V2G network cross-domain transaction security method based on block chain
A blockchain and cross-domain technology, applied in protocol authorization, data processing applications, instruments, etc., can solve the problems of V2G network development obstacles, insecurity, etc., to reduce the number of signatures and verifications, high efficiency, and scalability strong effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
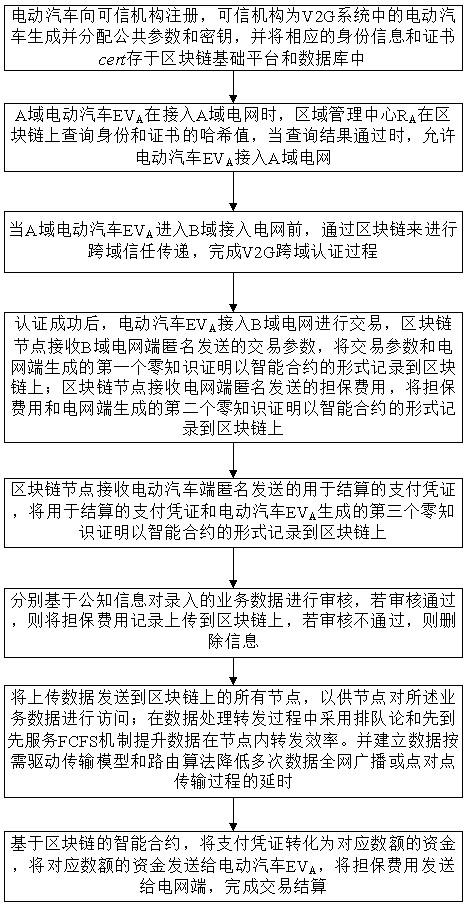
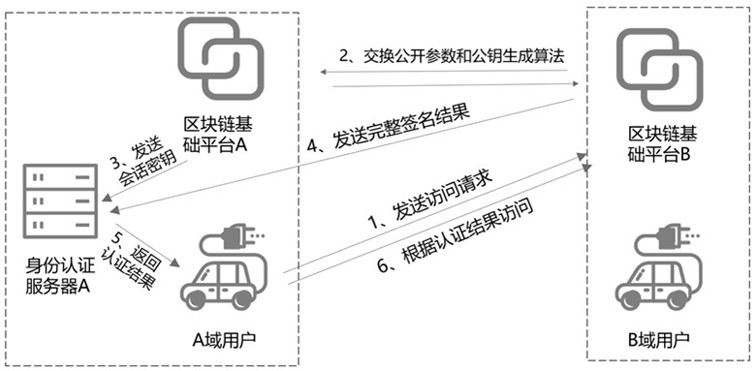
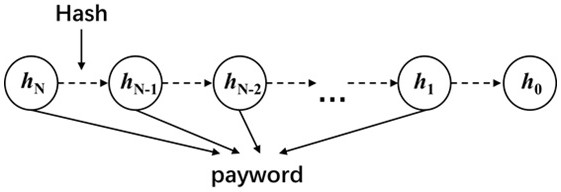
[0034] The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0035] The two-way power transmission process between electric vehicles and the grid will generate a large number of records, and the control center can provide valuable services by analyzing these records, but at the same time, these records will also cause a series of privacy issues, and these security and privacy issues It is a major obstacle to the development of V2G networks. Blockchain technology has achieved extensive success in digital currency applicati...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More