Multi-mechanism encryption method used in lattices for supporting strategy hiding
An encryption method and multi-institutional technology, applied in the cloud environment and cryptography, can solve the problems of not meeting application requirements and low security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0041] The present invention will be further elaborated below by describing a preferred specific embodiment in detail in conjunction with the accompanying drawings.
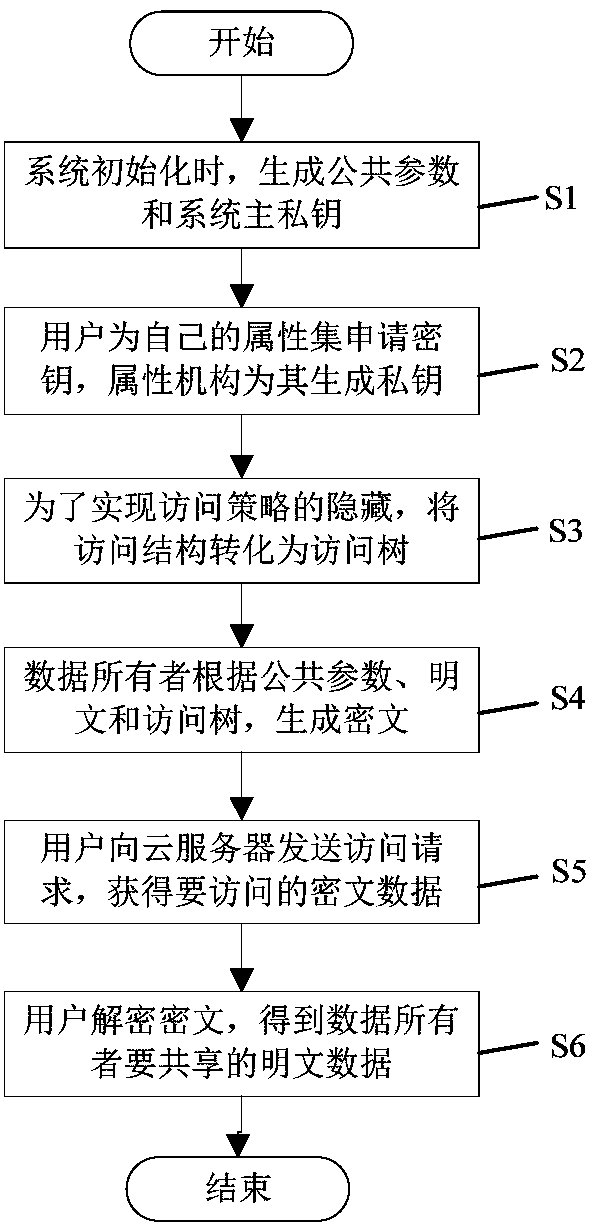
[0042] like figure 1 As shown, the present invention discloses a multi-mechanism encryption method that supports policy hiding on a grid, which includes the following steps: S1, when the system is initialized, generate public parameters and system master private keys; S2, users apply for encryption for their own attribute sets key, the attribute organization generates a private key according to the public parameters, the system master private key and the user's attribute set; S3, transform the access structure into a corresponding access tree to realize the complete hiding of the access policy; S4, the data owner according to the Parameters, plaintext and converted access tree, generate ciphertext data, and then upload it to the cloud server for storage; S5, the user sends an access request to the cloud server, a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More