Route origin and path two-factor authentication method
A double verification, routing source technology, applied in the network field, can solve the problems of high network performance pressure of network equipment, and achieve the effect of reducing the verification process and improving the processing flow and efficiency.
Active Publication Date: 2016-03-02
CHINA INTERNET NETWORK INFORMATION CENTER
View PDF2 Cites 18 Cited by
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
[0026] However, since the INR route authorization verification mechanism and the BGPSEC technology are implemented at the same time, there will be a lot of pressure on network equipment changes and network performance. Therefore, there is currently no solution that can simultaneously perform BGP route source verification and BGP route path verification.
Method used
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
View moreImage
Smart Image Click on the blue labels to locate them in the text.
Smart ImageViewing Examples
Examples
Experimental program
Comparison scheme
Effect test
Embodiment 1
[0074] Embodiment 1: The value of ROA can be embedded into the path attribute.
Embodiment 2
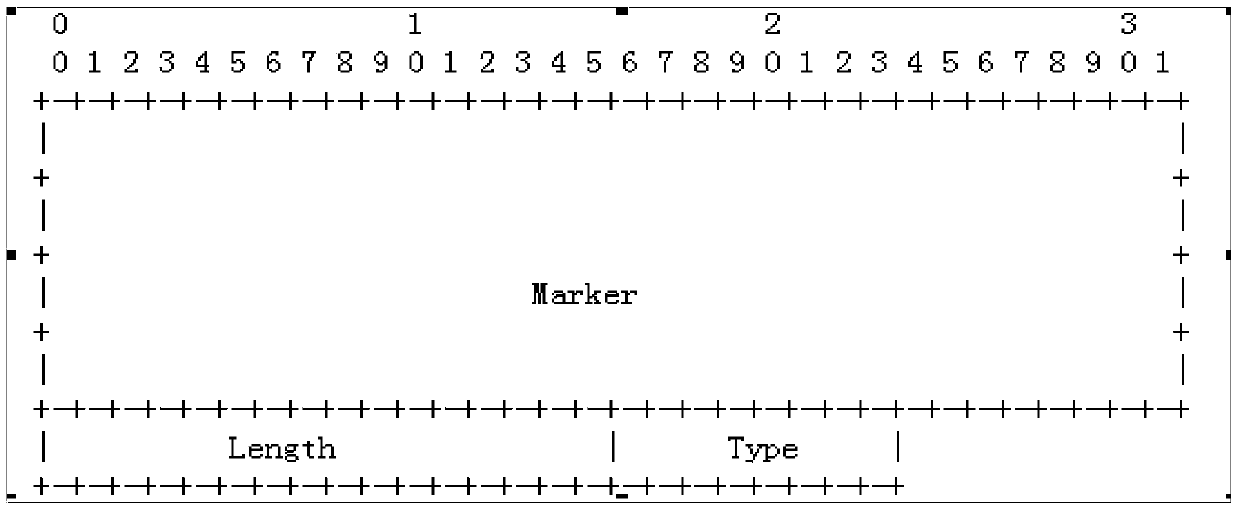
[0075] Embodiment 2: The BGP message can be extended, and a new option is added behind the network layer reachability information, which is used to store the value of ROA. The specific format is as follows:
[0076]
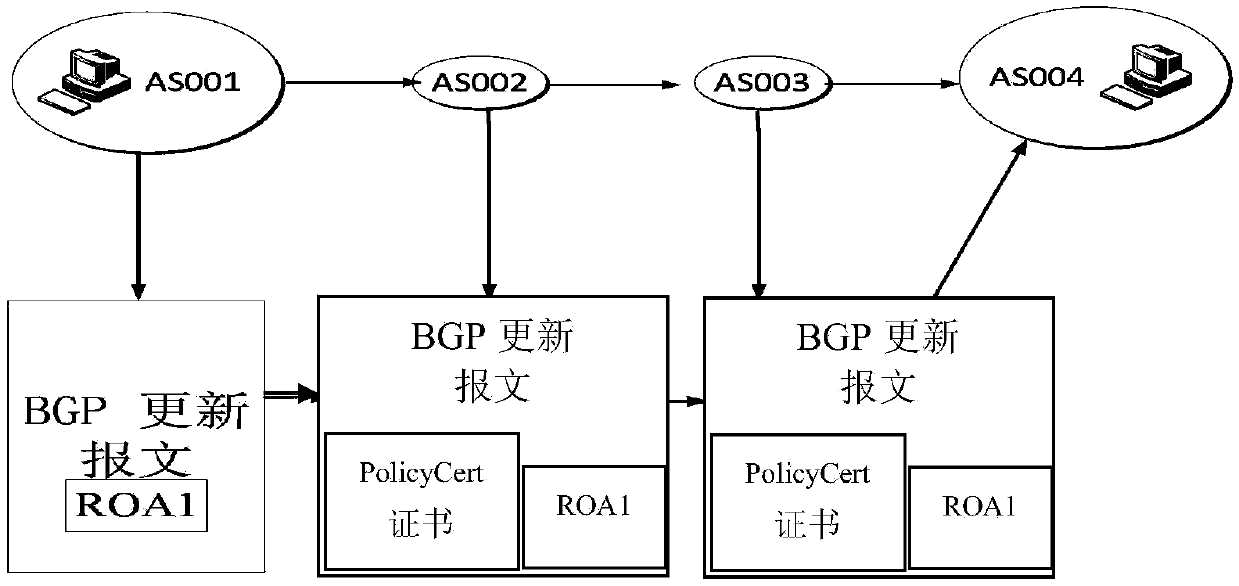
[0077] 1) The originating router sends update+roa;
[0078] 2) The second hop uses ROA to verify UPDATE;
[0079] Y: Forward update, no ROA is required, plus policycert;
[0080] N: Discard;
[0081] 3) The next-hop router directly trusts the previous hop;
[0082] Path validation is based on policycert.
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More PUM
 Login to View More
Login to View More Abstract
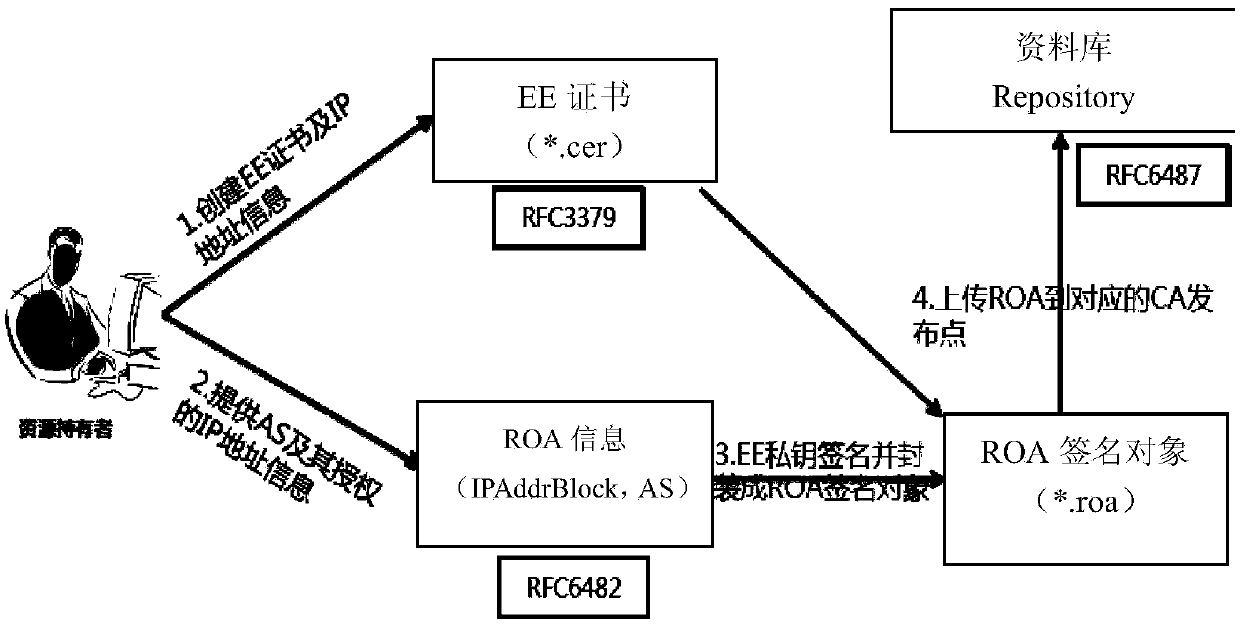
The invention discloses a route origin and path two-factor authentication method. The method comprises the following steps that: (1) a source autonomous system AS<1> embeds a route origin authorization (ROA) certificate of the autonomous system AS<1> into a border gateway protocol (BGP) route update message, and sends the update message to a next-hop autonomous system AS<2>; (2) the autonomous system AS<2> verifies the ROA certificate of the AS<1>, and issues a certificate ASPolicyCert, signs the issued certificate ASPolicyCert with a private key, embeds the signed certificate ASPolicyCert into a BGP route update message of the AS<2>, and sends the update message to a next-hop autonomous system AS after a route origin being the AS<1> is verified; and (3) after reception of the update message sent by a last-hop autonomous system, each autonomous system AS acquires the ROA certificate of the AS<1> from the update message, issues a certificate and signs the certificate after the route origin being the AS<1> and a routing path being correct are verified, embeds the certificate into a BGP route update message of the AS, and sends the update message to a next-hop autonomous system till a destination autonomous system AS.
Description
technical field [0001] The invention relates to a method for realizing double authentication of routing source authentication and path authentication, and belongs to the field of network technology. Background technique [0002] As an important infrastructure to ensure Internet interconnection, the inter-domain routing system has a vital impact on the security and stability of the Internet. Because the BGP protocol adopted by the traditional inter-domain routing system lacks the verification of the authenticity of the routing advertisement content, deliberate attacks by hackers and wrong network parameter configurations may lead to route hijacking. Route hijacking has a great impact on the normal operation of the Internet, and may cause a large area of network paralysis. Typical router hijacking incidents that have been reported in the newspapers include: the AS7007 incident in April 1997, the Turkey TTNet router hijacking incident in December 2004, the Con-Edison router ...
Claims
the structure of the environmentally friendly knitted fabric provided by the present invention; figure 2 Flow chart of the yarn wrapping machine for environmentally friendly knitted fabrics and storage devices; image 3 Is the parameter map of the yarn covering machine
Login to View More Application Information
Patent Timeline
 Login to View More
Login to View More Patent Type & Authority Applications(China)
IPC IPC(8): H04L12/24H04L9/32H04L9/30H04L12/715H04L12/771H04L45/60
Inventor 李晓东傅瑜延志伟王翠翠
Owner CHINA INTERNET NETWORK INFORMATION CENTER