A vulnerability detection method and device
A vulnerability detection and vulnerability technology, applied in transmission systems, electrical components, etc., can solve the problems of error-prone, low vulnerability detection efficiency, etc., and achieve the effect of improving efficiency and accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
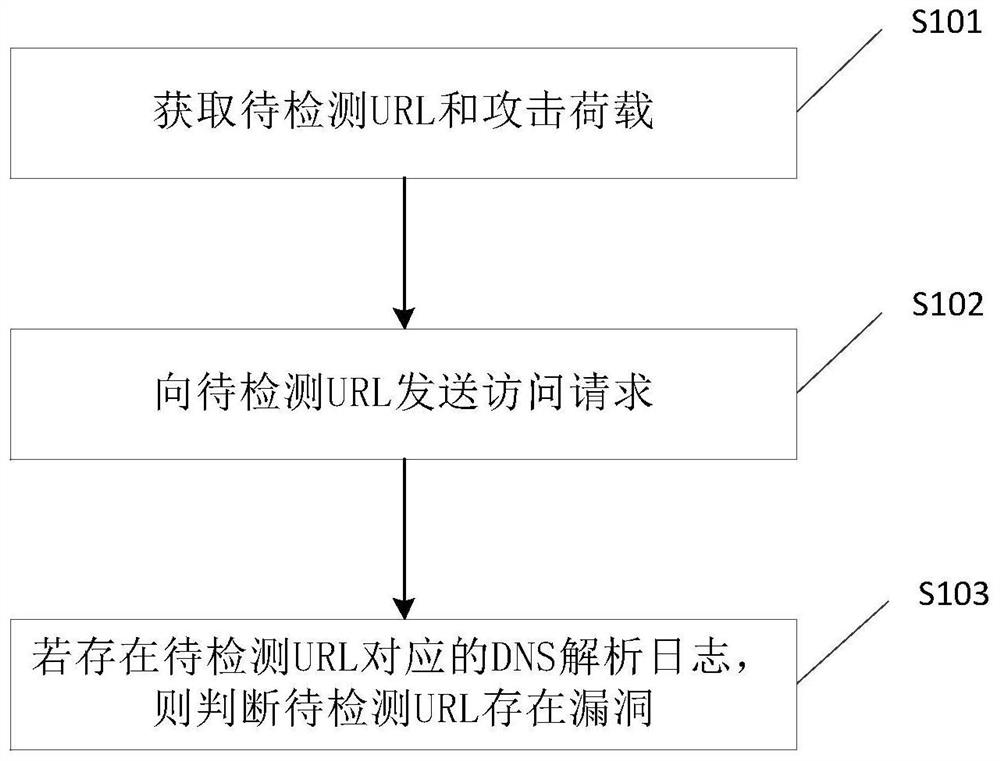
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0031] The inventor found through research that there may be SQL injection vulnerabilities, command execution vulnerabilities, SSRF and other vulnerabilities in the Web site, and in the process of detecting the vulnerabilities, the Web application sometimes does not echo, resulting in low efficiency of vulnerability detection.
[0032] Currently, when there is no echo in the web application, you can use the penetration testing tool to detect vulnerabilities. Penetration testing is a mechanism provided to prove that the network defense is operating normally according to the expected plan. Generally speaking, the security of the computer network system can be evaluated by simulating the attack method of malicious hackers.
[0033] In addition, the domain name system is the mapping relationship between domain names and Internet Protocol (IP) addresses on the World Wide Web. Users can access the Internet through domain names, and obtain the IP addresses corresponding to domain name...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More