Database access control method and device based on public key verification and electronic equipment
An access control and database technology, applied in the field of computer technology and cryptography, can solve problems such as user information leakage, and achieve the effect of avoiding data leakage, improving accuracy, and improving data security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] Embodiments of the present invention will be described below with reference to the accompanying drawings. Those skilled in the art would recognize that the described embodiments can be modified in various ways or combinations thereof without departing from the spirit and scope of the invention. Accordingly, the drawings and description are illustrative in nature and not intended to limit the scope of the claims. Also, in this specification, the drawings are not drawn to scale, and like reference numerals denote like parts.
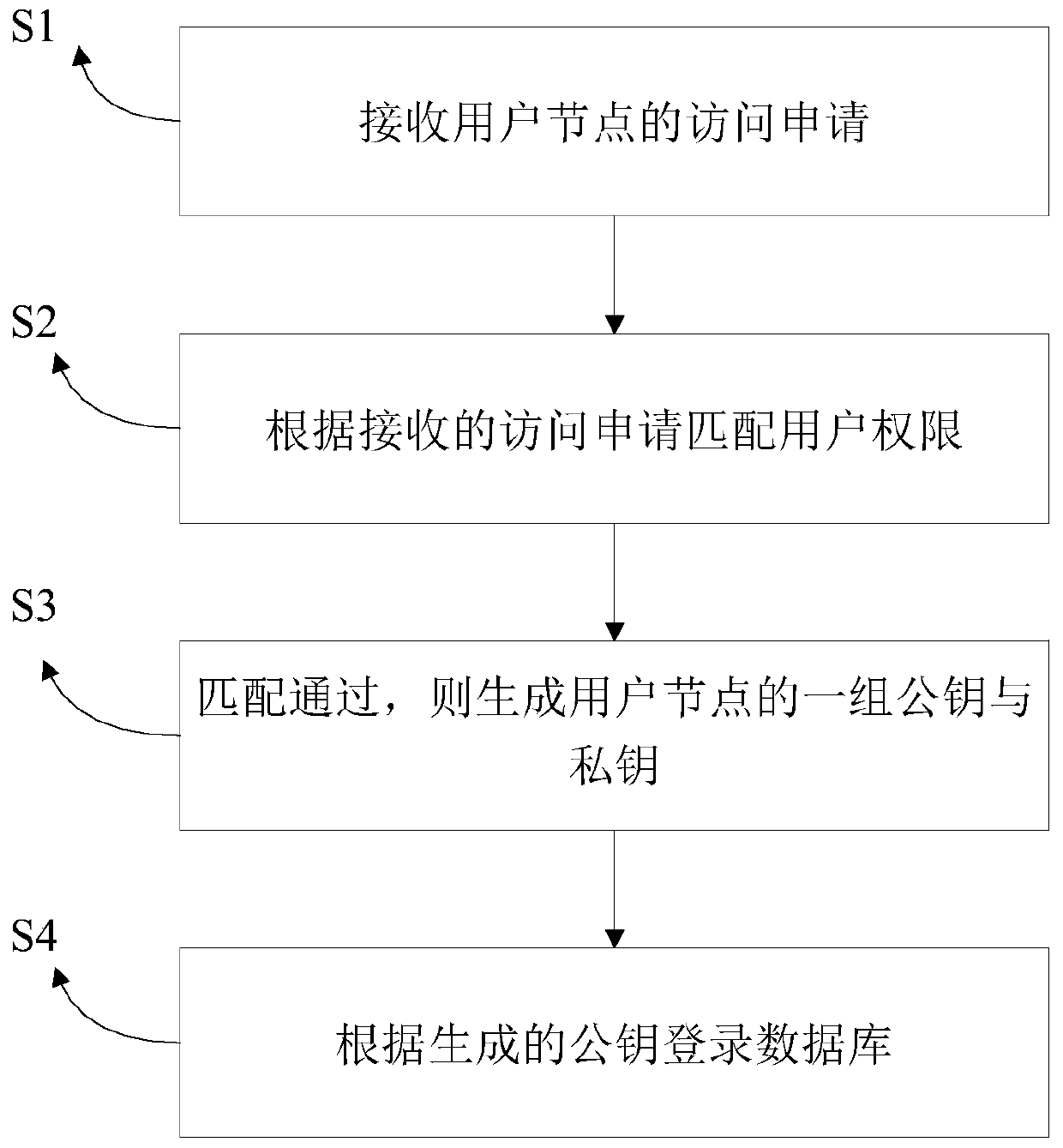
[0024] figure 1 It is a schematic flow chart of the database access control method based on public key verification according to the present invention, such as figure 1 As shown, the database access control method based on public key authentication described in the present invention comprises the following steps:
[0025] Step S1, receiving the access application from the user node, where the user node refers to the node that uses data in the blo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More