Novel low-resource efficient lightweight Surge block cipher implementation method
A technology of a block cipher and an implementation method, applied in the direction of encryption devices with shift registers/memory, etc., can solve the problems of low efficiency, high resource occupation, low encryption performance, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0061] The present invention will be further described below in conjunction with the accompanying drawings and embodiments.
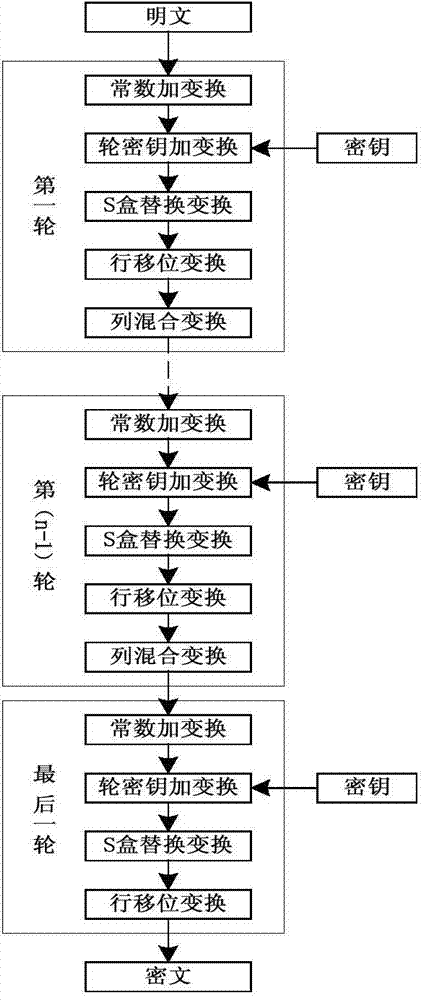
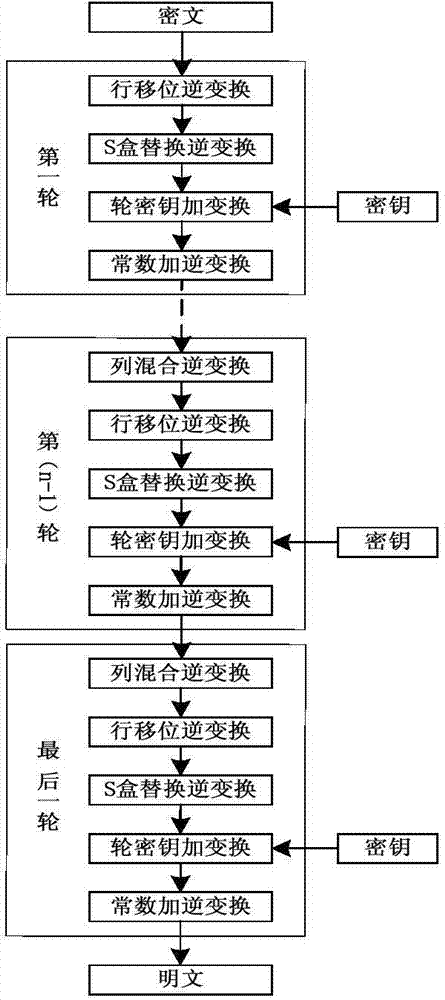
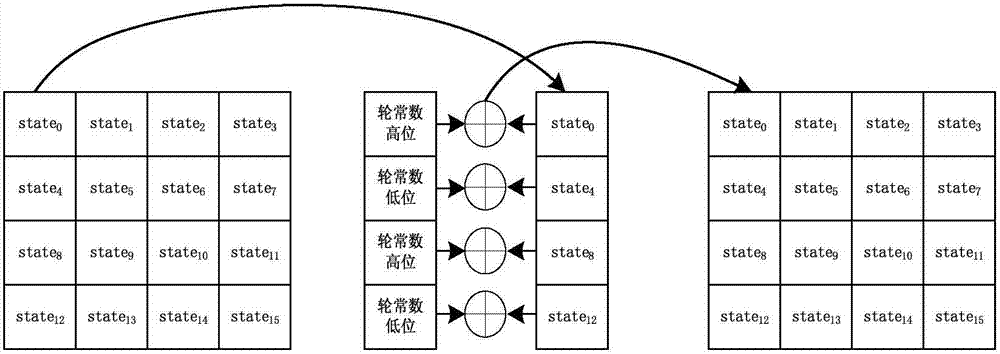
[0062] The implementation method of the Surge block cipher adopts the SPN structure, the block length is 64-bit, and the key length is designed to be 64-bit, 80-bit, and 128-bit, which are respectively recorded as Surge-64, Surge-80, and Surge-128 . Surge-64, Surge-80 and Surge-128 iteration rounds N R They are 32 rounds, 36 rounds and 40 rounds respectively. Surge encryption operation process is as follows: figure 1 As shown, the encryption round operation includes five modules: constant plus transformation (AddConstants), round key plus transformation (AddRoundKey), S-box replacement transformation (SubCells), row shift transformation (ShiftRows), and column mix transformation (MixColumns). The decryption operation flow is as follows figure 2 , the algorithm decryption round operation includes column mixing inverse transformation (InvMixColumns),...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More