Cipher text access control system based on cloud computing platform
A cloud computing platform and access control technology, applied in the field of information security, can solve the problems of unreliable access control schemes for users, complex management of cloud storage service modules, and poor security, so as to reduce the storage space of ciphertext, improve the overall performance, improve the The effect of efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
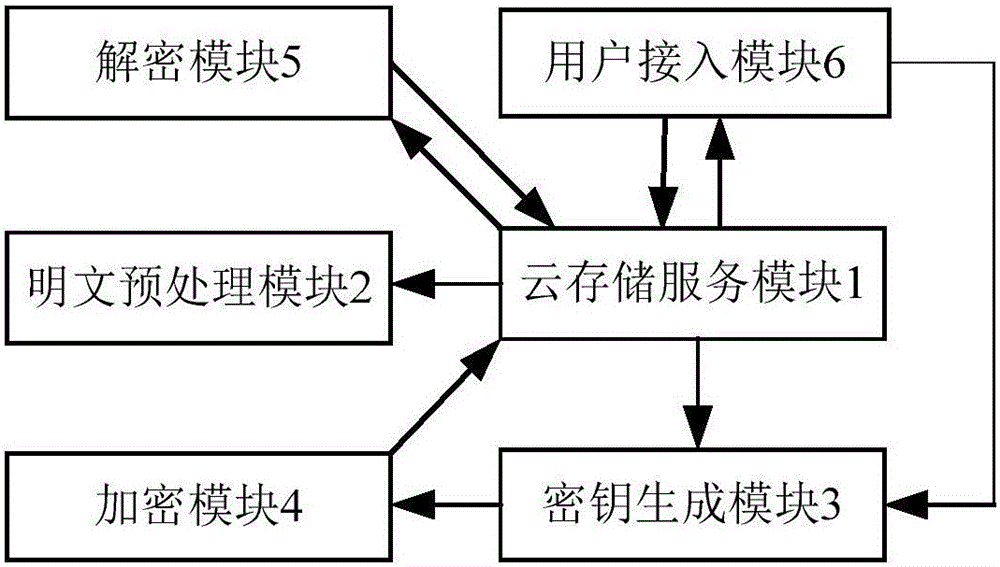
[0050] see figure 1 , figure 2 , the ciphertext access control system based on the cloud computing platform of this embodiment includes a cloud storage service module 1, a plaintext preprocessing module 2, a key generation module 3, an encryption module 4, a decryption module 5, and a user access module 6:
[0051] (1) Cloud storage service module 1, for providing data storage services for visiting users, including a cloud storage server for storing data and a data manager for controlling external users to access the cloud storage service module;
[0052] (2) The key generation module 3 is used to generate the initial public parameters and master key of the system. When receiving the request from the visiting user, it distributes the public parameters of the system for the encryption module 4, and generates corresponding public parameters for each visiting user. private key, and participate in the negotiation of the shared session key between the cloud storage service module...
Embodiment 2
[0085] see figure 1 , figure 2 , the ciphertext access control system based on the cloud computing platform of this embodiment includes a cloud storage service module 1, a plaintext preprocessing module 2, a key generation module 3, an encryption module 4, a decryption module 5, and a user access module 6:
[0086] (1) Cloud storage service module 1, for providing data storage services for visiting users, including a cloud storage server for storing data and a data manager for controlling external users to access the cloud storage service module;
[0087] (2) The key generation module 3 is used to generate the initial public parameters and master key of the system. When receiving the request from the visiting user, it distributes the public parameters of the system for the encryption module 4, and generates corresponding public parameters for each visiting user. private key, and participate in the negotiation of the shared session key between the cloud storage service module...
Embodiment 3
[0120] see figure 1 , figure 2 , the ciphertext access control system based on the cloud computing platform of this embodiment includes a cloud storage service module 1, a plaintext preprocessing module 2, a key generation module 3, an encryption module 4, a decryption module 5, and a user access module 6:
[0121] (1) Cloud storage service module 1, for providing data storage services for visiting users, including a cloud storage server for storing data and a data manager for controlling external users to access the cloud storage service module;
[0122] (2) The key generation module 3 is used to generate the initial public parameters and master key of the system. When receiving the request from the visiting user, it distributes the public parameters of the system for the encryption module 4, and generates corresponding public parameters for each visiting user. private key, and participate in the negotiation of the shared session key between the cloud storage service module...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More