Code protection method, device and system and readable storage medium
A technology for protection devices and storage media, which is applied in the direction of program/content distribution protection, etc., and can solve problems such as insufficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
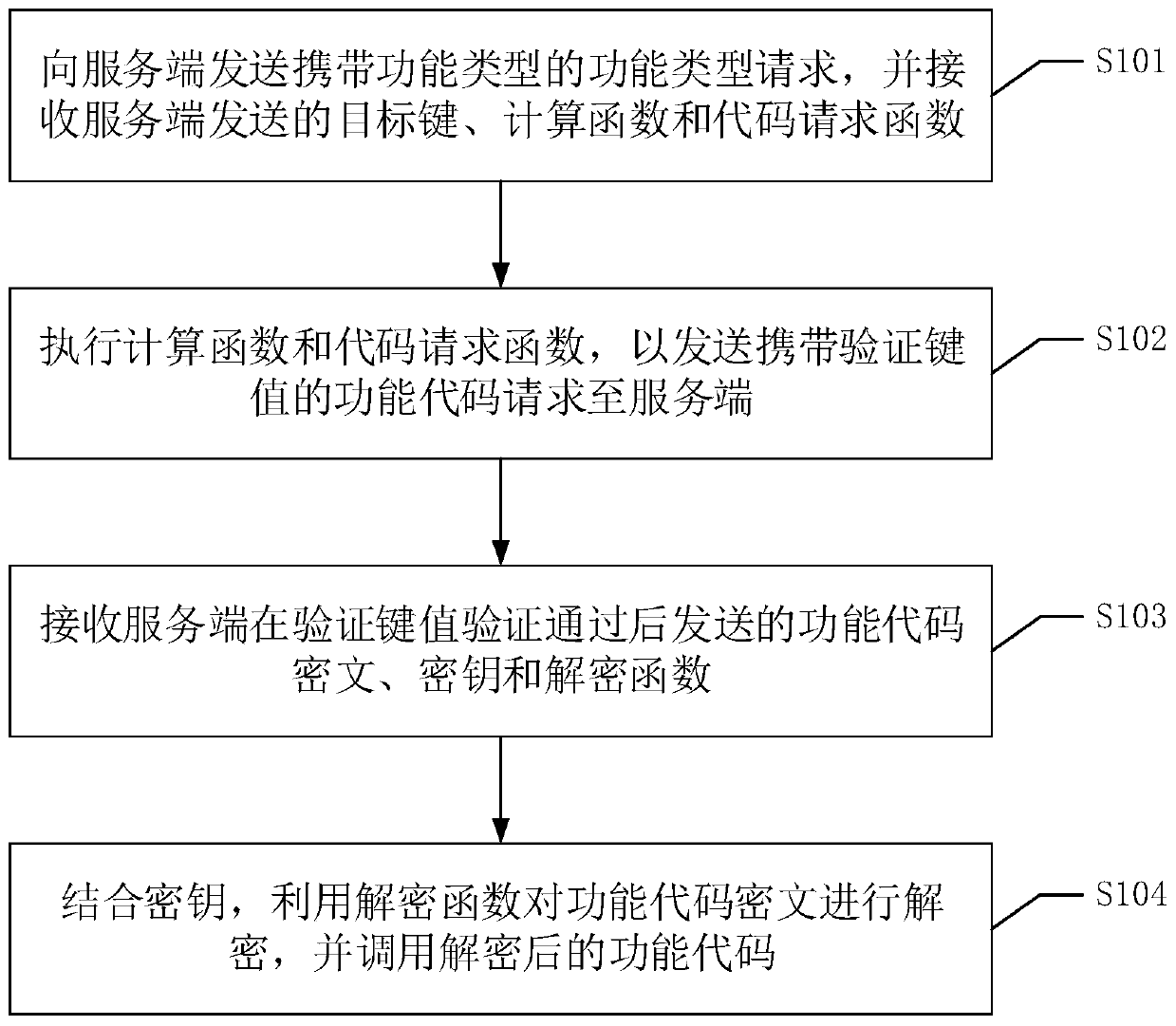
[0062] Please refer to figure 1 , figure 1 It is a flow chart of the first code protection method in the embodiment of the present application. This method can be applied to the client, and the method includes the following steps:
[0063] S101. Send a function type request carrying a function type to the server, and receive the target key, calculation function and code request function sent by the server.
[0064] The client (front end), such as the foreground part of the website, runs on browsers such as PCs and mobiles to display web pages for users to browse.
[0065] The server (backend) such as the background part of the website, that is, something invisible to the user, is usually used for data interaction with front-end engineers and storage and reading of website data.
[0066] In this embodiment, each function type that needs to keep the function code secret can be defined in advance, and a unique identifier can be set for each function type. In this way, the clien...
Embodiment 2
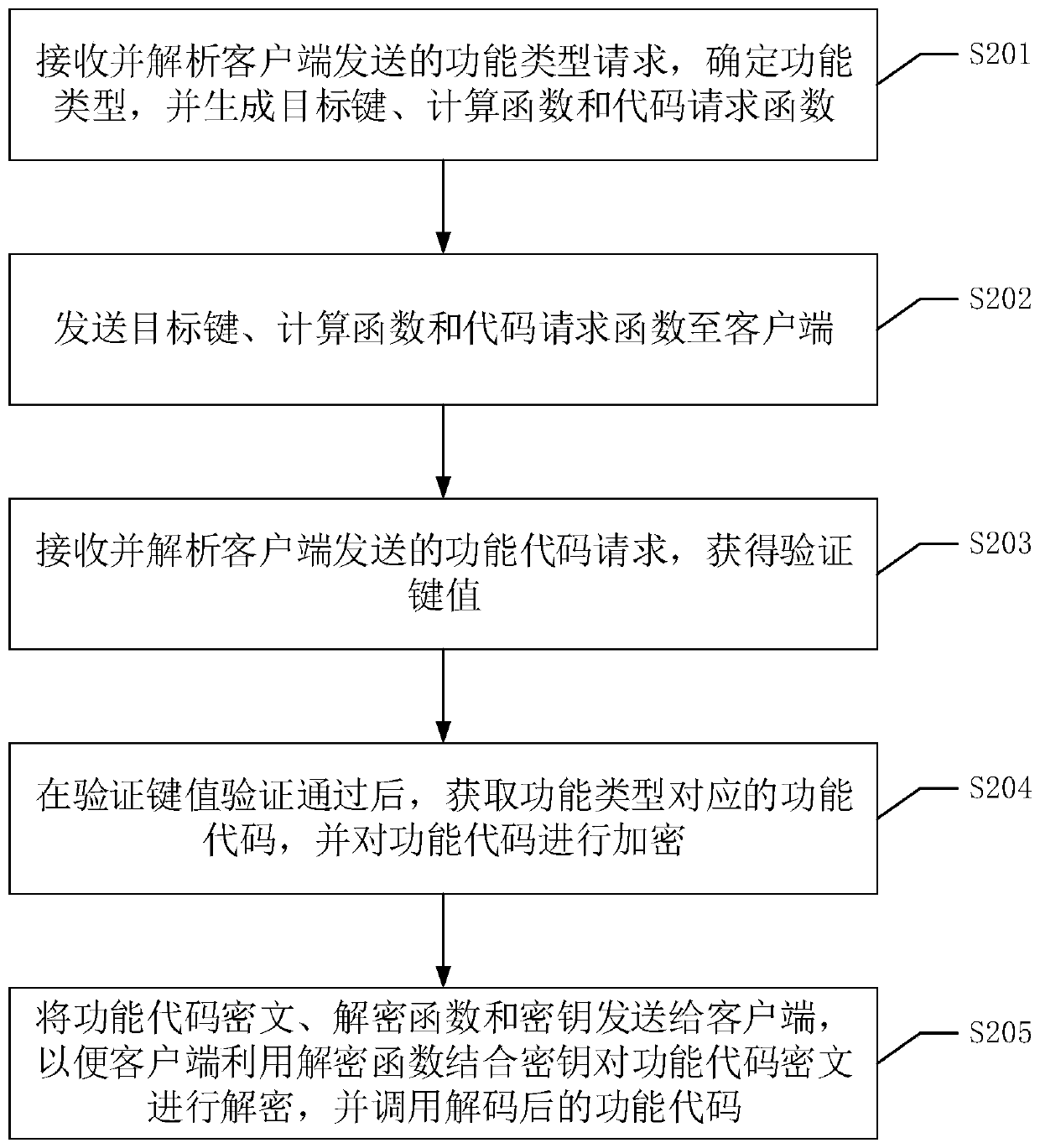
[0094] Based on the first embodiment above, this application also proposes another code protection method that can be applied to the server. The code protection method in the second embodiment and the code protection method in the first embodiment can be referred to each other, and the overlapping parts will not be repeated one by one. .
[0095] Please refer to figure 2 , figure 2 It is a flow chart of the second code protection method in the embodiment of the present application. The method can be applied to the server (such as a server running a backend or background), and the method includes the following steps:
[0096]S201. Receive and analyze the function type request sent by the client, determine the function type, and generate a target key, calculation function and code request function.
[0097] When the user has a demand for a certain function, the client can send a function type request to the server by operating the user interface.
[0098] After the server p...
Embodiment 3
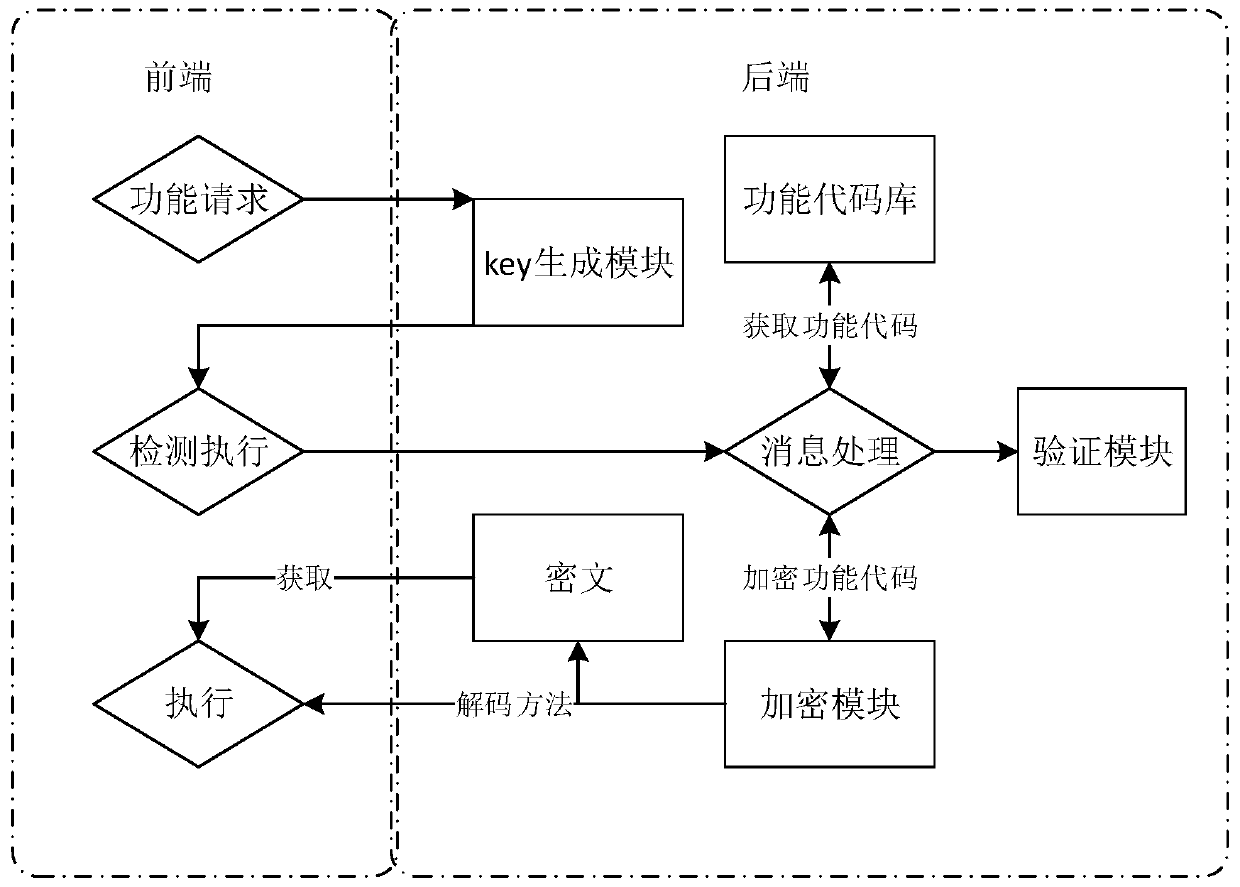
[0118] It should be noted that the above two code protection methods may be used alone or in combination in practical applications. The following uses a specific application scenario as an example to describe the combined application of the two in detail.
[0119] Such as image 3 As shown, the main modules of the system with code protection function are at the back end, which are Key generation module, function code library, verification module and encryption module. Among them, the Key generation module is used to generate Key after receiving the function type request sent by the front end; the function code library is used to store various function codes; the verification module is used to verify whether the key value is valid and correct, and the encryption module is used to Encrypt the function code.
[0120] Among them, the decryption method refers to the decryption function and key; the ciphertext refers to the function code ciphertext; the function request refers to ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More