White-box cryptography encryption-decryption method based on expansion ciphertext
A white-box cipher and encryption method technology, applied in the field of white-box cipher encryption and decryption, can solve the problems of slow decryption speed and insecurity, and achieve high efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
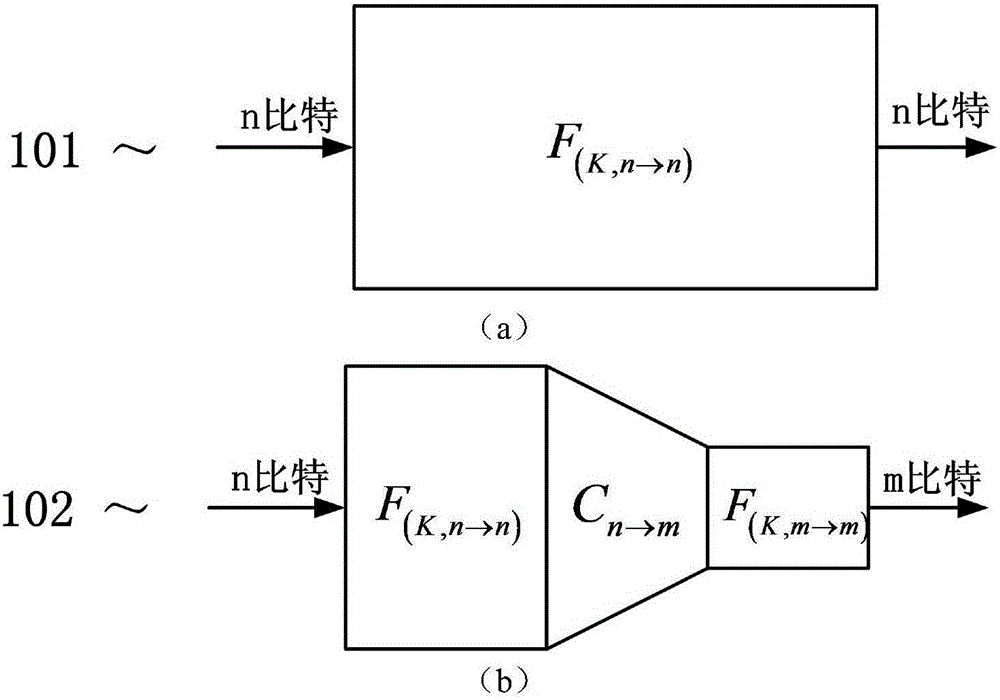
[0037] Using the lookup table of the hidden key to operate the data stream is the basic method of designing white-box ciphers: such as figure 1 (a), F (K,n→n) It is a one-to-one mapping from n bits to n bits related to the key K. After expressing it with the lookup table 101, it is difficult for the attacker to inversely deduce K from the lookup table or be related to F (K,n→n) Equivalent functional relationship. 101 may be a single lookup table, or a combination of a set of lookup tables.
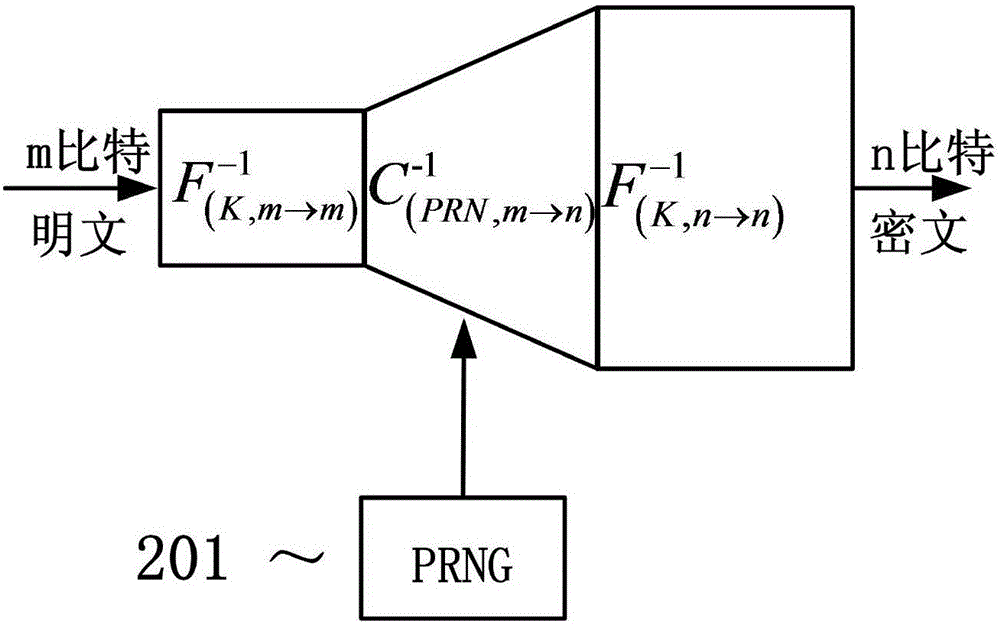
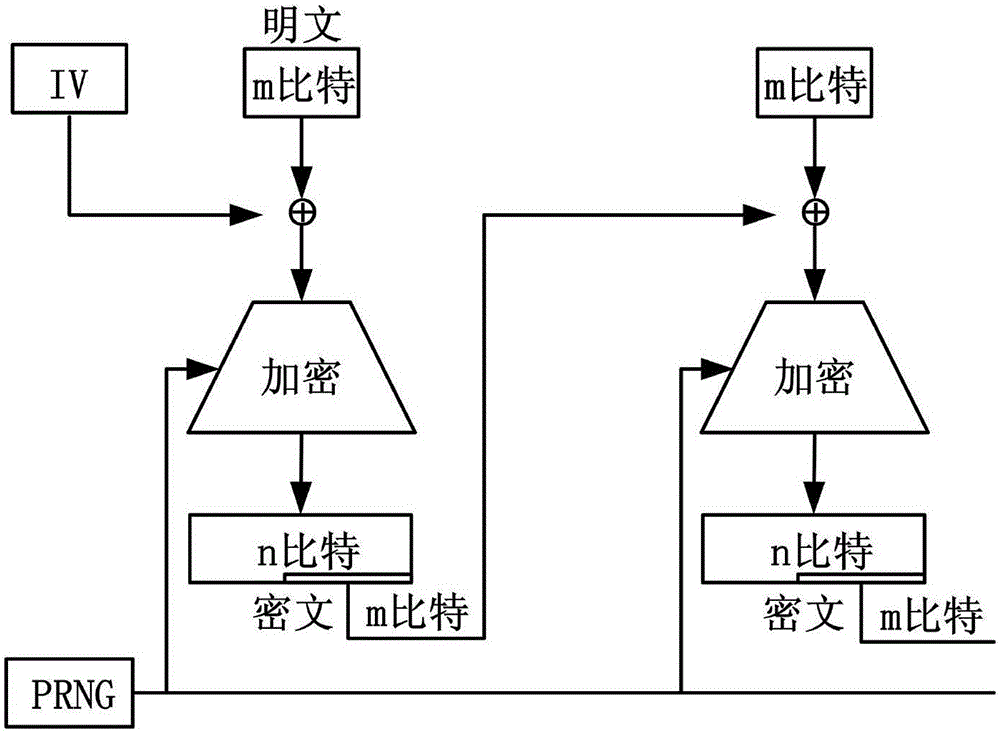
[0038] When the system is implemented, the server uses F (K,n→n) The inverse of the function encrypts the data, and the endpoint (running in a white-box environment) decrypts it using a lookup table. Considering the construction efficiency of the lookup table and the limitation of computing resources on the server side (in the case of multiple users, the key cannot be stored in the form of a lookup table for each user), the lookup table is generated by the superposition of relatively s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More