Communication link establishment method and device, storage medium, processor and system
A technology for establishing a method and a communication link, which is applied in the field of data encryption, can solve problems such as the anti-VPN technology is easy to be cracked, and achieve the effect of not being easy to be cracked and solving the problem of being easy to be cracked
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0046] According to an embodiment of the present invention, an embodiment of a method for establishing a communication link is also provided. It should be noted that the steps shown in the flowcharts of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions, Also, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
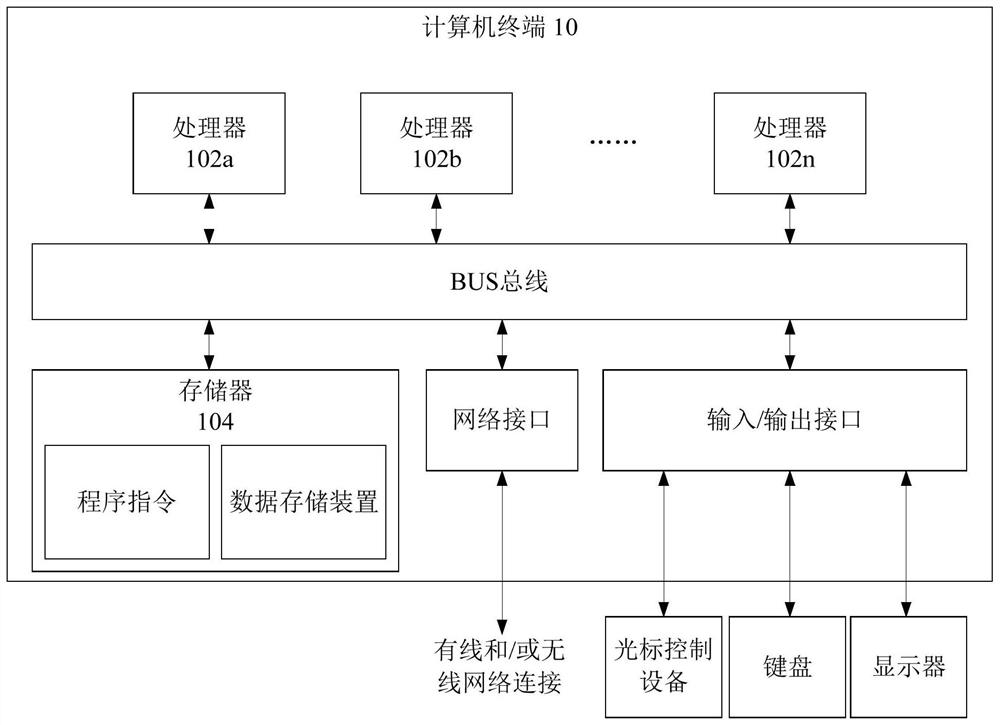
[0047] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. figure 1 A block diagram of a hardware structure of a computer terminal (or mobile device) for implementing a method for establishing a communication link is shown. Such as figure 1 As shown, the computer terminal 10 (or mobile device) may include one or more (shown by 102a, 102b, ..., 102n in the figure) processor 102 (...
Embodiment 2
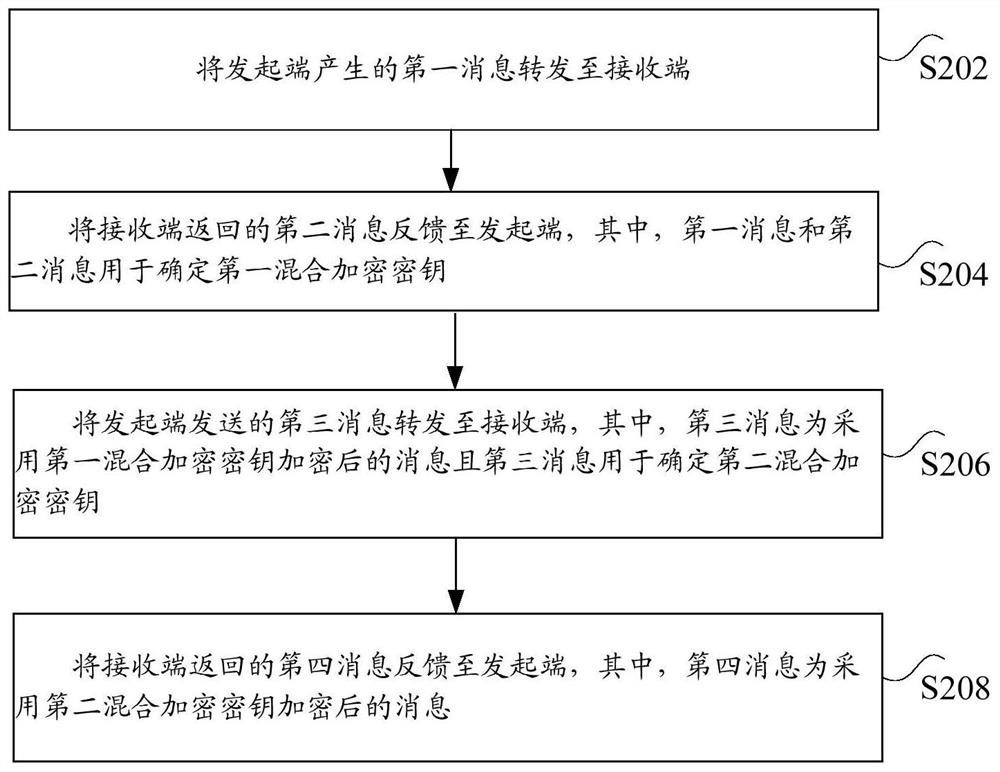
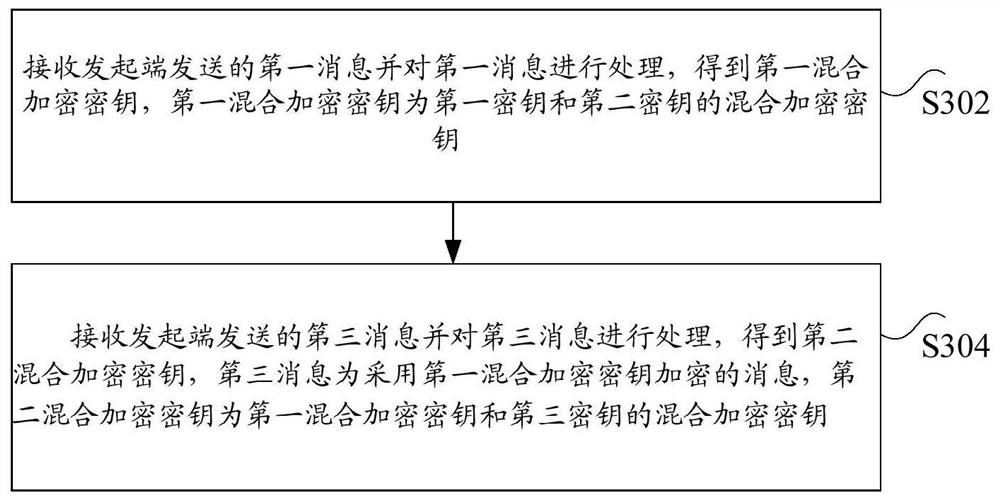
[0078] In an embodiment of the present invention, a method for establishing a communication link is provided, image 3 is a flow chart of the second method for establishing a communication link provided according to an embodiment of the present invention, such as image 3 As shown, the process includes the following steps:
[0079] Step S302, receiving the first message sent by the initiator and processing the first message to obtain a first mixed encryption key, which is a mixed encryption key of the first key and the second key;
[0080] Step S304, receiving the third message sent by the initiator and processing the third message to obtain a second mixed encryption key, the third message is a message encrypted with the first mixed encryption key, and the second mixed encryption key is the first mixed encryption key A mixed encryption key and a mixed encryption key of the third key.
[0081] As an optional embodiment, the first mixed encryption key is a mixed encryption key...
Embodiment 3
[0087] In an embodiment of the present invention, a method for establishing a communication link is provided, Figure 4 It is a flow chart of the third method for establishing a communication link provided according to an embodiment of the present invention, such as Figure 4 As shown, the process includes the following steps:
[0088] Step S402, the initiator and the receiver negotiate a first predetermined key, a first predetermined algorithm, and a second predetermined algorithm;
[0089] Step S404, the initiator and the receiver determine the encryption key for the negotiation process according to the first predetermined key, the first predetermined algorithm, and the second predetermined algorithm, and the encryption key is the key obtained by the first predetermined key and the first predetermined algorithm and a mixed encryption key of the key obtained by the second predetermined algorithm.
[0090] As an optional embodiment, the first message and the second message a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More