Financial POS system against channel Trojan horse attack and its anti-attack implementation method
A POS system and Trojan horse technology, applied in cash registers, instruments, digital data authentication, etc., can solve the problem that the bank card system cannot distinguish and bear responsibilities, and achieve the effect of increasing risks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment
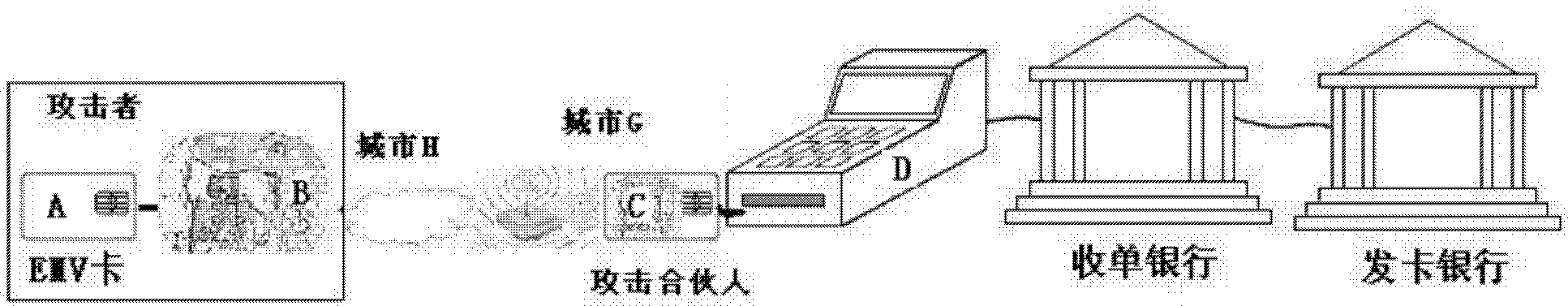
[0092] like Figure 7As shown, the financial POS system of a kind of anti-channel Trojan horse attack of the present embodiment comprises POS main board, IC card box, password keyboard, user PIN disk, nonvolatile memory, IC card, and trust management side, described IC card box Be connected with the POS main board, the password keyboard is connected with the IC card box, the POS main board is connected with the trust management side through the I / O interface, and the IC card is connected with the trust management side through the IC card box;
[0093] The password keyboard is used to receive the user's PIN password;
[0094] The user PIN disk is used to display the transaction amount and receive the user PIN password;
[0095] The non-volatile memory is used to store the authorization certificate of the transaction;
[0096] The IC card box, password keyboard, user PIN disk, and IC card are all provided with a password chip;
[0097] The trusted management party shares keys...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More