Image steganography method and secret information extraction method
A secret information and image technology, applied in image data processing, image data processing, instruments, etc., can solve the problems of embedding and steganographic methods with small embedding capacity and image distortion
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
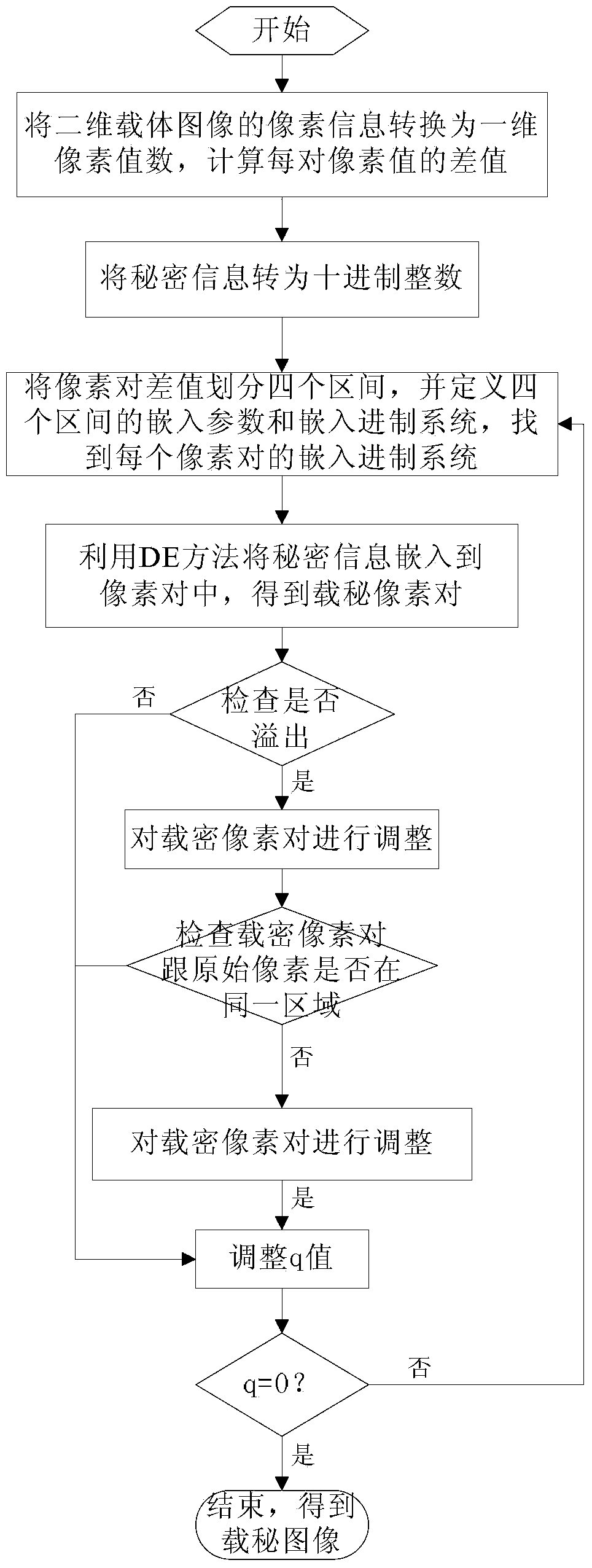
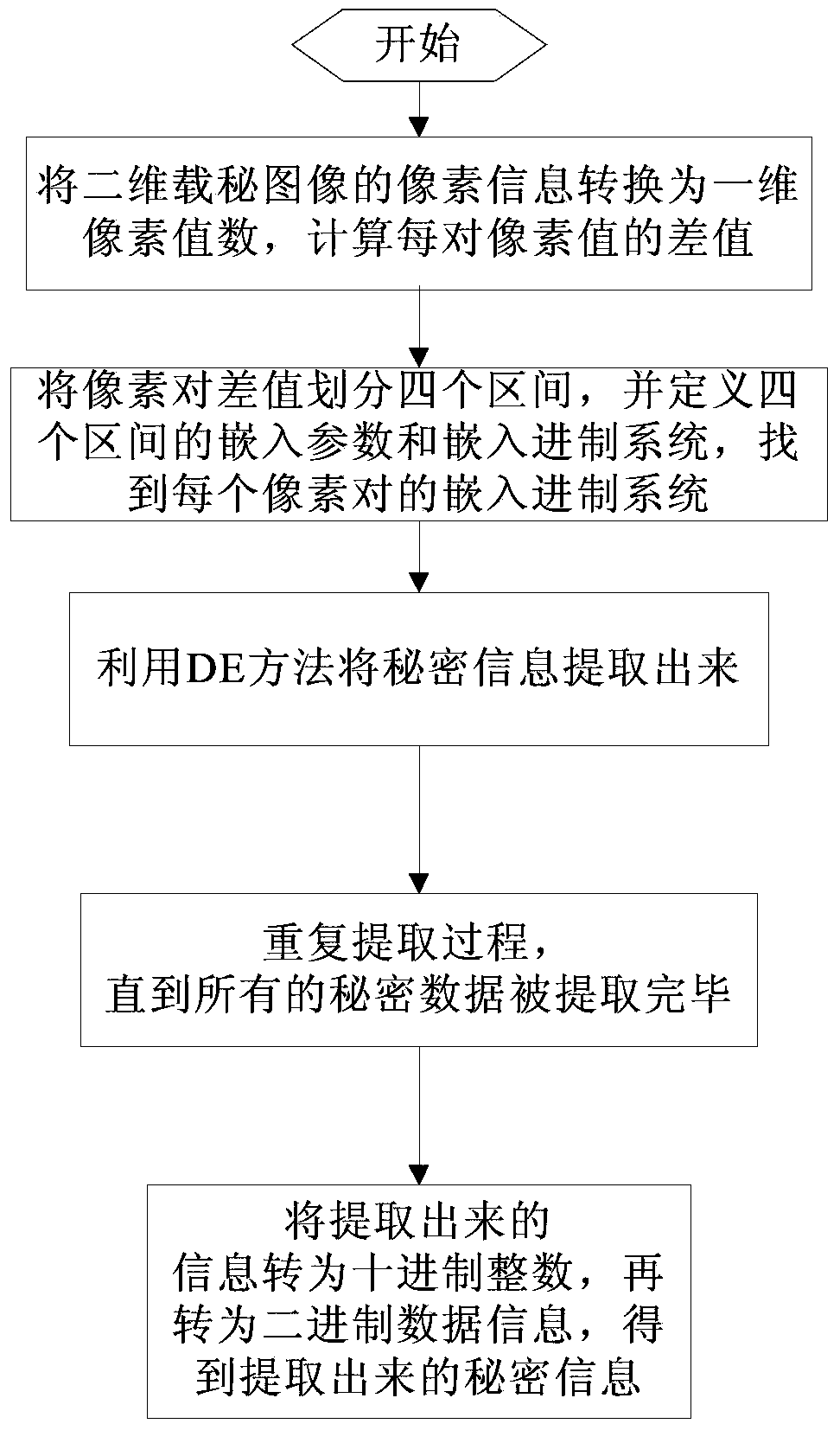
[0044] This embodiment first provides an image steganography method for embedding secret information S with size N 1 ×N 2 In the carrier image I, it includes the following steps, see figure 1 Shown:
[0045] (1), using the zigzag scanning method, in order from top to bottom, the size is N 1 ×N 2 The pixel information of the two-dimensional carrier image I is converted into a set of continuous non-overlapping one-dimensional pixel value data, two adjacent pixel values are a group, and each group of pixel values is represented by W i said, W i A pair of pixel values in (x i ,y i ) means, 0≤i≤N 1 ×N 2 / 2, finally by d i =|x i -y i |, calculate the difference between each pair of pixel values;
[0046] (2) Perform DES encryption on the secret information S, and convert the encrypted secret information S′ into a decimal integer q;
[0047] (3), d calculated by (1) i Values are divided into four intervals T j , j=1,2,3,4, where T 1 The interval range is [0,15...
Embodiment 2
[0065] Different from Embodiment 1, in the step (6), select scheme A or scheme B for the secret-carrying pixel pair (x i ',y i ') to adjust:
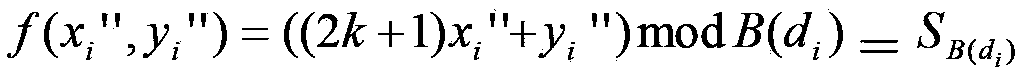
[0066] calculate X A = log 2 B ( d i ) ( x i - x i ′ ′ ′ ) 2 + ( y i - ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More