Encryption method and?device
An encryption method and ciphertext technology, applied in the field of information security and encryption, can solve problems such as no solution, inability to meet performance, etc., and achieve the effect of high speed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in combination with specific embodiments and with reference to the accompanying drawings. It should be understood that these descriptions are exemplary only, and are not intended to limit the scope of the present invention. The embodiments in the present application and the features in the embodiments can be combined with each other. Also, in the following description, descriptions of well-known structures and techniques are omitted to avoid unnecessarily obscuring the concept of the present invention.
[0042] The present invention proposes a Character Based Bidirection Cyclic Replacement (Character Based Bidirection Cyclic Replacement) encryption method and a corresponding decryption method. They are respectively described as follows.
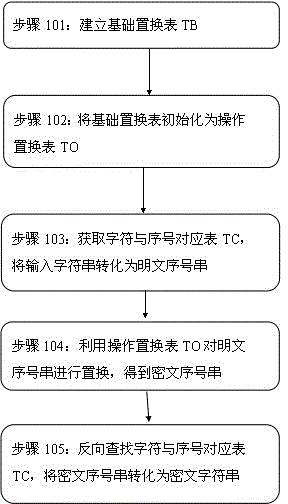
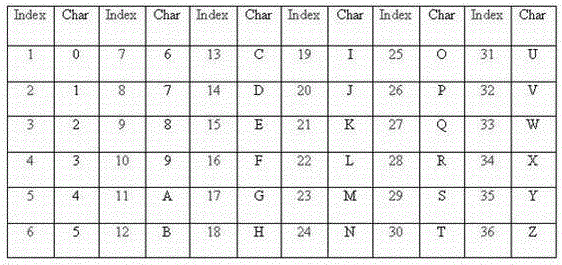
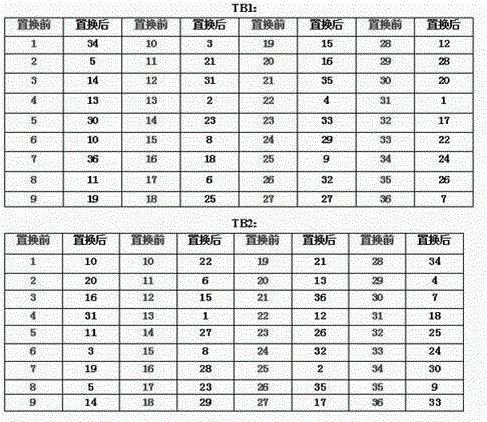
[0043] figure 1 is a flowchart of an encryption method according to an ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More