Data encryption and decryption and key distribution method and device, equipment and readable storage medium
A technology for encrypting public keys and session keys, which is applied in the computer field and can solve problems such as data leakage, poor security of pseudo-random numbers, and low security of encrypted data
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
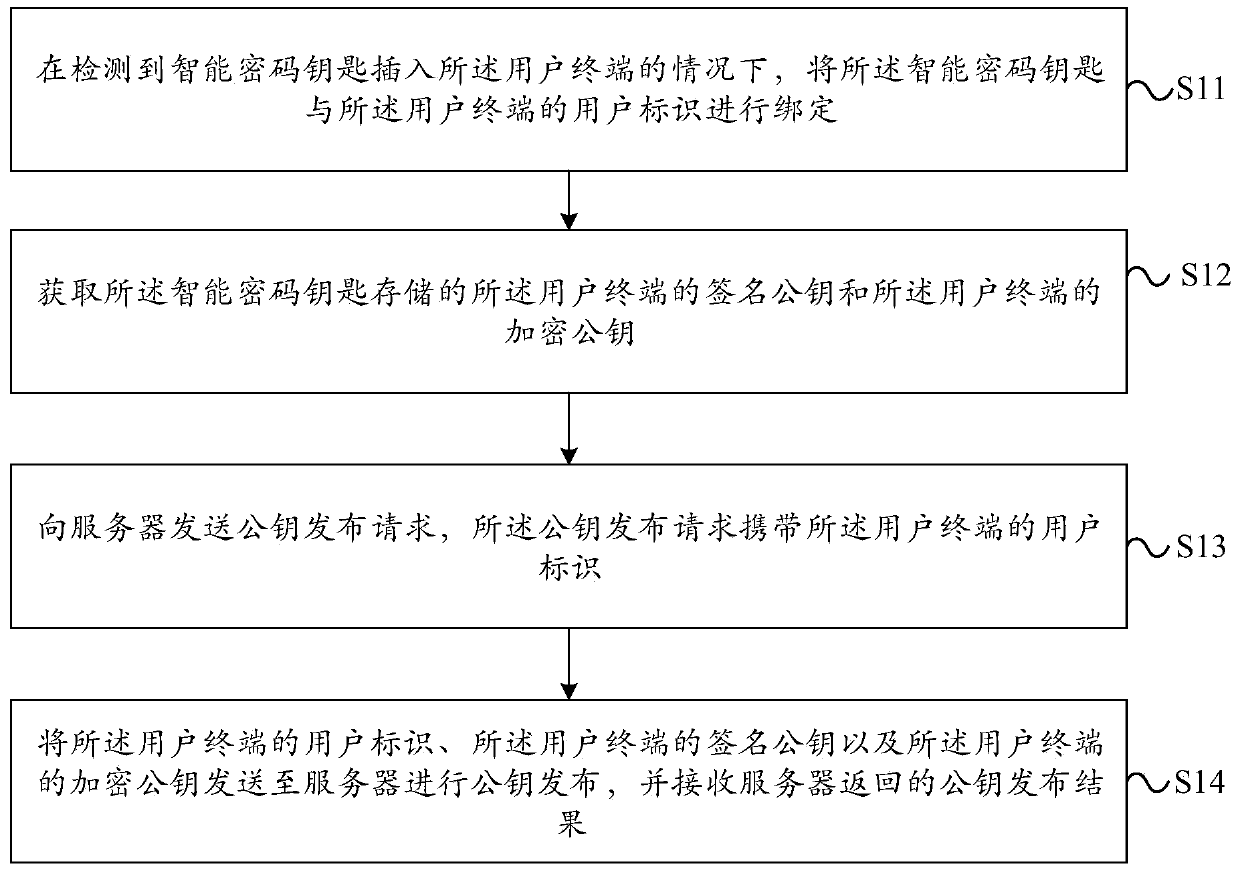
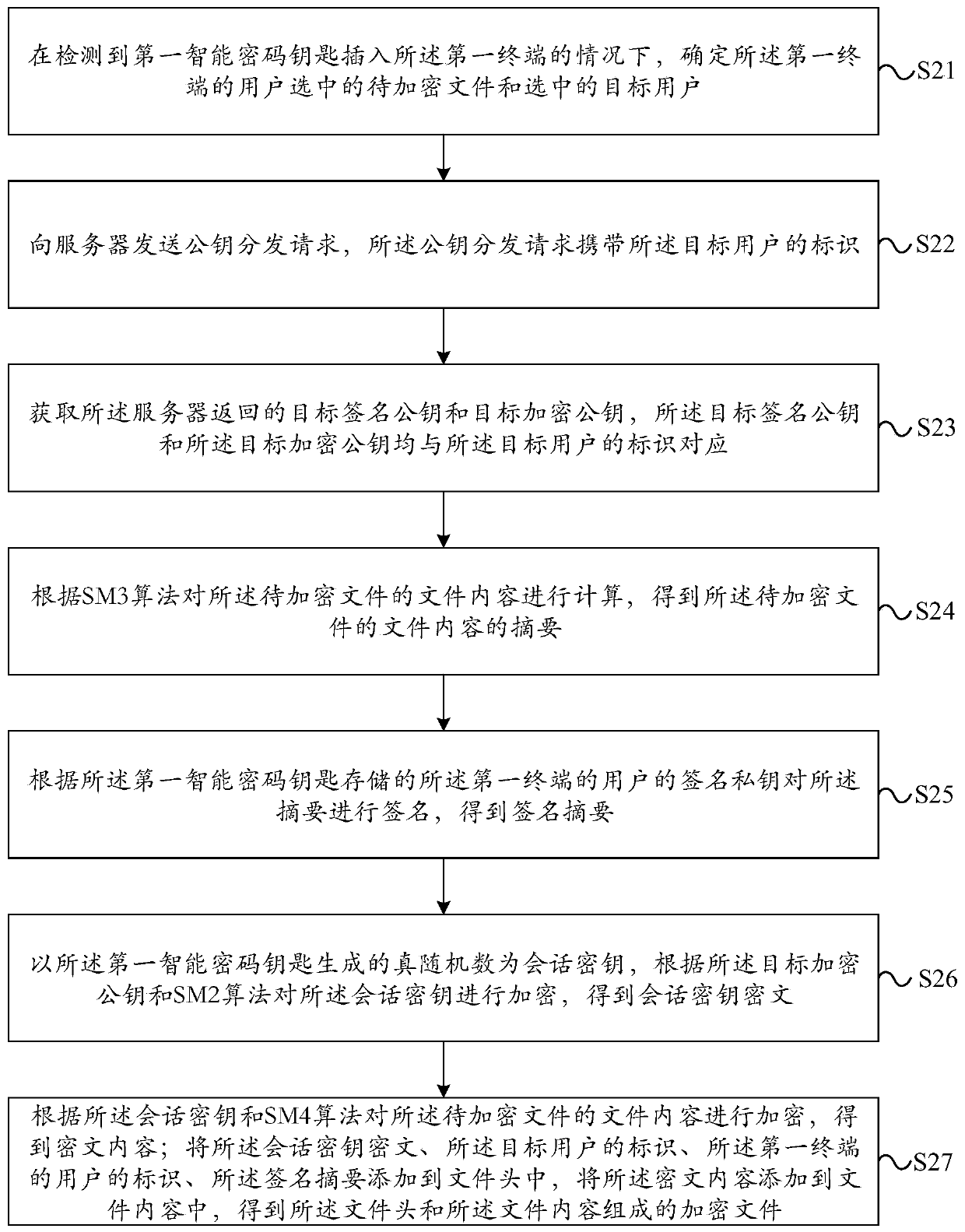
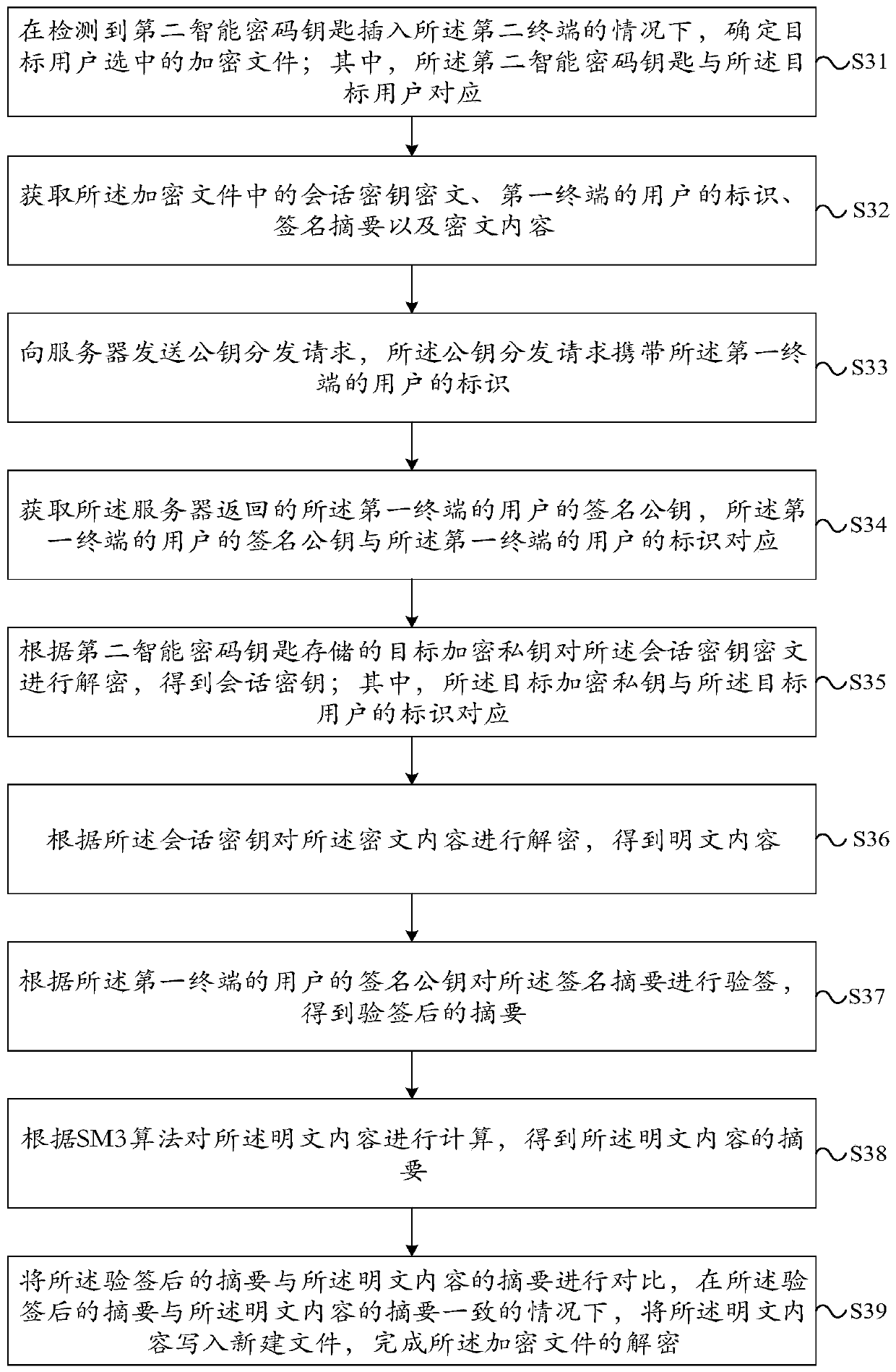
[0090] The technical solutions in the embodiments of the present application will be clearly and completely described below in conjunction with the accompanying drawings in the embodiments of the present application. Obviously, the described embodiments are part of the embodiments of the present application, rather than all of them. Based on the embodiments in this application, all other embodiments obtained by those of ordinary skill in the art without creative work shall fall within the protection scope of this application.
[0091] The inventor of the present application discovered in the process of implementing the present application that, in related technologies, the technical solution adopted for point-to-point encryption of data in the data leakage prevention system is: through the use of encrypted public and private keys and signature public and private keys embedded in the program , Pseudo-random number and RSA, DES, SHA1 and other algorithms to encrypt data point-to-poi...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More