Secure mutual authentication and key agreement protocol under Internet of Things environment
A technology of key negotiation and two-party authentication, applied to the public key of secure communication, secure communication device, and key distribution, it can solve problems such as low efficiency and dictionary attack, and achieve high performance and efficiency, high security The effect of reducing security risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
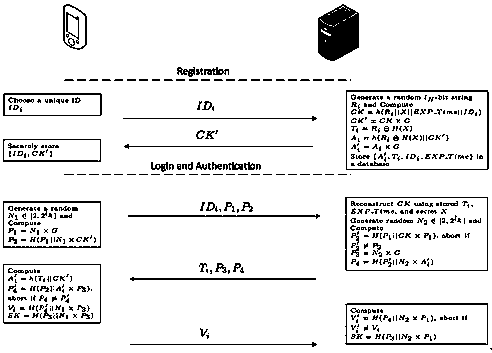
[0025] Such as figure 1 As shown, a three-party password authentication and key agreement protocol based on a highly reliable smart card includes the following steps:
[0026] A. Registration stage: user to the server submit your own Information, registered as a legal user.
[0027] A1: User own sent to the server via a secure channel .
[0028] A2: server received by user After sending the message, choose a random number and key expiration time , and then use the private key calculate: , , , , . server storage to the database, and will send to user .
[0029] A3: User store received and own to the database.
[0030...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More