Boundary intrusion detection method, device, server and system
A border intrusion and detection method technology, applied to instruments, alarms, anti-theft alarms, etc., can solve problems such as false alarms, difficult installation and implementation, and high investment costs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
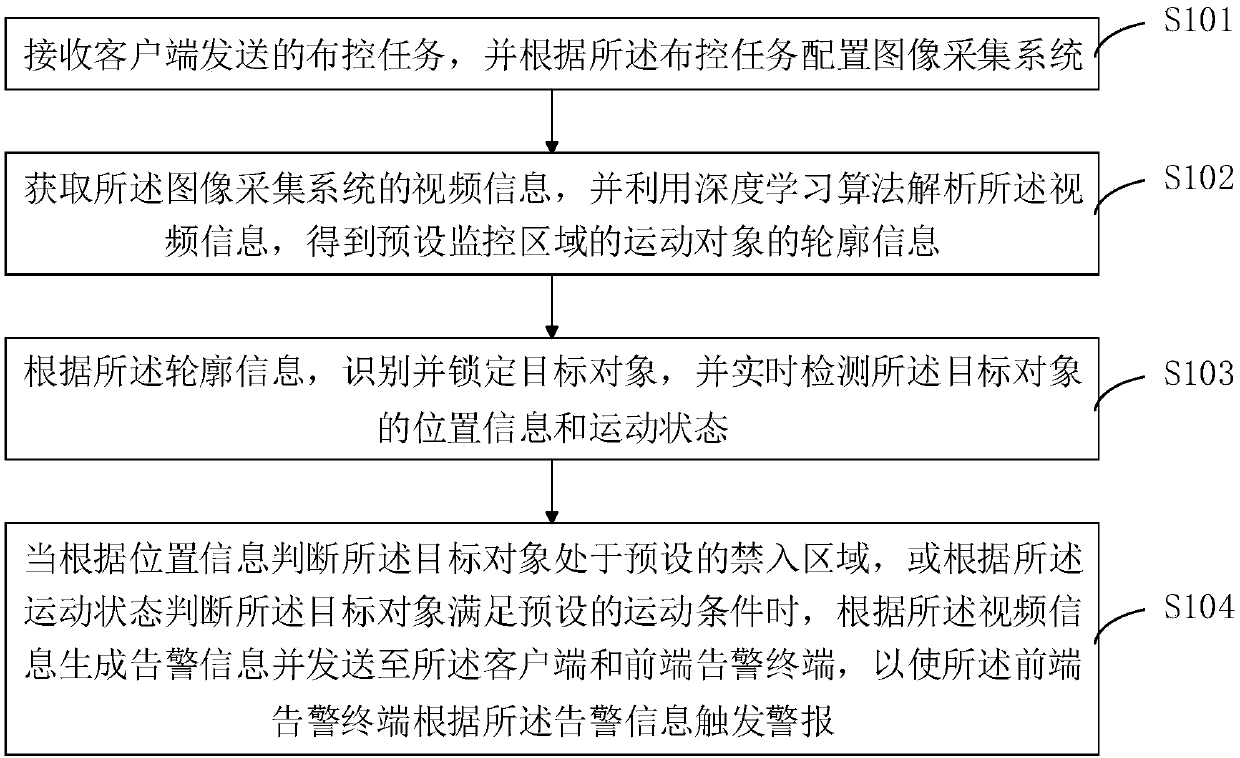
[0045] see figure 1 , figure 1is a schematic flowchart of the border intrusion detection method provided by the first embodiment of the present invention.
[0046] The border intrusion detection method comprises the steps of:
[0047] S101. Receive a deployment and control task sent by a client, and configure an image acquisition system according to the deployment and control task.
[0048] In this example, if figure 2 as shown, figure 2 It is a schematic diagram of the architecture of the security system in the first embodiment of the present invention. Implementing the boundary intrusion detection method requires devices such as a client 201, a server 202 (the server includes a background management server 2021 and a video analysis server 2022), an image acquisition system 203, and a front-end alarm terminal 204. Wherein, the image acquisition system includes at least one camera 2031 and a switch 2032 corresponding to the camera 2031 . The client 201 sets the monitor...
no. 2 example
[0063] see image 3 , image 3 is a schematic structural diagram of a border intrusion detection device provided by the second embodiment of the present invention.
[0064] The border intrusion detection device includes:
[0065] The deployment and control unit 301 is configured to receive the deployment and control task sent by the client, and configure the image acquisition system according to the deployment and control task.
[0066] The video information analysis unit 302 is configured to acquire the video information of the image acquisition system, and use a deep learning algorithm to analyze the video information to obtain the contour information of the moving object in the preset monitoring area.
[0067] The target object locking unit 303 is configured to identify and lock the target object according to the outline information, and detect the position information and motion state of the target object in real time.
[0068] The intrusion judging unit 304 is configur...
Embodiment 3
[0077] This embodiment provides a boundary intrusion detection system, including: a client, a server, an image acquisition system, and a front-end alarm terminal.
[0078] The client is configured to send deployment and control tasks to the server.
[0079] The server end is configured to configure the image acquisition system according to the deployment and control task.
[0080] The image collection system is used to collect video information of a preset monitoring area.
[0081] In this example, if figure 2 as shown, figure 2 It is a schematic diagram of the architecture of the security system in the first embodiment of the present invention. Implementing the boundary intrusion detection method requires devices such as a client 201, a server 202 (the server includes a background management server 2021 and a video analysis server 2022), an image acquisition system 203, and a front-end alarm terminal 204. Wherein, the image acquisition system includes at least one camer...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More