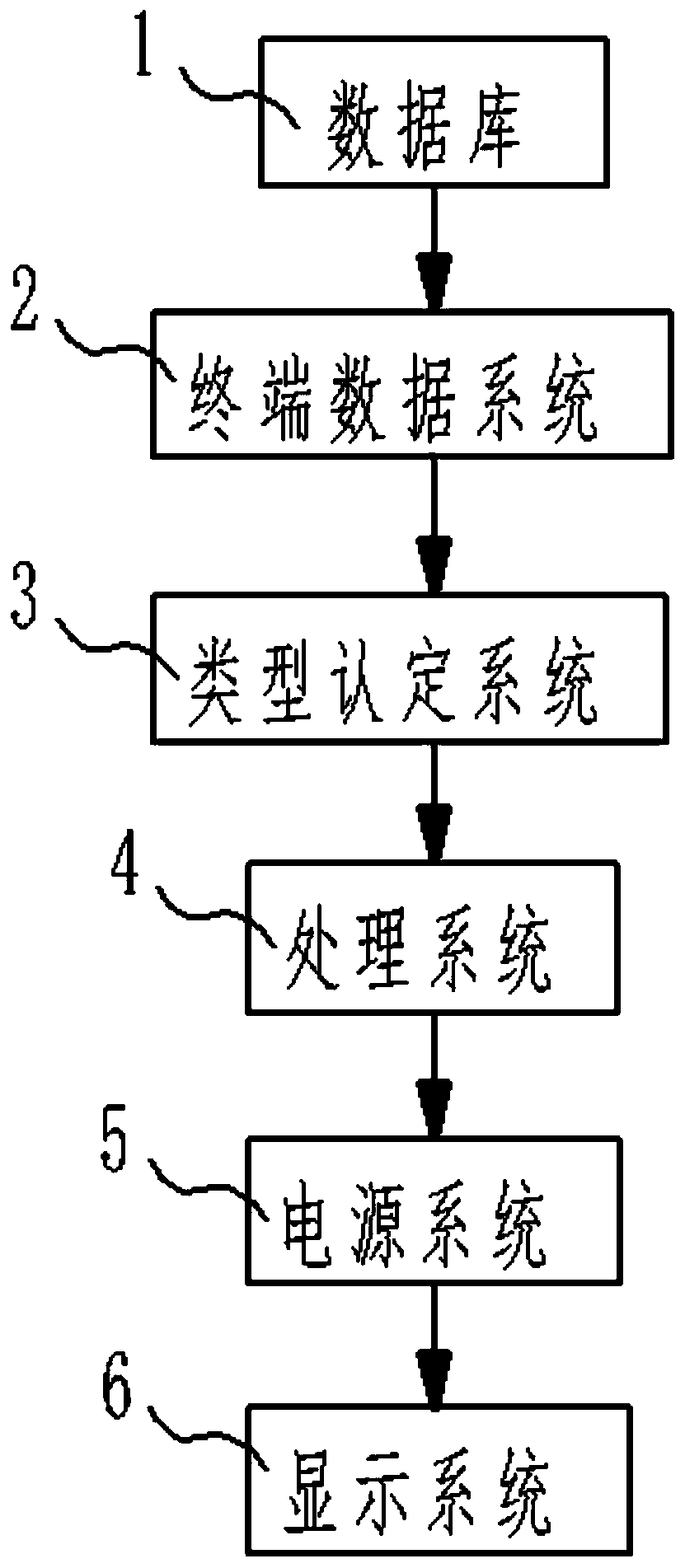
Network security monitoring equipment
A technology for monitoring equipment and network security, applied in the field of network security to achieve the effect of improving user information
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
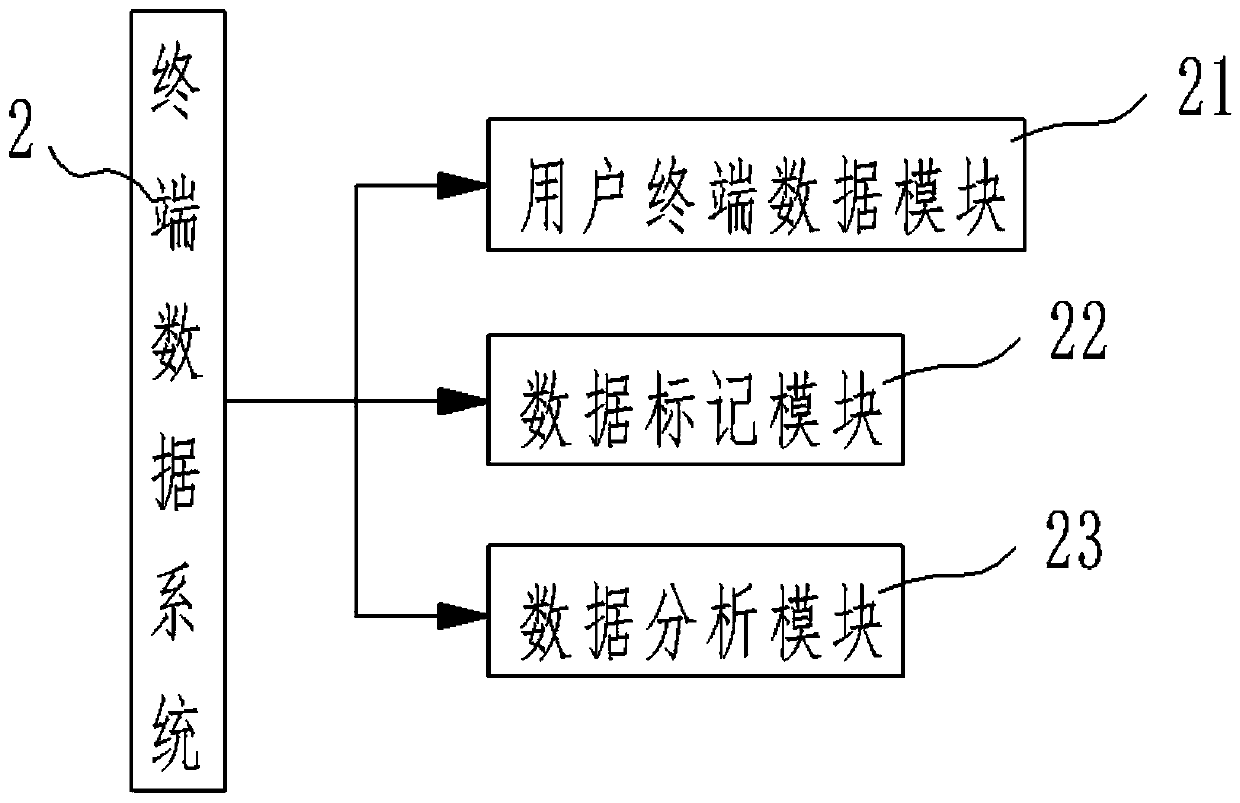
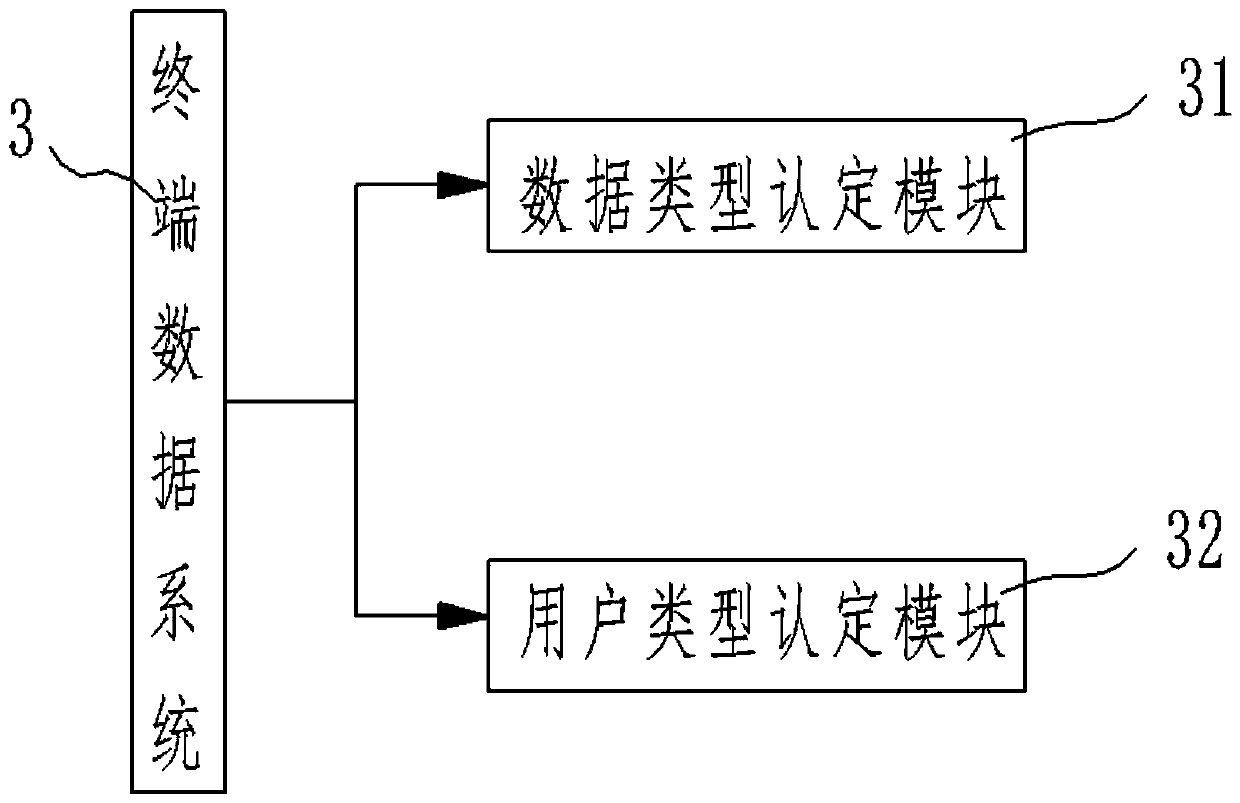
Embodiment Construction
[0026] The present invention will be further described below in conjunction with the examples.
[0027] The following examples are used to illustrate the present invention, but cannot be used to limit the protection scope of the present invention. The conditions in the embodiment can be further adjusted according to the specific conditions, and the simple improvement of the method of the present invention under the premise of the concept of the present invention belongs to the protection scope of the present invention.
[0028] It should be noted that, in the description of the invention, terms such as "upper", "lower", "left", "right", "inner", "outer" and other indicated directions or positional relationships are based on the terms shown in the accompanying drawings. Orientation or positional relationship, which is only for convenience of description, and does not indicate or imply that the device or element must have a specific orientation, be constructed and operated in a ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More