Method for generating secret or secret key in network
A secret, network technology, applied in the field of cryptographic keys, which can solve problems such as inefficiency and high computational complexity of asymmetric methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
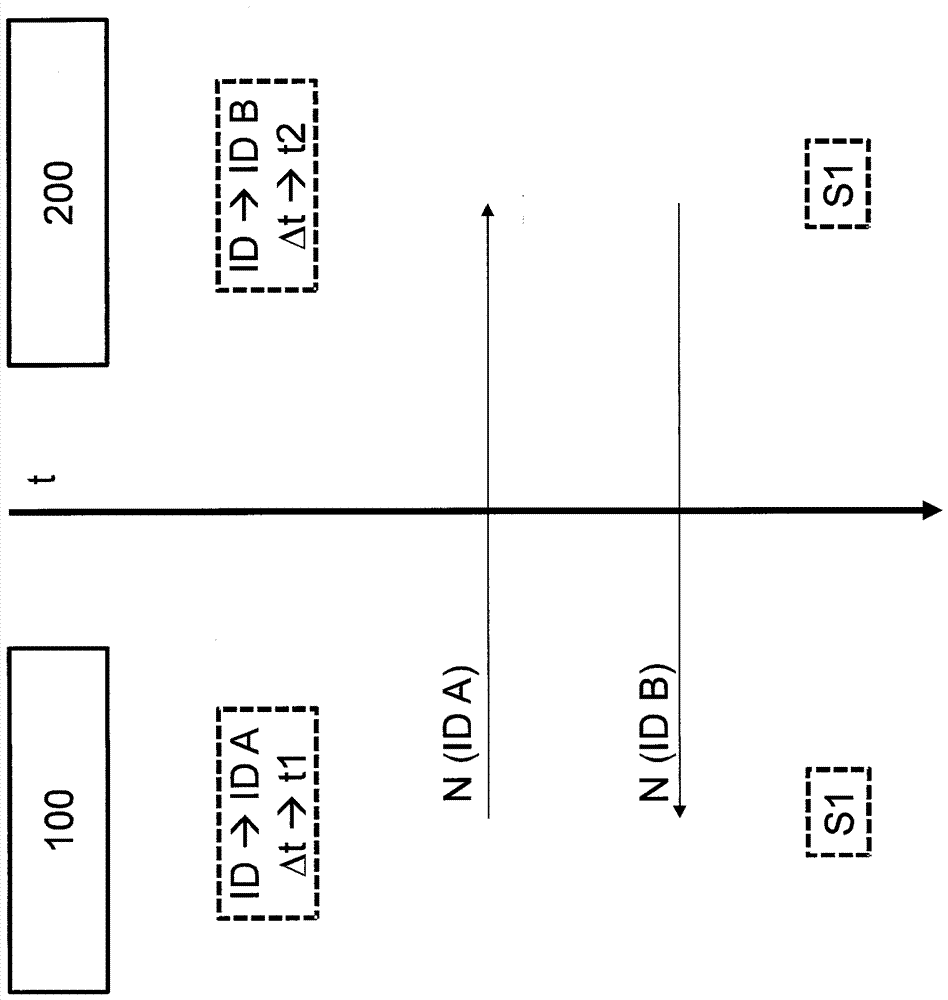
[0023] The invention relates to a method for generating a secret, such as a (secret) symmetric cryptographic key, between two nodes (users of a network) of a communication system via a commonly used medium (transmission channel of the network) communicate with each other. In this case, the generation or negotiation of a secret, in particular a cryptographic key, is based on a public data exchange between two users, wherein however a possible eavesdropping third party as an attacker is still unable or only very difficult to deduce the generated key .
[0024] With the invention it is therefore possible to establish completely automated and secure corresponding symmetric cryptographic keys between two different users of the network, in order to then implement certain security functions, such as data encryption, on the basis of this. As will be described in more detail, first a common secret is established for this purpose, which can be used for key generation. In principle, ho...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More