Authentication method and system based on certificateless clustering signatures and without bilinear pairs
An authentication method and linear pairing technology, applied in the fields of information security and confidential communication, can solve problems such as low efficiency and achieve the effect of improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0021] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings.
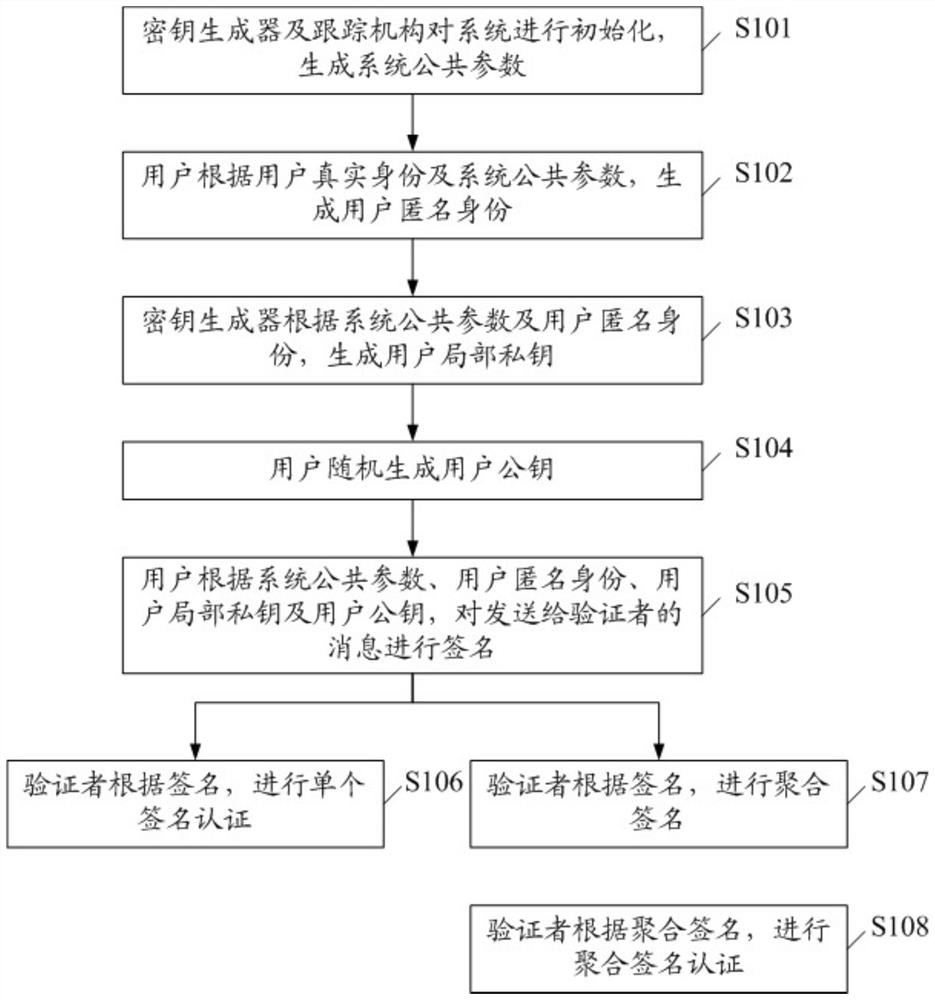
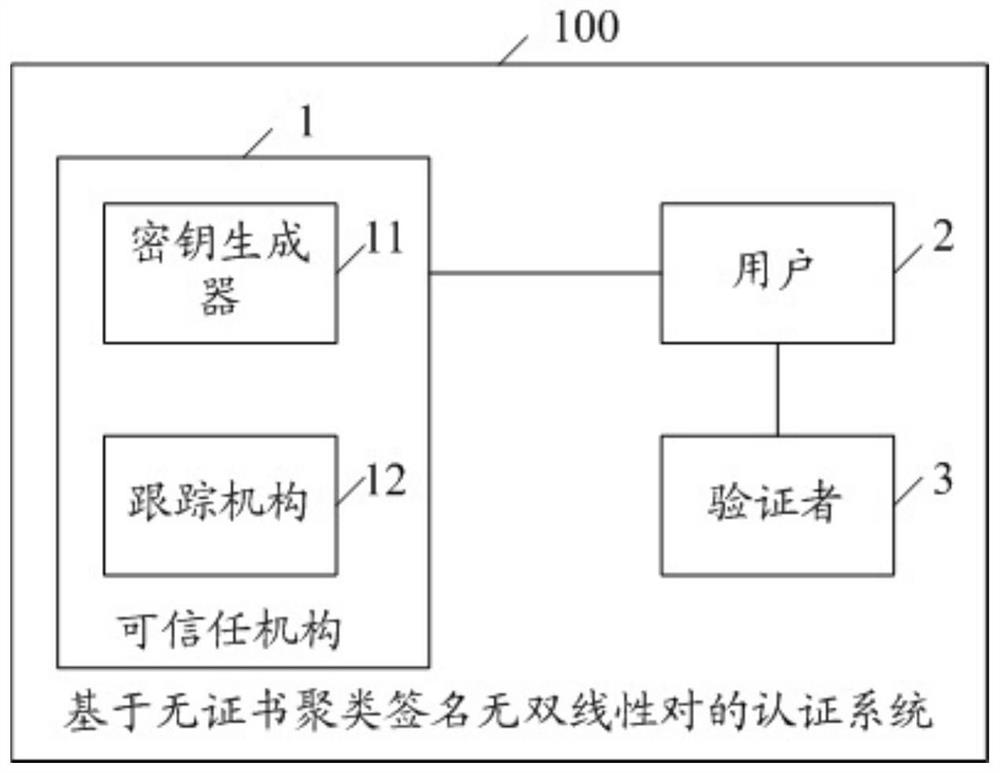
[0022] see figure 1 , figure 1 It shows a flow chart of an embodiment of the authentication method based on certificateless clustering signature without bilinear pairing of the present invention, which includes:
[0023] S101, the key generator and the tracking mechanism initialize the system and generate system public parameters;
[0024] S102, the user generates an anonymous user identity according to the user's real identity and system public parameters;
[0025] S103, the key generator generates the user's local private key according to the system public parameters and the user's anonymous identity;
[0026] S104, the user randomly generates a user public key;
[0027] S105, the user signs the message sent to the verifier according to the system public par...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More