An intrusion detection method for network data in xen virtualization environment
A virtualization environment and intrusion detection technology, which is applied in the field of intrusion detection of network data in a Xen virtualization environment, can solve problems such as inability to defend against intrusion of network data, inability to obtain network data of virtual machine devices, etc., and achieve the effect of filtering
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] In order to better understand the technical problems solved by the present invention and the technical solutions provided, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. The specific embodiments described here are only used to explain the implementation of the present invention, but not to limit the present invention.
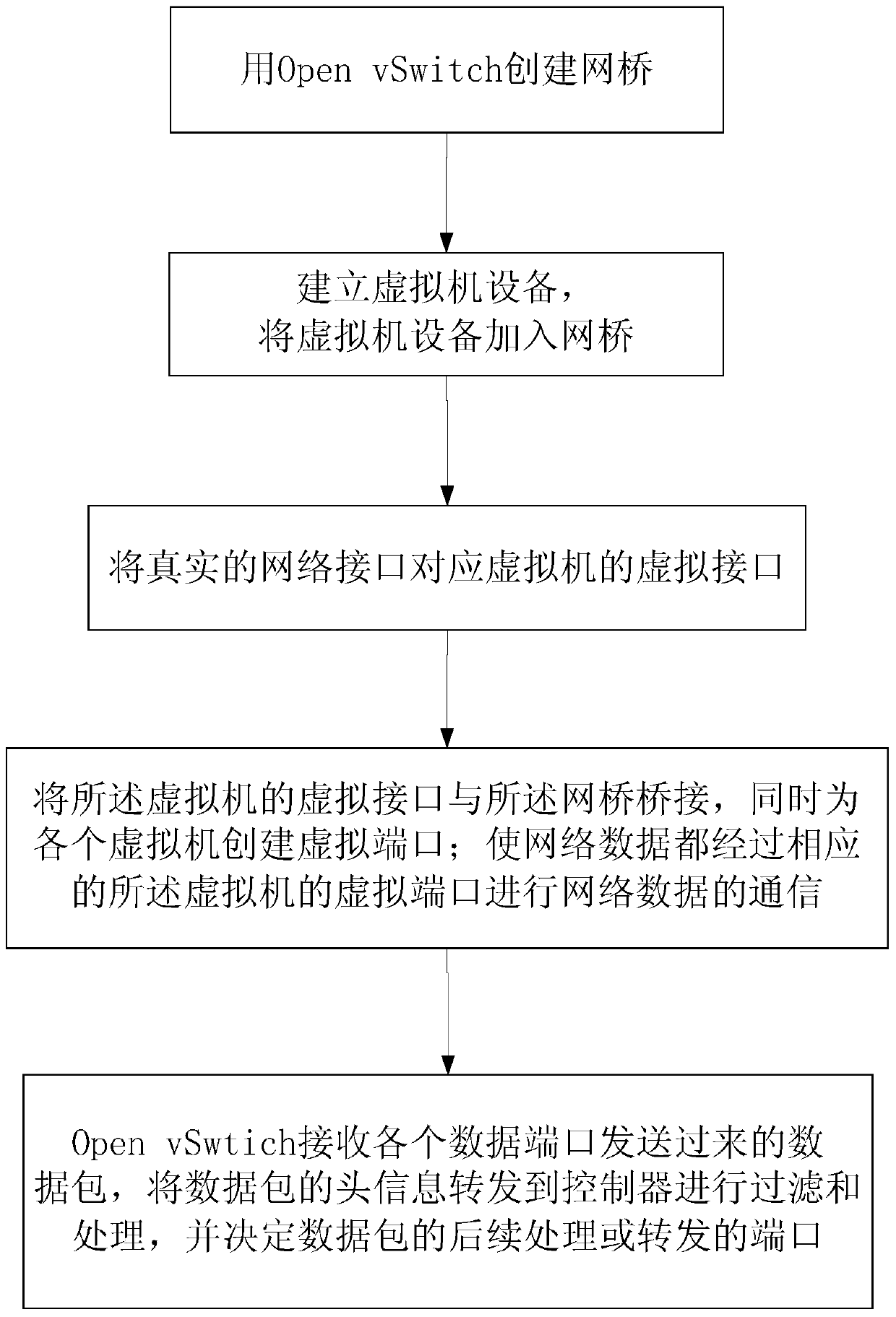
[0034] In a preferred embodiment, figure 1 It exemplarily shows a schematic flowchart of an intrusion detection method for network data in a Xen virtualization environment; including: .
[0035] Step 1: On the host machine, use Open vSwitch to build a network architecture and create a bridge;
[0036] Step 2: Establish a virtual machine device, and add the virtual machine device to the network bridge;
[0037] Step 3: Match the real network interface to the virtual interface of the virtual machine device, and keep the correspondence between the real network interface and th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More