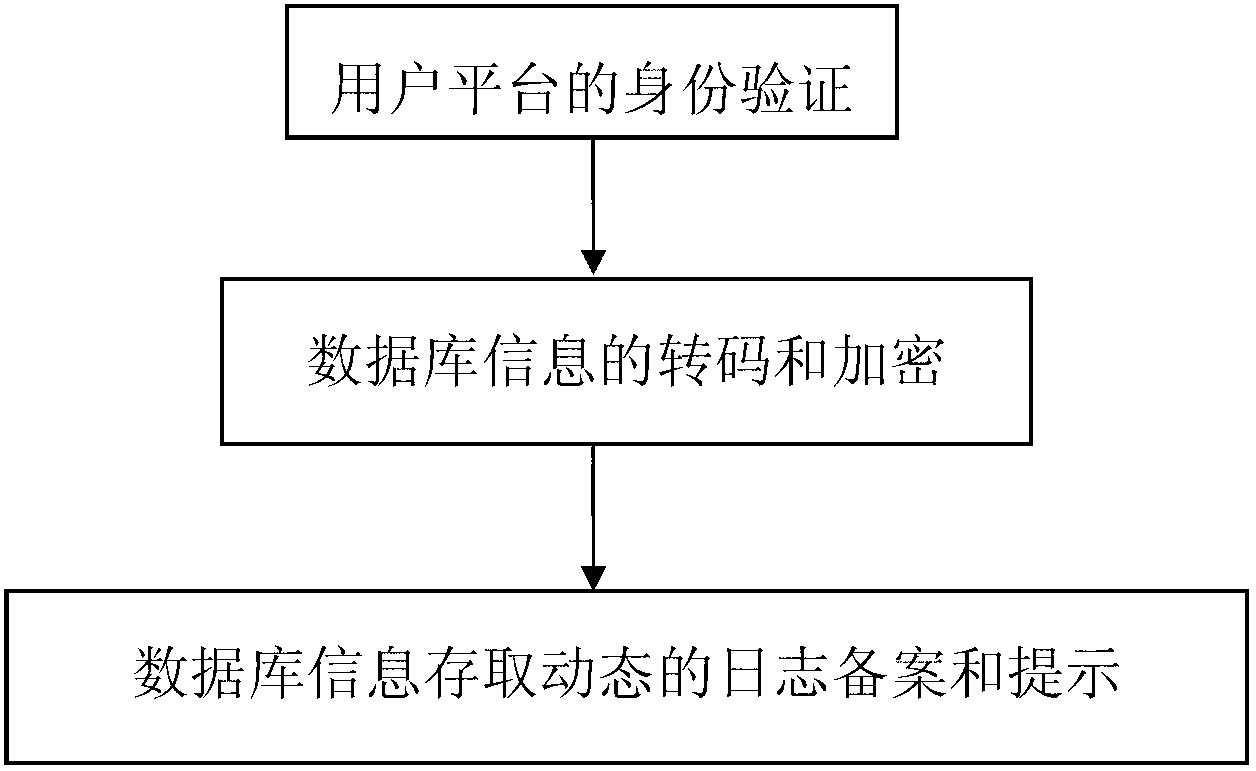
[0008] according to figure 1 , the concrete implementation method step of the inventive method is:
[0009] 1. Identity verification of the user platform; 2. Transcoding and encryption of database information; 3. Dynamic log filing and prompting of database information access.
[0010] In the step of user platform identity verification, the user logs in to the home page of the security management system through the account, and the system analyzes and classifies the user level. The content opened on the home page is the system operating platform corresponding to the user level, so that the database information can be effectively processed. Effectively hidden. In the steps of transcoding and encryption of database information, the software development team designs a database transcoding storage software with limited authority. This software classifies, transcodes, stores, and encrypts the uploaded user information. The code is transcoded according to a set of code books compi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More