Data security protection method and device, electronic equipment and storage medium
A data security and database technology, applied in the field of data security, can solve problems such as privacy data leakage, and achieve the effect of ensuring security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
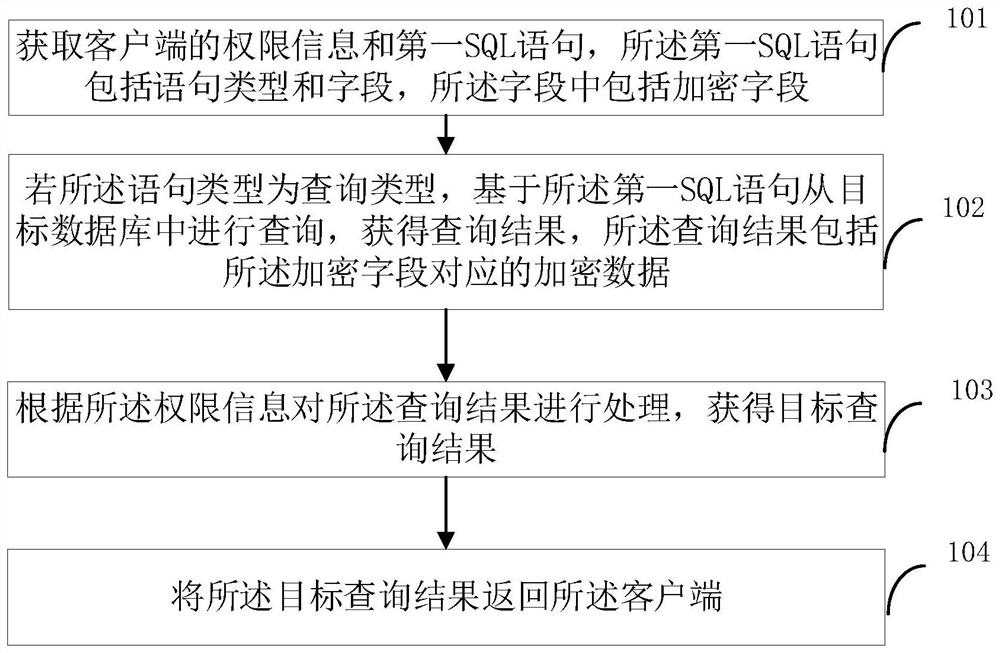
[0033] The technical solutions in the embodiments of the present application will be described below with reference to the drawings in the embodiments of the present application.
[0034] figure 1 A schematic flow diagram of a data security protection method provided in the embodiment of this application, as shown in figure 1 As shown, this method can be applied to the server connected to the database. The server has an agent end and a management end. The agent end is the protection end of the outer layer of the database. It protects the database on the basis of the database firewall and can The data request sent by the client is processed accordingly to provide data protection, and the management terminal is used to implement database management functions, such as adding data assets, configuring rules, and data encryption. The method includes:
[0035] Step 101: Obtain permission information of the client and a first SQL statement, the first SQL statement includes a stateme...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More