Tracing analysis method for network attacks
An analysis method and network attack technology, applied in data exchange networks, digital transmission systems, electrical components, etc., can solve problems such as difficult detection, single node attacking other nodes, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
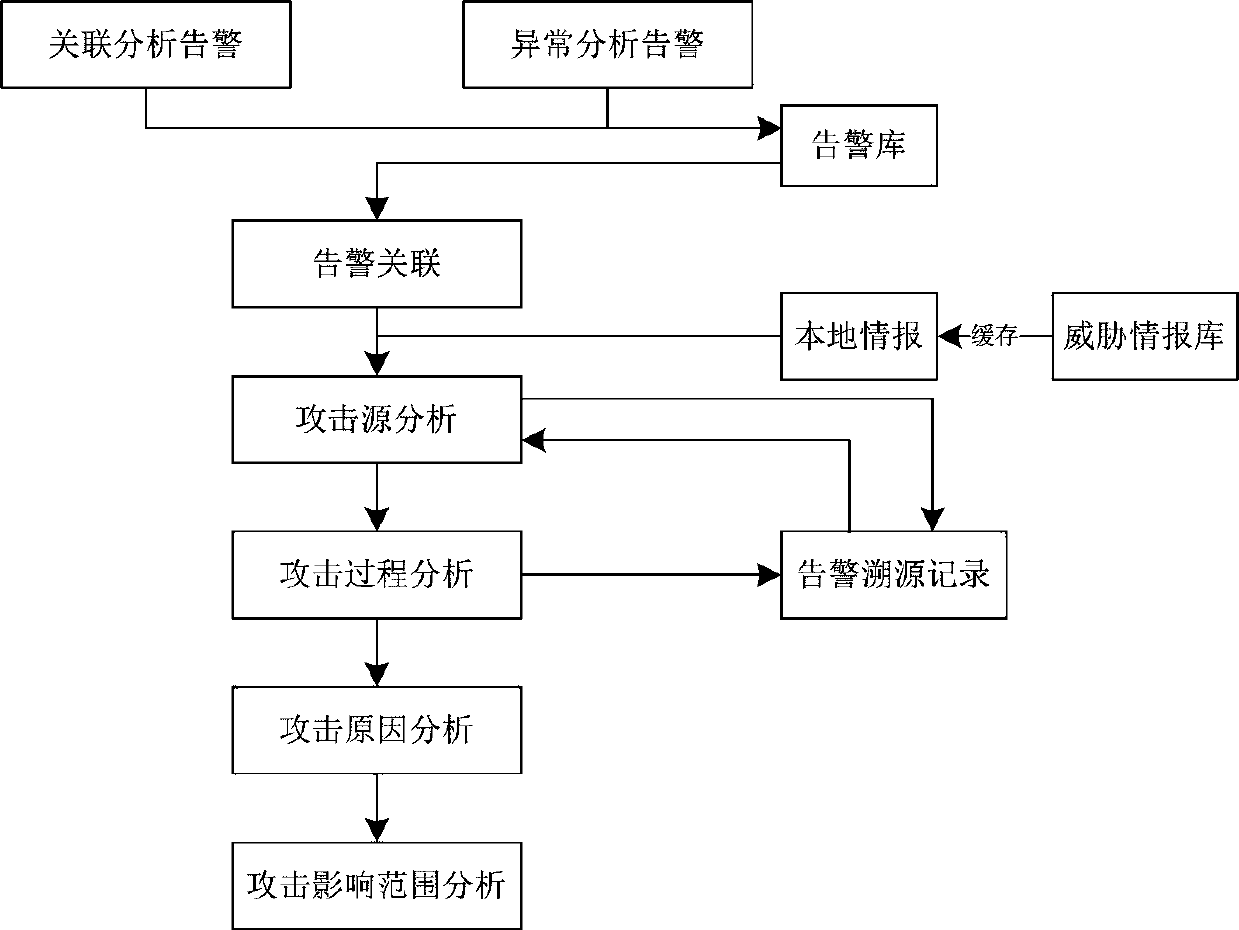
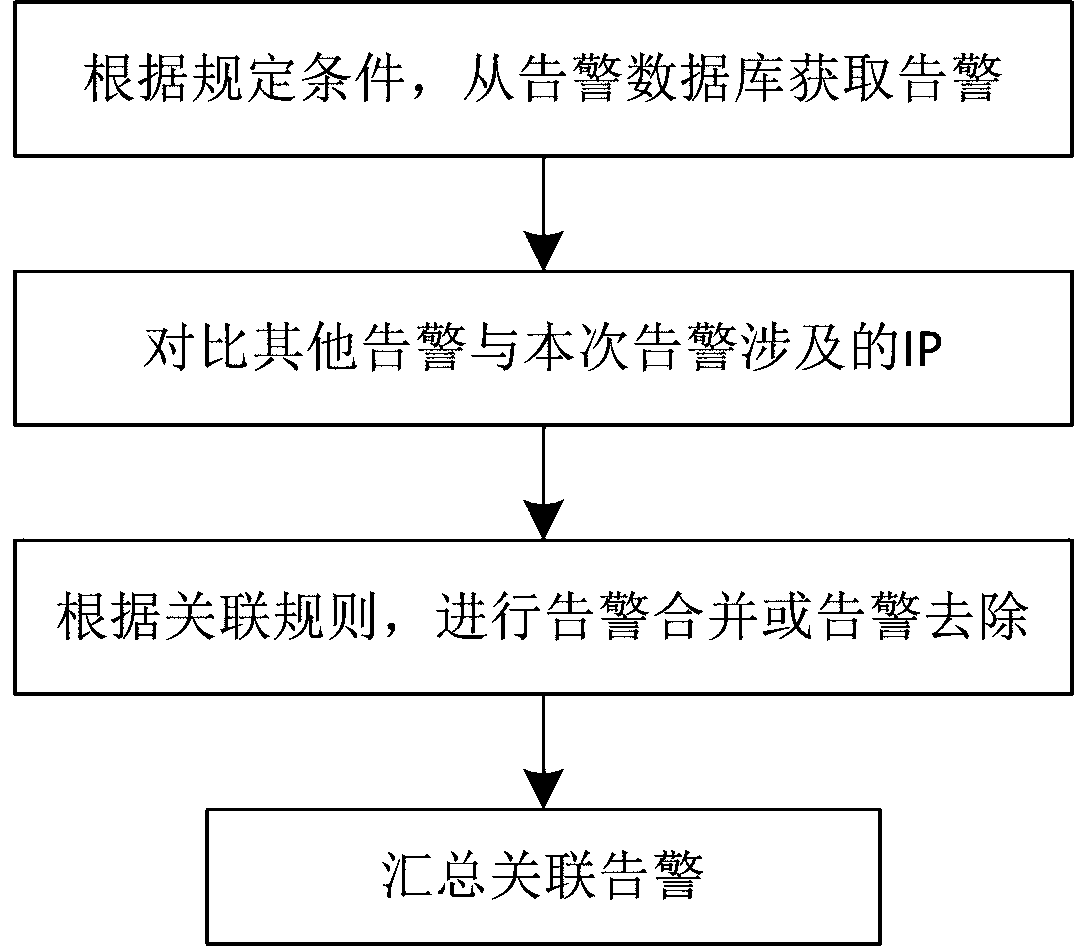
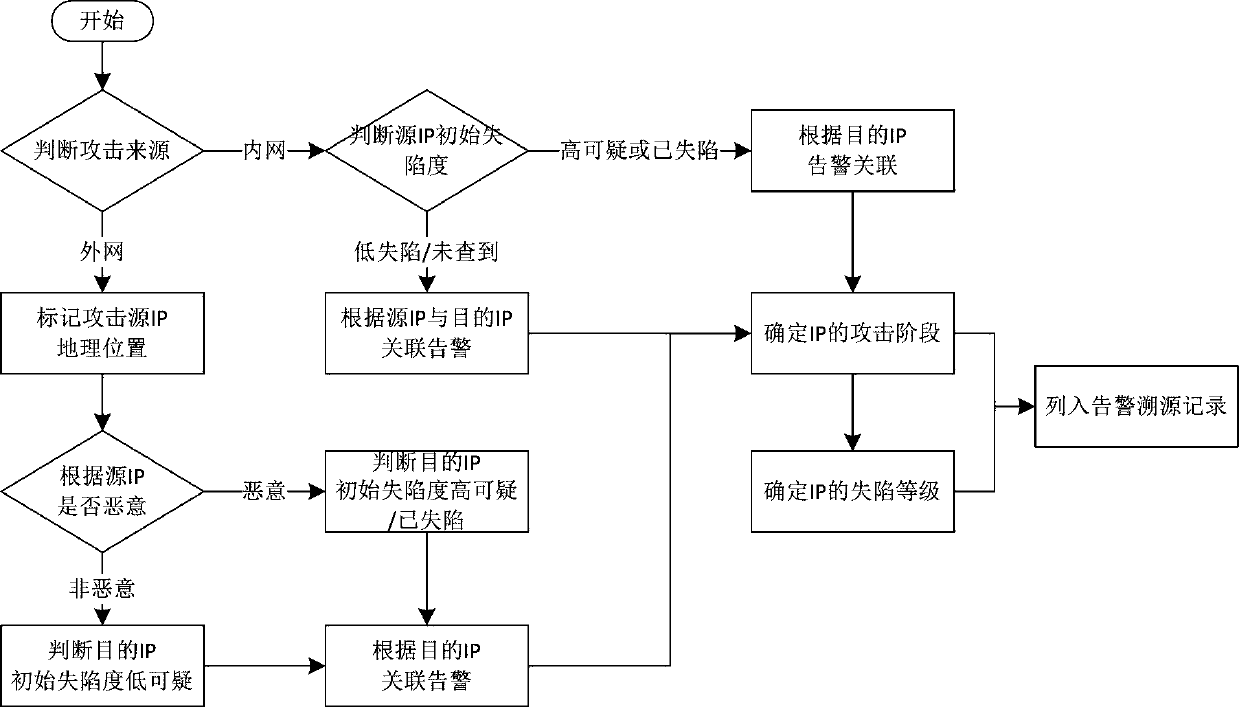
Method used
Image
Examples
Embodiment Construction
[0031] The technical solutions of the present invention will be described in detail below in conjunction with the drawings and embodiments; it should be understood that the specific embodiments described here are only used to explain the present invention, and are not intended to limit the present invention.
[0032] In order to facilitate the understanding of the embodiments of the present invention, a brief introduction of related technical terms is first introduced.
[0033] Threat, a potential cause of an unwanted incident that could result in harm to a system or organization.
[0034] Information security risk refers to the degree of impact on the organization after a security incident occurs due to the threat of exploiting the vulnerability of the information system.
[0035] Vulnerabilities, weaknesses of an asset or of several assets that may be exploited by threats.
[0036] Network traffic is the collection of data packets generated on the network by devices connect...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More