Complex attack identification technology for wireless intrusion detection system
A technology for wireless intrusion detection and attack identification, applied in transmission systems, wireless communications, digital transmission systems, etc., can solve problems such as different attack targets, increased difficulty of intrusion detection or defense, and different attack methods
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0131] The present invention will be further described below in conjunction with the examples. The description of the following examples is provided only to aid the understanding of the present invention. It should be pointed out that for those skilled in the art, without departing from the principles of the present invention, some improvements and modifications can be made to the present invention, and these improvements and modifications also fall within the protection scope of the claims of the present invention.
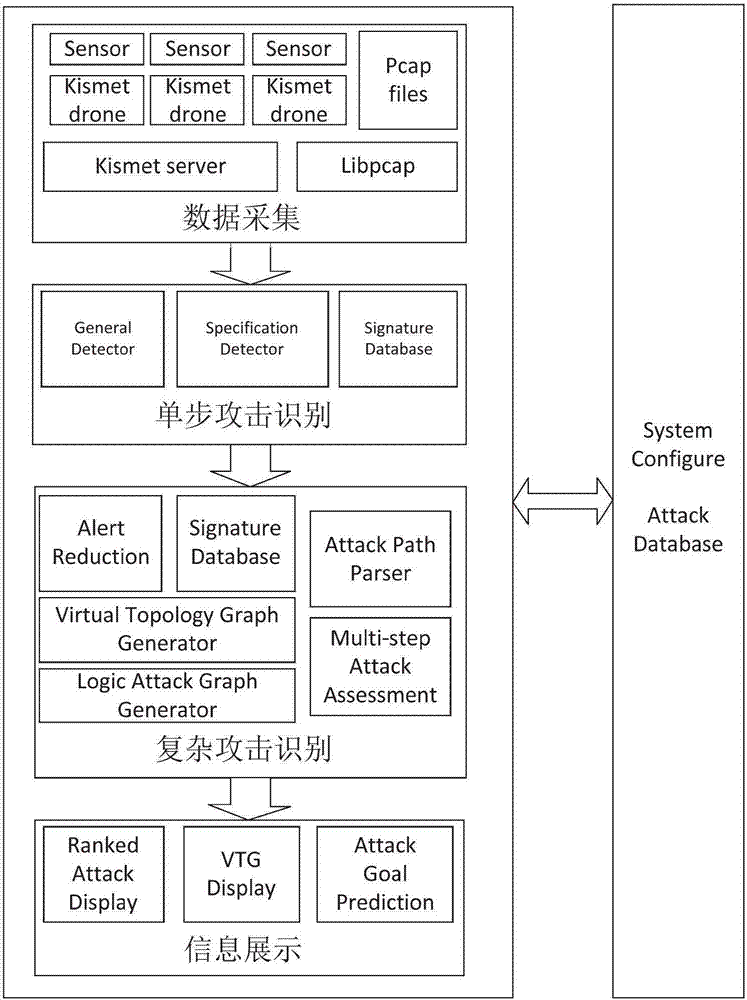
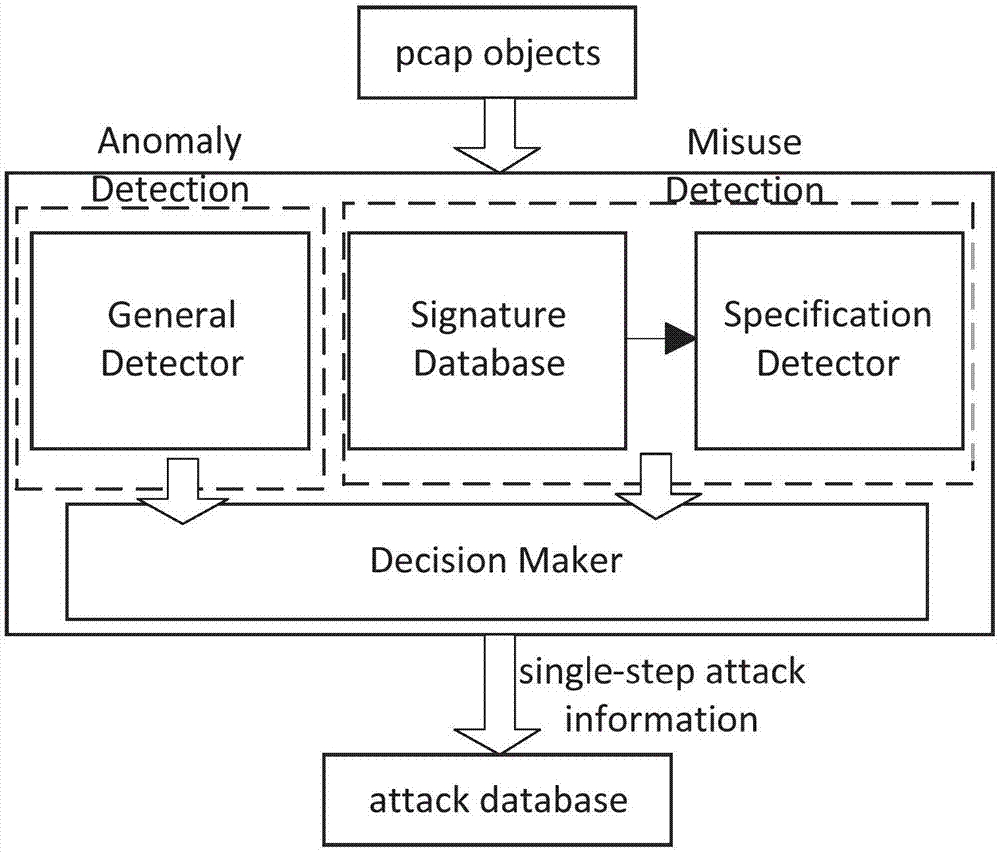
[0132] like Figure 1 to Figure 19 As shown, the complex attack identification technology in the wireless network of the present invention includes four steps: data collection, single-step attack identification, complex attack identification and information display interface.
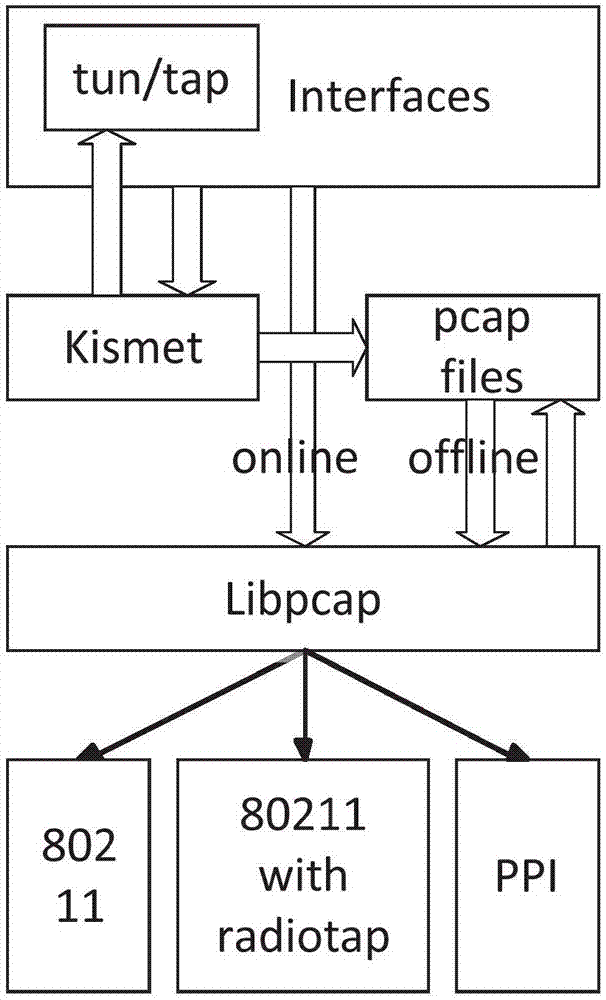
[0133] (1) Data collection: The source of data collection and the selection of metrics are very important for intrusion detection systems. Selecting appropriate metrics can effectively c...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More