CCA secure proxy re-encryption method with delegable verifiability
A proxy re-encryption and re-encryption technology, which is applied in the computer field, can solve problems such as the inability to forge legal public key encrypted ciphertexts and insufficient security of encryption methods, and achieve the effects of avoiding damage to rights and interests, safe and efficient transmission, and improving security
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
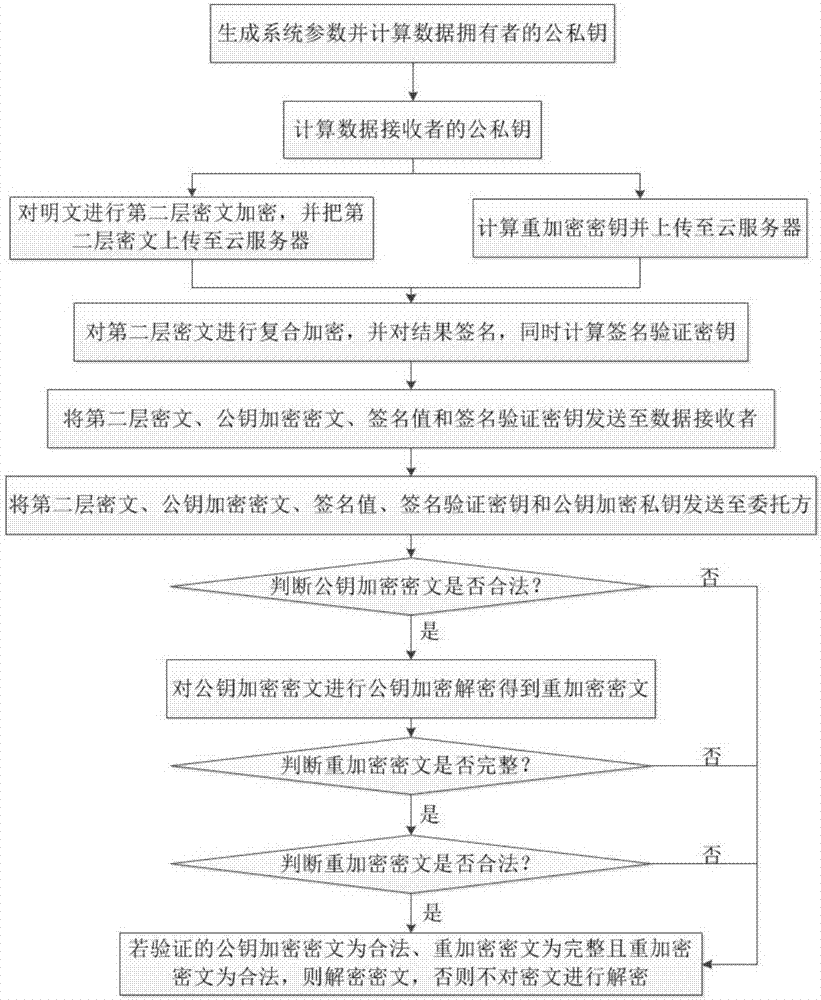
Image
Examples
Embodiment Construction
[0026] The present invention will be described in further detail below in conjunction with the accompanying drawings.
[0027] Step 1. The data owner generates system parameters param according to their own security requirements, including: seven randomly selected members g in the first group G 1 , g 2 , h 1 , h 2 , u, v, w, encryption parameters L, four hash functions H 0 , H 1 , H 2 , H 3 , Multiplicative cyclic group Finite field and bilinear map e, the implementation steps are:
[0028] Step 1a, the data owner randomly selects a prime number p according to their own security requirements, and constructs the first group G and the second group G with p members respectively T , a multiplicative cyclic group with members p-1 and a finite field with p members Finally, according to the construction method of bilinear mapping in algebra, using the first group G and the second group G T Construct bilinear map e:G×G→G T ;
[0029] Step 1b, the data owner randomly ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More