Inaccessible function call path detection method in complex system
A function call path and complex system technology, applied in the computer field, can solve problems such as the lack of detection methods for unreachable function call paths, and achieve effective analysis and accurate detection effects
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] In order to make the technical problems, technical solutions and advantages to be solved by the present invention clearer, the following will describe in detail with reference to the drawings and specific embodiments.
[0032] First, the concepts used in the embodiments of the present invention are described for easy understanding.
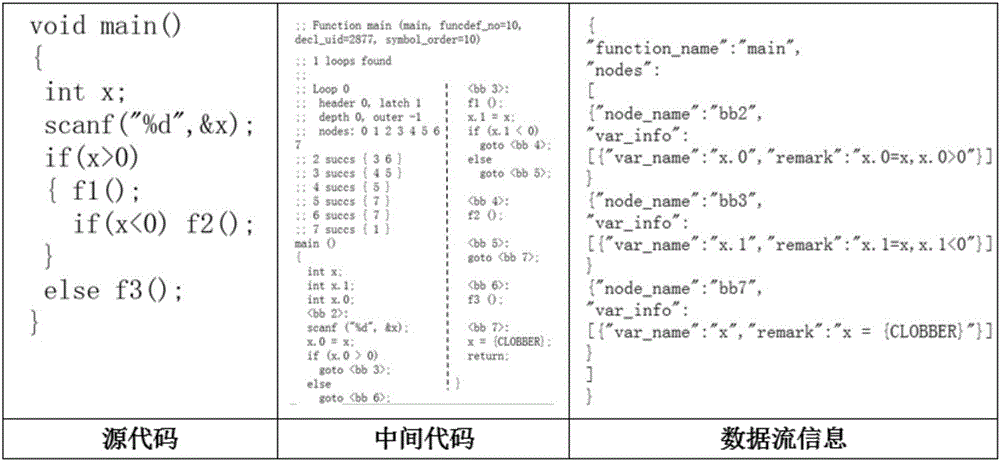
[0033] 1. Control flow graph:
[0034] The control flow graph consists of nodes (N) and edges (E), where each node represents a basic code block, and each edge has a start node (B) and a termination node (D), representing the basic code block a control flow. So the control flow graph can be represented by a quadruple (E∈N×N, B∈N, D∈N).
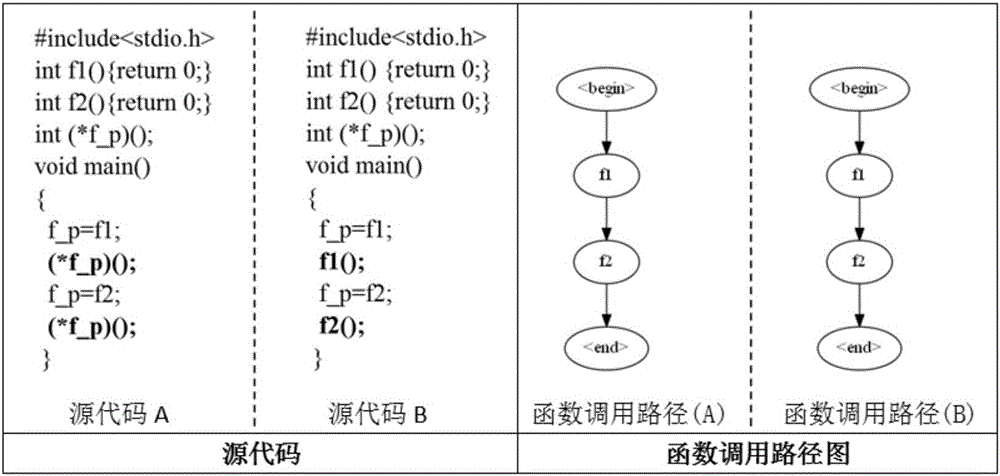
[0035] 2. Function call path set: for the program source code, the set of function name sequences from the program entry point to the exit point obtained from the function call relationship, expressed as G={P 0 ,P 1 ,...,P n}, P i ={F 0 , F 1 ,...,F n} represents one of the function call paths, F ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More