Encryption threshold signature method based on confusion technology
A technology and threshold technology, applied in the field of threshold cryptography, can solve security risks and other problems, and achieve the effect of overcoming leakage and protecting private key fragmentation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] In order to make the purposes, technical solutions and advantages of the embodiments of the present application clearer, the technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the drawings in the embodiments of the present application. Obviously, the described embodiments It is a part of the embodiments of this application, not all of them.
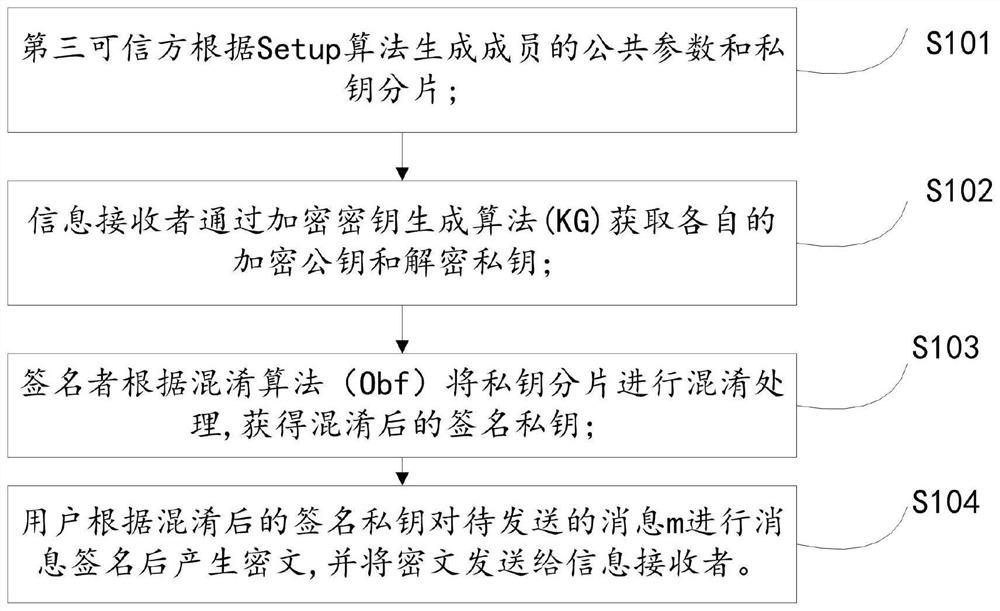
[0039] Such as figure 1 As shown, the encrypted threshold signature method based on obfuscation technology is applied to a cryptographic system based on obfuscation technology, and the method includes:
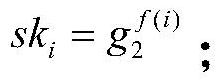
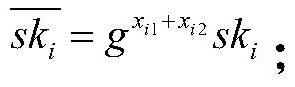
[0040] S101: The trusted third party generates the member's public parameter p and private key fragment sk according to the Setup algorithm i ; The public parameter p is public, and the private key fragment sk i is confidential;
[0041] The specific expression is:
[0042] p={q,G,G T ,e,g,g 1 , g 2,u′,U,VK};
[0043] sk=(sk 1 ,sk 2 ,...sk ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More