Feature selection method and system for network security data
A feature selection method and network security technology, applied in the feature selection method and system field of network security data, can solve the problem that redundant features are not processed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] Embodiments of the present invention are described in detail below, examples of which are shown in the drawings, wherein the same or similar reference numerals designate the same or similar elements or elements having the same or similar functions throughout. The embodiments described below by referring to the figures are exemplary only for explaining the present invention and should not be construed as limiting the present invention.
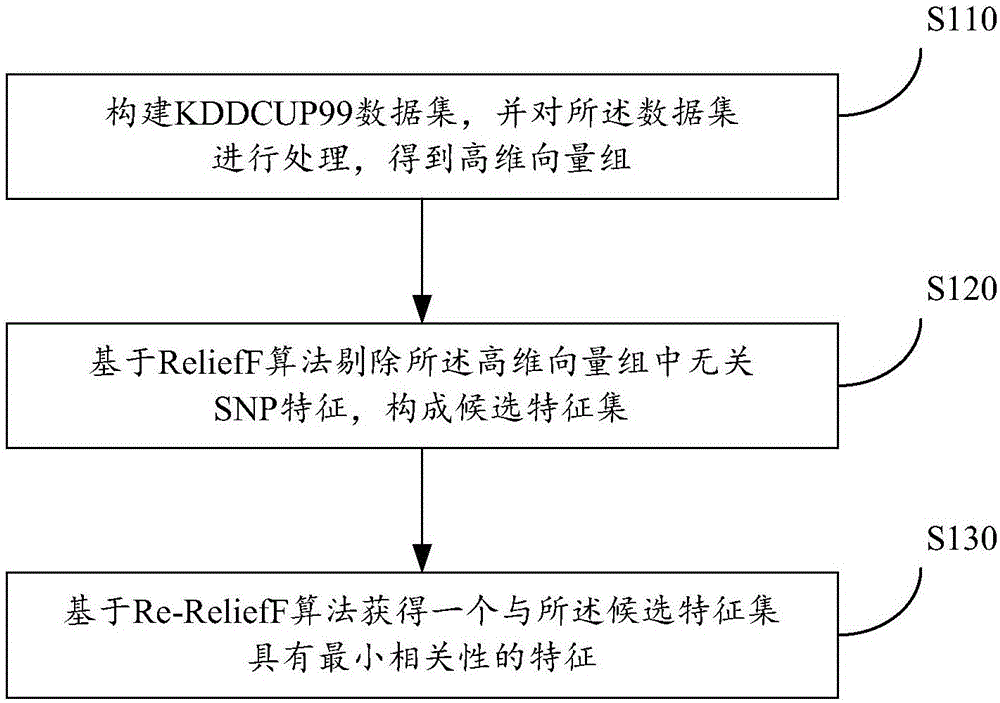
[0061] see figure 1 , the feature selection method of the network security data provided by the application, comprising the following steps:
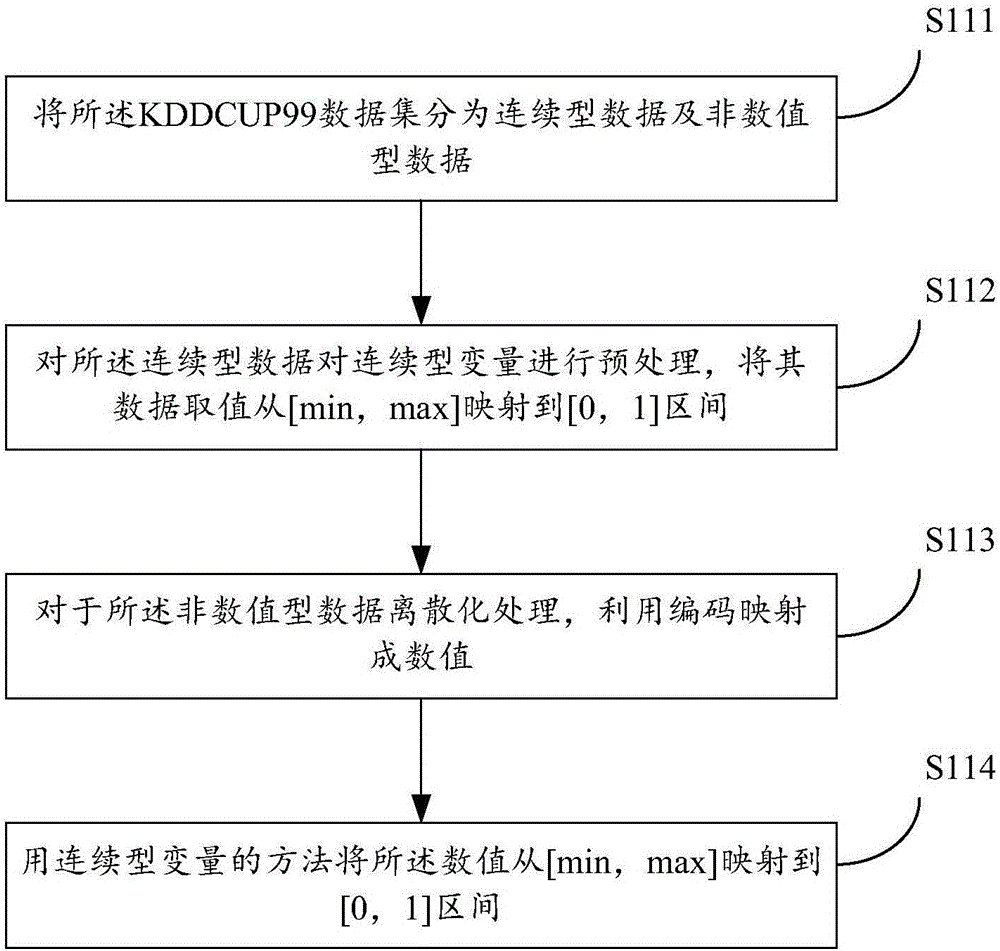
[0062] Step S110: constructing a KDDCUP99 data set, and processing the data set to obtain a high-dimensional vector group;
[0063] It can be understood that in feature selection, the selection of data sets is the first step in researching and evaluating algorithms, and the accuracy of data sets will directly determine the evaluation results of various algorithms. The KDDCUP99 dataset provided i...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More