Regular Hartley transform chaotic dual random phase coding optical image encryption method
A technology of chaotic random phase and double random phase, which is applied in the direction of secure communication through chaotic signals, image data processing, image data processing, etc., can solve the inconvenience of key management and transmission, the encryption system is vulnerable to chosen plaintext attack and known plaintext Attacks, random phase masks are inconvenient to update, etc., to achieve the effect of convenient key management and transmission, resistance to known plaintext attacks, and resistance to chosen plaintext attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
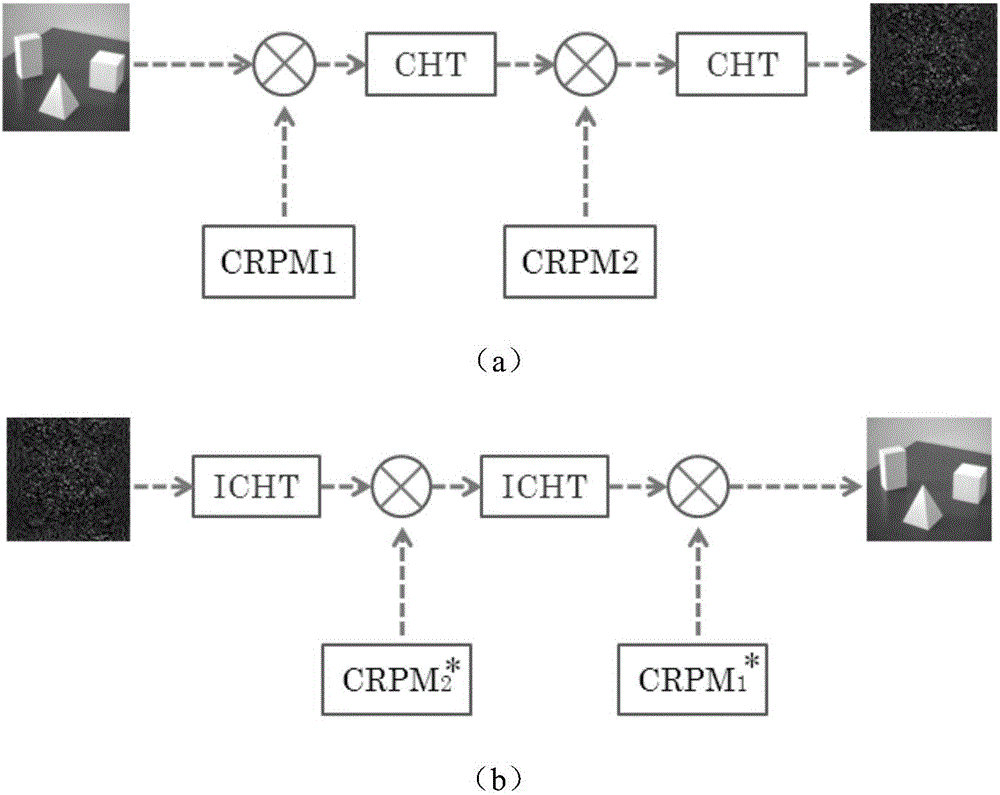
[0073] An optical image encryption method based on regular Hartley transform and chaotic double-random phase encoding, the schematic diagram of the encryption and decryption process is as follows figure 1 As shown, the encryption method consists of the construction of the two-dimensional regular Hartley transform system, the generation of the chaotic key, and the process of image encryption and decryption.
[0074] (1) Construction of two-dimensional regular Hartley transform system:
[0075] In the encryption method provided by the present invention, through rigorous mathematical derivation and proof, it is found that the two-dimensional canonical Hartley transform can be composed of a linear combination of two two-dimensional linear canonical transformations (LCT). Just as the linear canonical transform (LCT) is a more generalized Fourier transform and fractional Fourier transform, the canonical Hartley transform is a more generalized Hartley transform and fractional Hartley...
Embodiment 2
[0082] Combine below figure 1 1. The design principle introduces the scheme in embodiment 1 in detail, see the following description for details:
[0083] An optical image encryption method based on regular Hartley transform and chaotic double-random phase encoding, the schematic diagram of the encryption and decryption process is as followsfigure 1 shown. The encryption method consists of the construction of two-dimensional regular Hartley transform system, the generation of chaotic key, and the process of image encryption and decryption. The specific implementation manners of these three parts will be described in detail below.
[0084] (1) Construction of two-dimensional regular Hartley transform system:
[0085] After rigorous mathematical derivation and proof (the proof and derivation process is omitted here), it is found that the two-dimensional canonical Hartley transform (CHT) can be composed of a linear combination of two two-dimensional linear canonical transformat...
Embodiment 3
[0105] Below in conjunction with specific accompanying drawing, the scheme in embodiment 1 and 2 is carried out feasibility verification, see the following description for details:
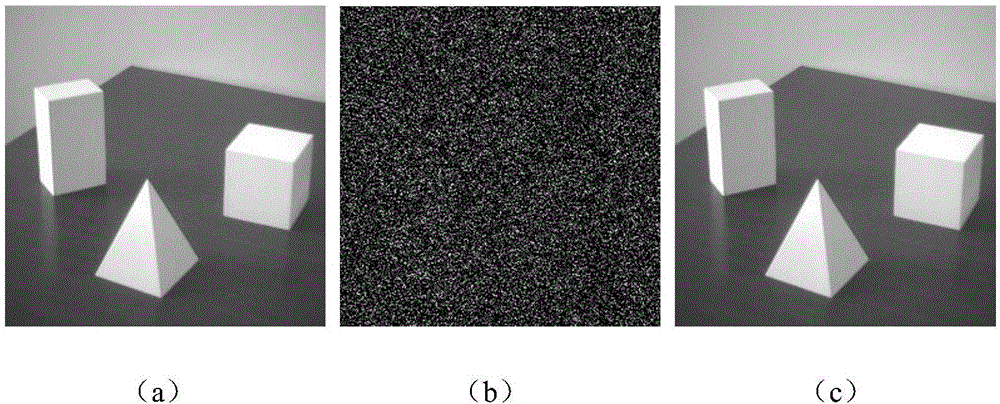
[0106] Adopt the encryption method provided by the implementation of the present invention to an image (such as figure 2 As shown in (a), after encryption, the obtained encrypted image is as follows figure 2 (b) shown.
[0107] Depend on figure 2 (b) It can be seen that any information of the original image is hidden. When all the keys are correct, the decrypted image is as follows figure 2 (c) shown. Depend on figure 2 (c) It can be seen that the original image can be completely restored. It shows that the encryption and decryption of grayscale images using this system is successful.
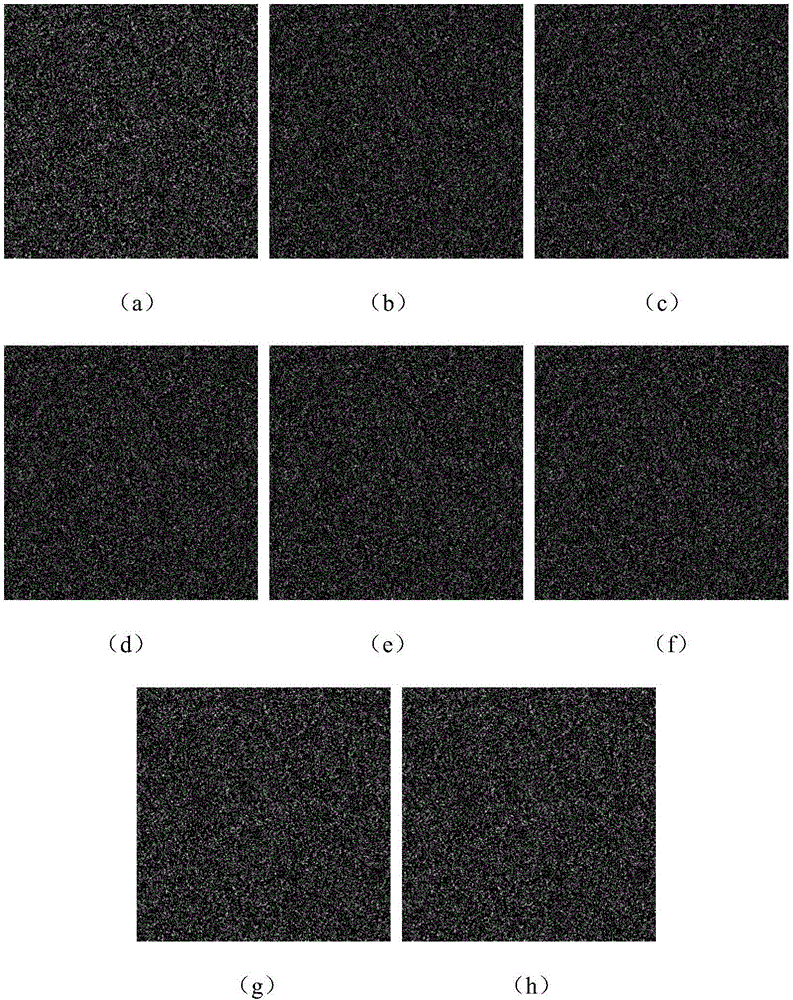
[0108] In addition, when one key is wrong and other keys are correct, the decryption result is as follows: image 3 (a)-3(h). It can be seen that the security of the system can be guaranteed.
[0109...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More