A digital identity verification method, device, computer equipment and storage medium
A digital identity and verification method technology, applied in the blockchain field, can solve the problems of low confidentiality of user privacy data and low timeliness of identity verification data sources, and achieve the effects of improving efficiency, ensuring confidentiality, and ensuring timeliness
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
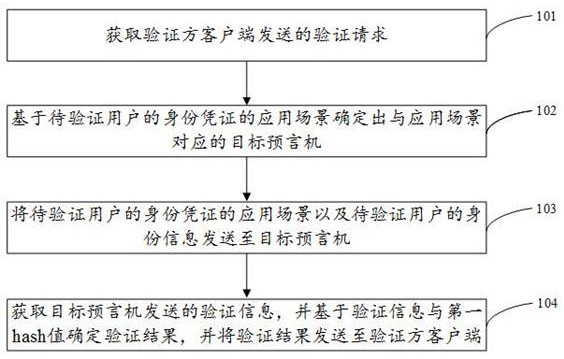
[0058] figure 1 It is a schematic flow diagram of a digital identity verification method provided according to an embodiment of the present application, applied to a blockchain digital identity contract, such as figure 1 As shown, can include:
[0059] Step 101. Obtain a verification request sent by a verifier client.
[0060] Wherein, the verification request may include: the application scenario of the identity certificate of the user to be verified, the identity information of the user to be verified, and the first hash value calculated by the verifier client based on the identity certificate of the user to be verified.
[0061] Wherein, in the embodiment of the present disclosure, the identity certificate of the user to be verified may specifically include the certificate number corresponding to the certificate of the user to be verified, for example, it may be the ID number, degree certificate number, and graduation certificate number of the user to be verified. The id...
Embodiment 2
[0087] figure 2 It is a schematic flow diagram of a digital identity verification method provided according to an embodiment of the present application, which is applied to a target oracle, such as figure 2 As shown, can include:
[0088] Step 201. Obtain the application scenario of the identity credential of the user to be verified sent by the digital identity contract and the identity information of the user to be verified.
[0089] Step 202. Query the identity certificate of the user to be verified based on the application scenario of the user's identity certificate and the identity information of the user to be verified.
[0090] Wherein, in one embodiment of the present disclosure, the target oracle specifically queries the identity certificate of the user to be verified in the application scenario based on the identity information of the user to be verified and the application scenario of the user's identity certificate to be verified.
[0091] For example, assuming ...
Embodiment 3
[0102] image 3 It is a schematic flow diagram of a digital identity verification method provided according to an embodiment of the present application, which is applied to the verifier client, such as image 3 As shown, can include:
[0103] Step 301. Obtain the information to be verified sent by the client of the party to be verified. The information to be verified may include the identity certificate of the user to be verified, the application scenario of the user's identity certificate to be verified, and the identity information of the user to be verified.
[0104] Step 302: Perform hash calculation on the identity certificate of the user to be verified to obtain a first hash value.
[0105] Wherein, in the embodiment of the present disclosure, the method for the verifier client to perform hash calculation on the identity certificate of the user to be verified to obtain the first hash value may include:
[0106] Determine the preset calculation rule based on the applica...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com