Power attack prevention method oriented at AES algorithm and circuit achieving method thereof
A technology with anti-power consumption and algorithm, applied in the direction of encryption device with shift register/memory, etc., can solve the problem of high attack efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
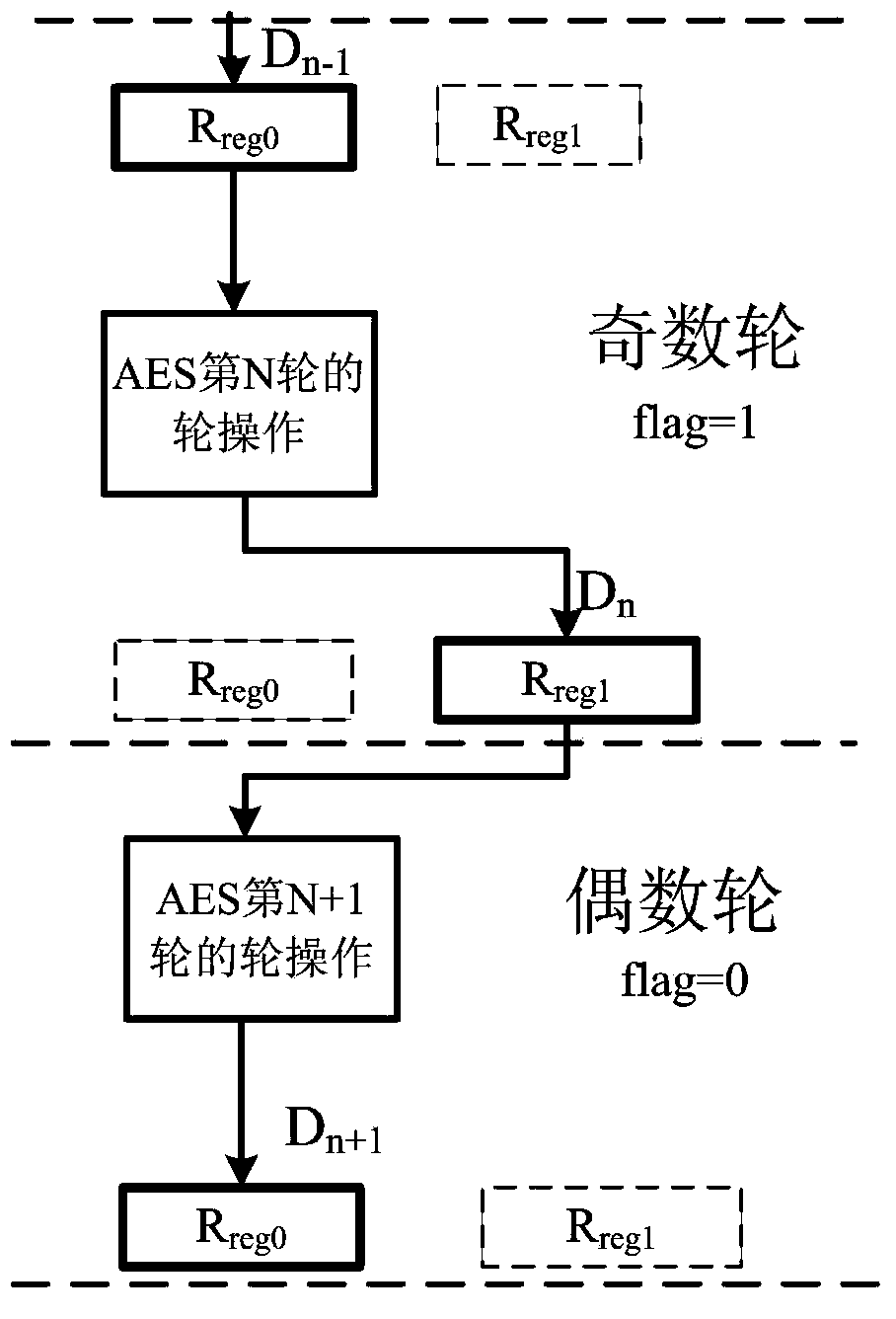
[0045] Below in conjunction with accompanying drawing and specific embodiment, further illustrate the present invention, should be understood that these embodiments are only for illustrating the present invention and are not intended to limit the scope of the present invention, after having read the present invention, those skilled in the art will understand various aspects of the present invention Modifications in equivalent forms all fall within the scope defined by the appended claims of this application.
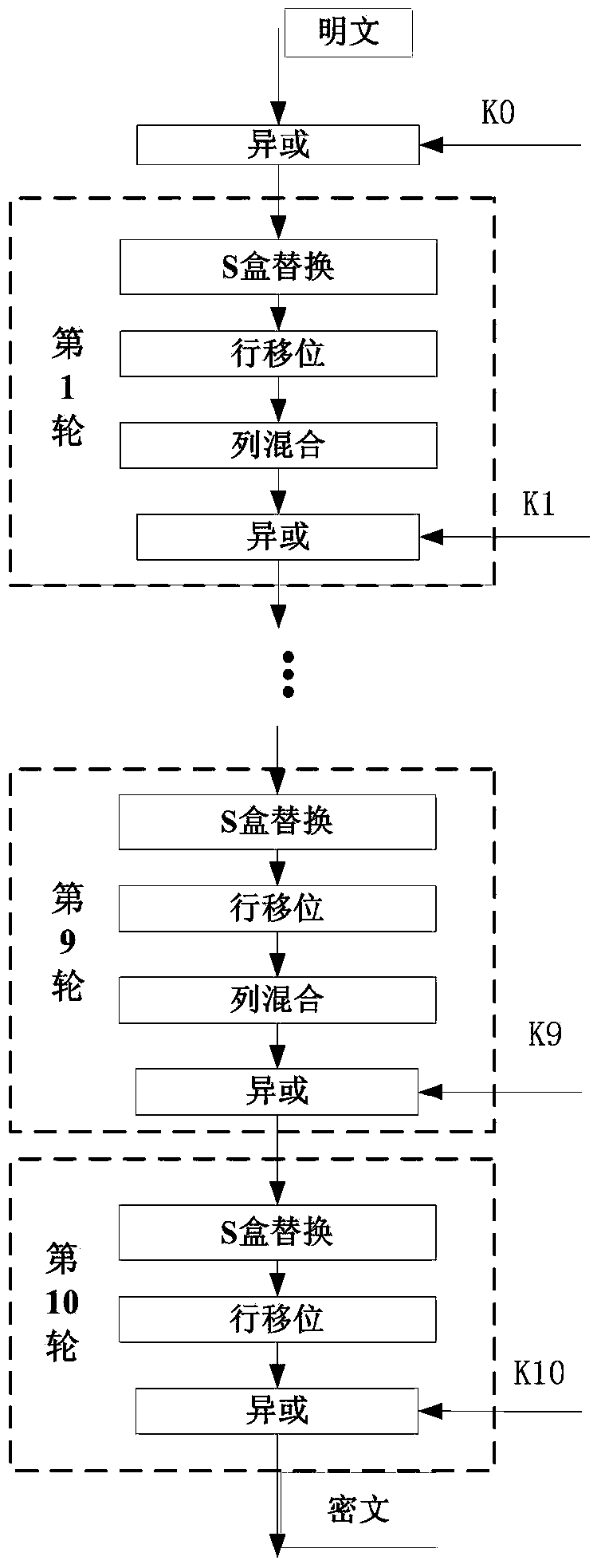
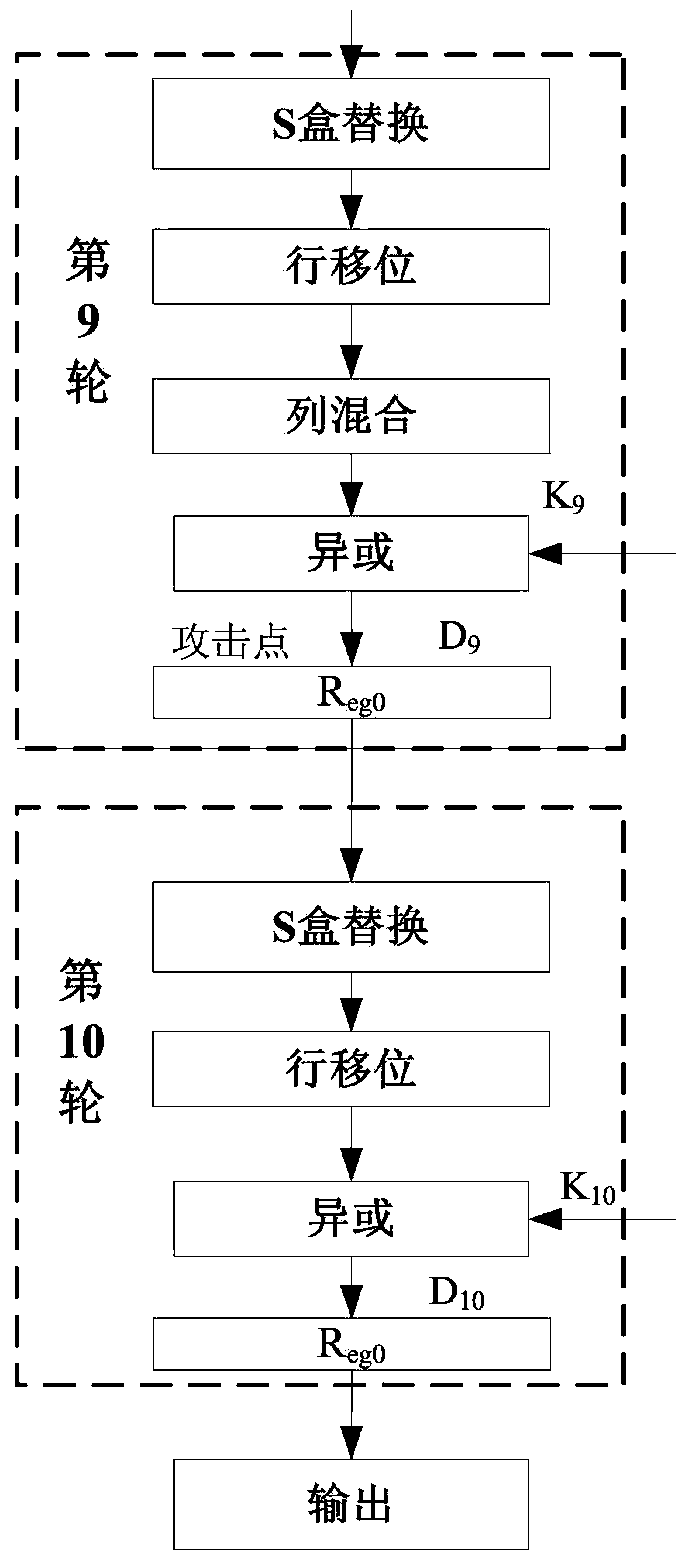
[0046] Such as figure 1 As shown, the original AES block encryption algorithm consists of 3 parts, including the initial XOR with the key, 9 cycles of round operations in the middle, and transformation at the end of the 10th round. The initial key of AES is 128 bits, and each round requires a 128-bit subkey k i (i=0,...,10), a total of eleven subkeys, the subkeys are obtained by expanding the initial key.
[0047] The 9 rounds of round operations in the middle of the A...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More