Method for realizing data security storage based on fragment recombination technology
A technology for data security storage and reorganization technology, which is applied in the field of data security storage based on fragmentation and reorganization technology, which can solve problems such as enterprise property loss and intrusion of internal ghosts, and achieve the effect of increasing difficulty and ensuring security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0020] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to explain the present invention, and are not intended to limit the present invention.
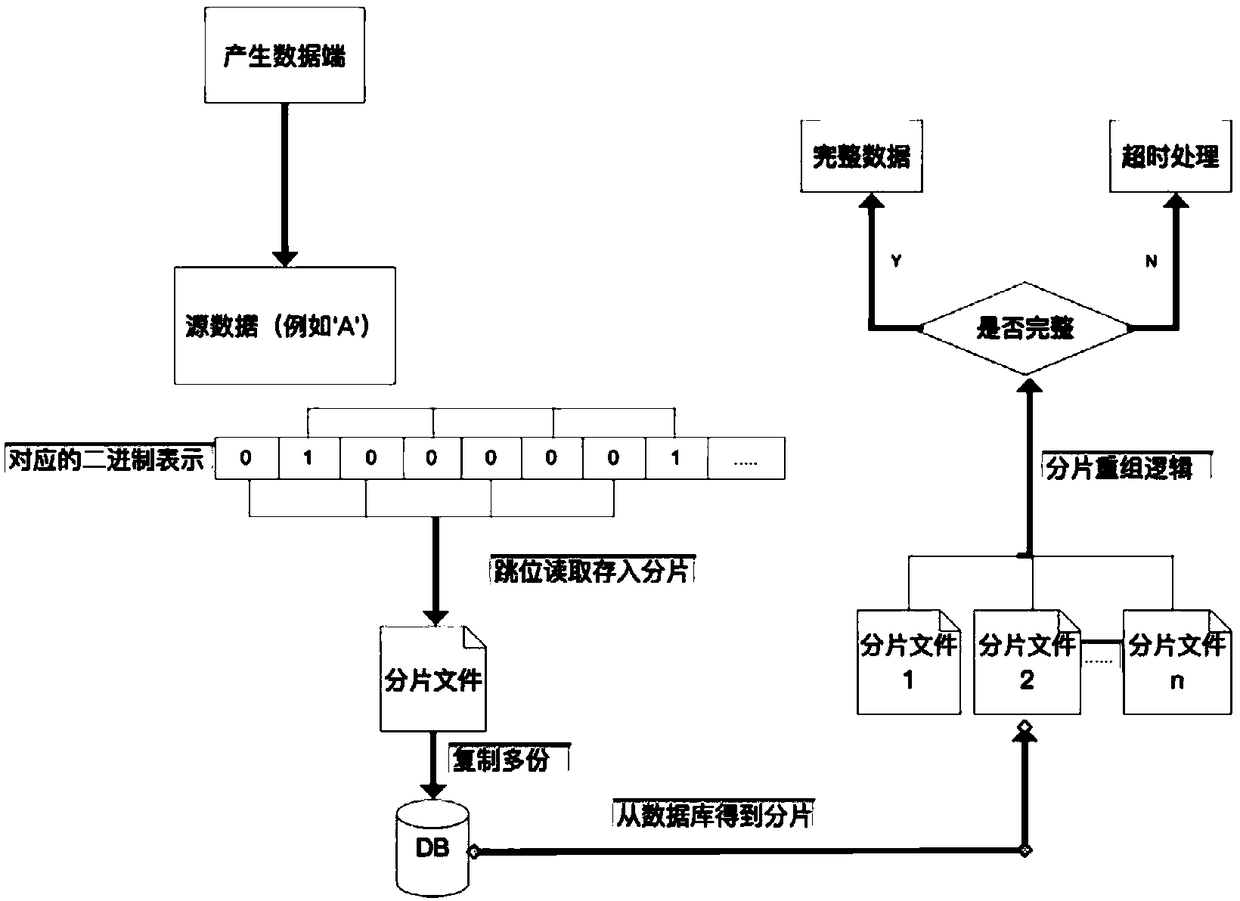
[0021] Such as figure 1 As shown, the embodiment of the present invention provides a method for realizing data security storage based on fragment reassembly technology, including the following steps:
[0022] S1, parsing the source data to generate a binary array;
[0023] S2, perform bit skip reading on the generated binary array to obtain a plurality of fragmented files; wherein, during bit jump reading, the number of bit jumps is controlled, and the tail of the binary array is supplemented according to the number of bit jumps Zero, so that the number of digits in the binary array after zero p...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More