Watermark embedding method, watermark reading method and watermark system based on desensitized data
A watermark embedding and data technology, applied in the field of data security, can solve the problems of unable to prove data leakage, data unable to be watermarked, unfavorable data security protection, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0038] The specific embodiments of the present invention will be further described below in conjunction with the accompanying drawings. It should be noted here that the descriptions of these embodiments are used to help understand the present invention, but are not intended to limit the present invention. In addition, the technical features involved in the various embodiments of the present invention described below may be combined with each other as long as they do not constitute a conflict with each other.
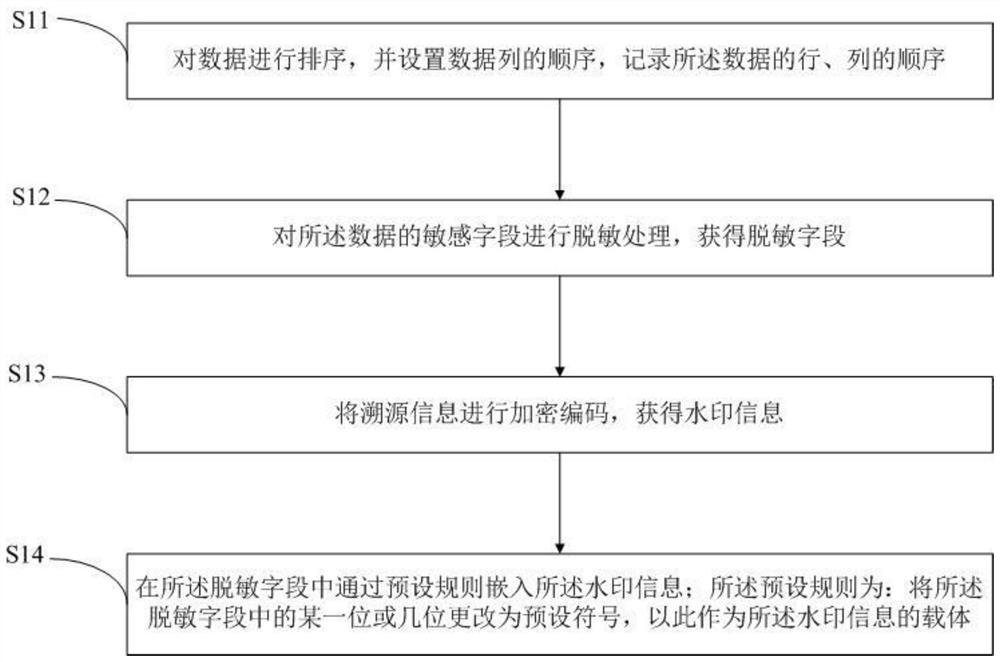
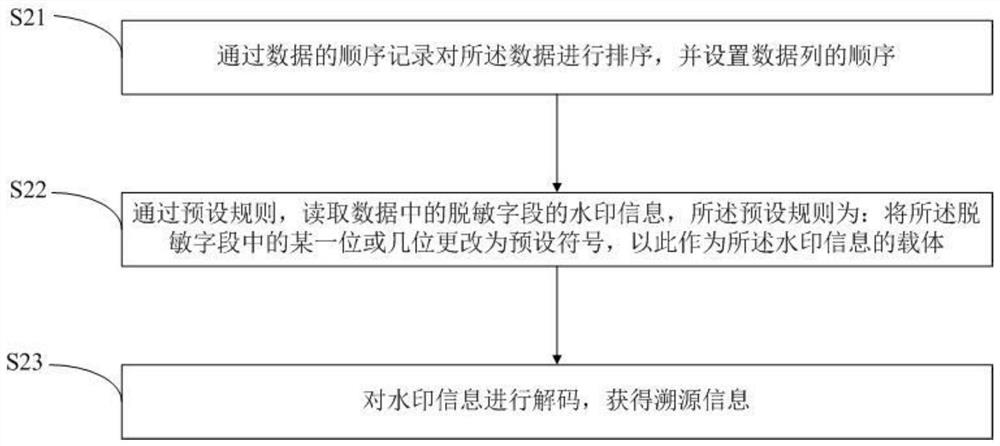
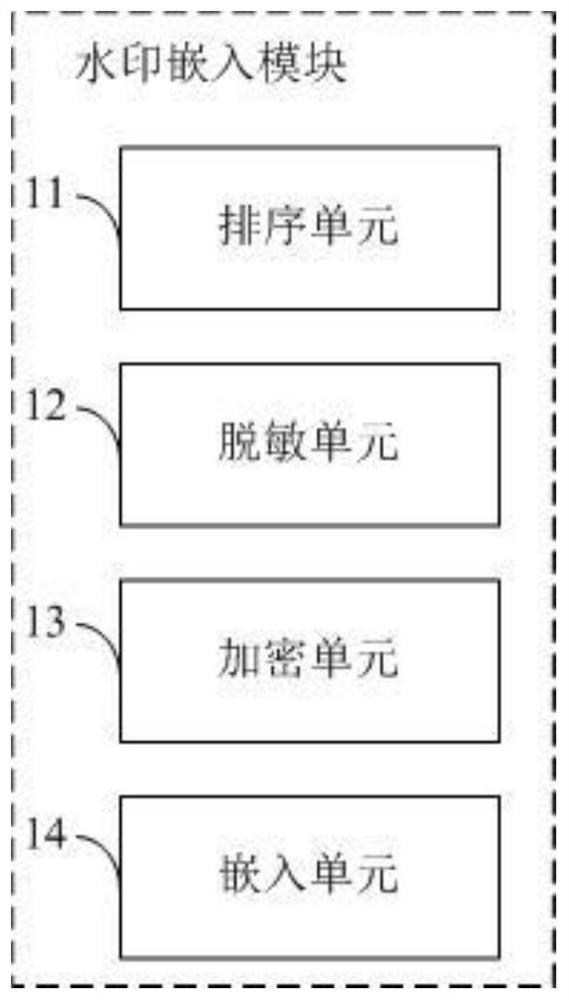
[0039] The technical solution of the present invention is: on the one hand, the present invention proposes a kind of watermark embedding method based on desensitized data, comprising steps:
[0040] S10: Log in to the watermark system; sort the data, set the order of the data columns, and record the order of the rows and columns of the data; when reading the watermark later, it is necessary to restore the order of the data according to the order of the rows and columns o...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More