Safety login method based on domestic cryptographic algorithm
A technology of secure login and national secret algorithm, applied in the field of secure login of network equipment, can solve problems such as major security risks, and achieve the effect of improving security, preventing illegal attacks, and being highly portable.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
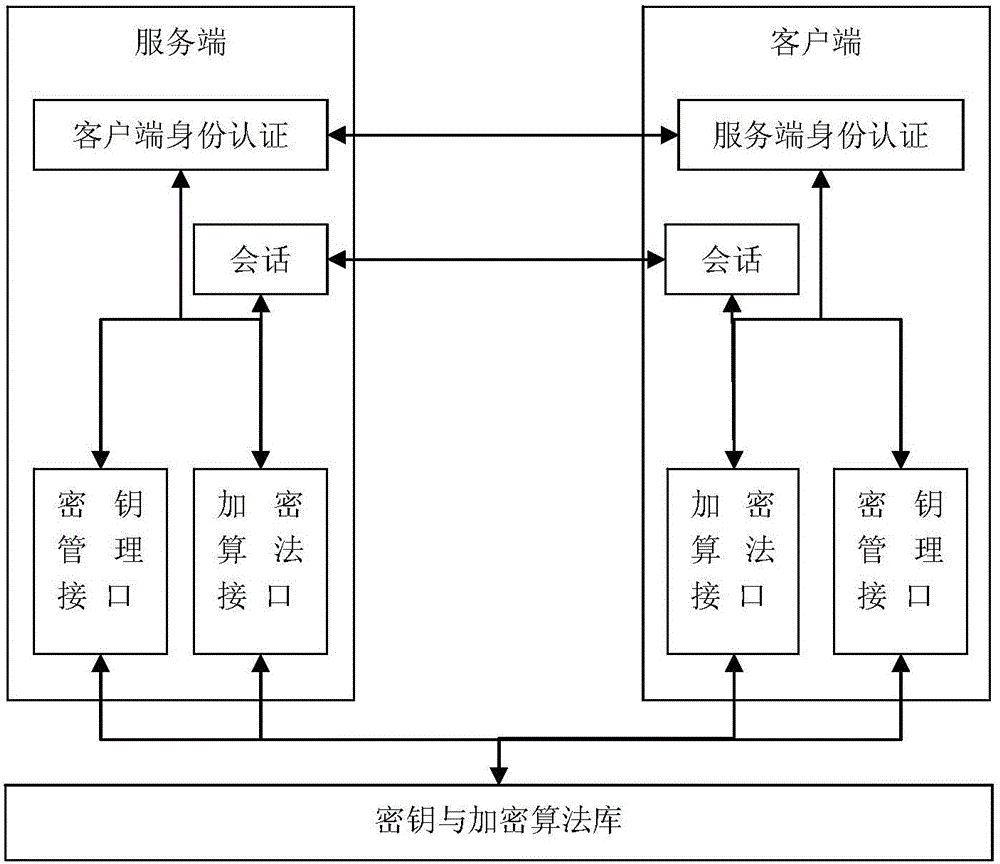
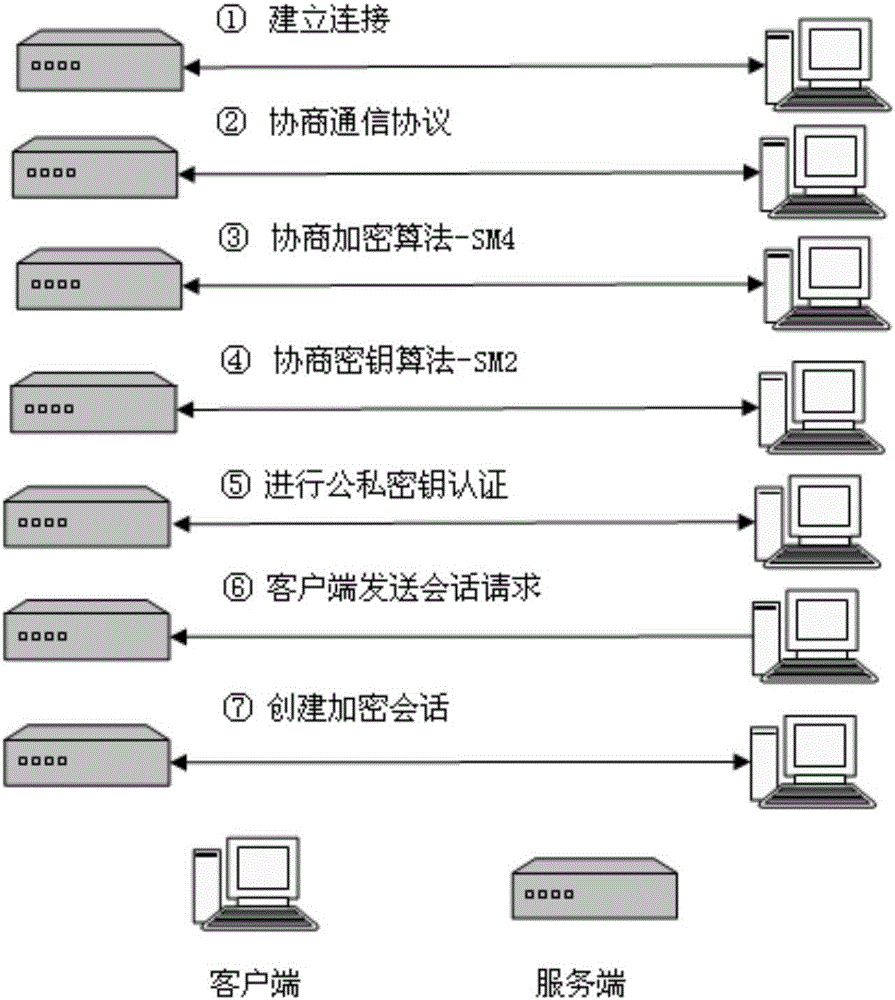
[0015] A secure login method based on the national secret algorithm. The device login software consists of two parts, the server and the client, which are installed on the embedded device and the debugging machine computer respectively, and the device and the computer are connected through the network port. The client logs in to the device remotely through the network, shielding the password authentication method with high security risks, and the software adopts the key verification method, and the user can log in to the device only after the client and server keys pass their respective verifications. Among them, the core key agreement and communication encryption are completely implemented based on the National Secret Algorithm.
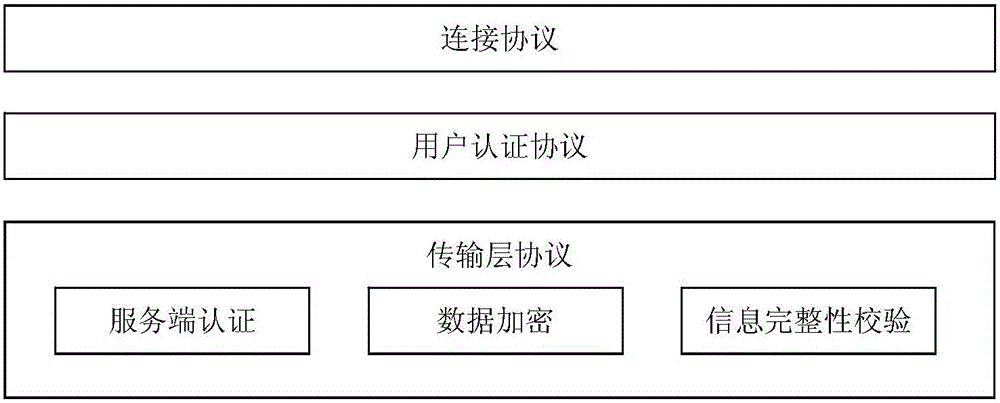
[0016] Such as figure 1 As shown, the communication protocol framework of secure remote login: Transport Layer Protocol (TransportLayerProtocol) provides server authentication, transmission data encryption and data integrity verification; User Authe...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More