Software safety defect library system based on attack mode and management method thereof
A software security and defect technology, which is applied in the field of software security defect discovery and resolution based on attack patterns, can solve problems such as not being able to combine system attack patterns well, not systematically combining attackers, etc., to achieve rich defect semantic information, input High library operation efficiency and the effect of improving work efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
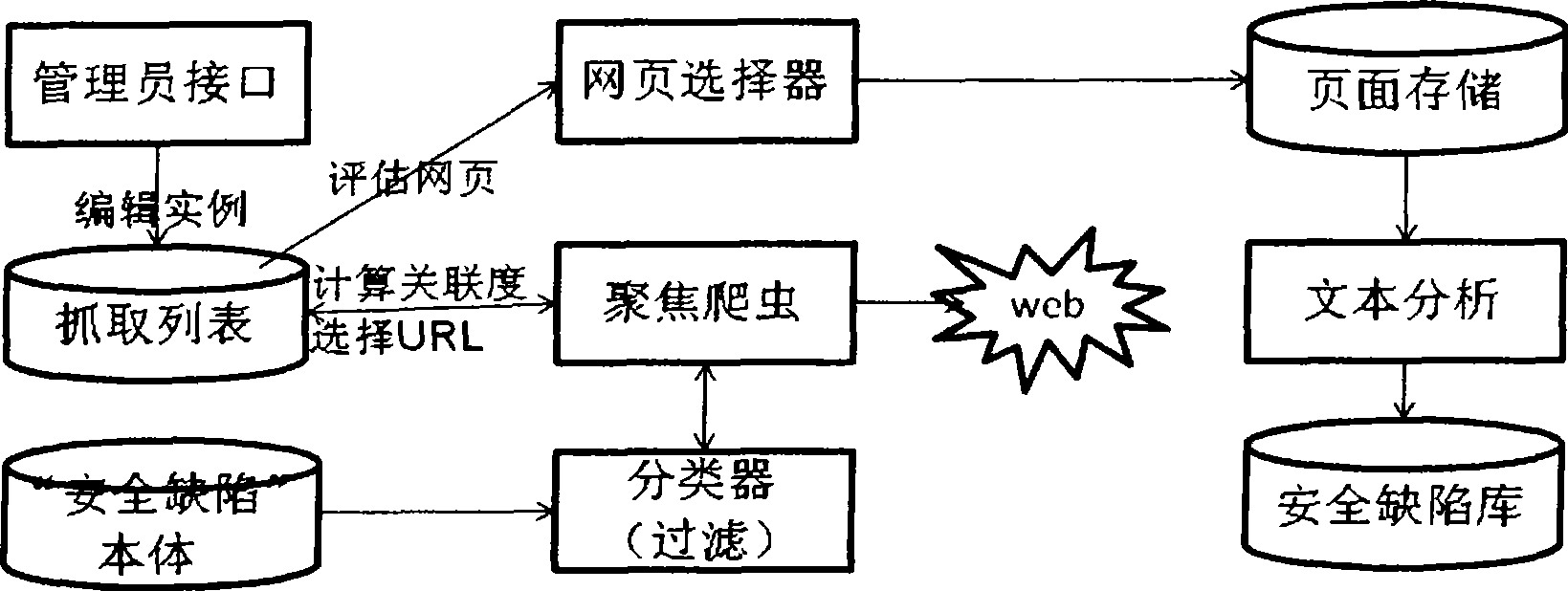
[0028] Effective classification and management of defects is conducive to improving the management level and quality of software projects. By establishing a security defect library to dynamically collect and manage software defects, it provides a favorable space for the storage, classification and management of software defects. To achieve this goal, a defect classification method for secure software defect libraries needs to be developed. The purpose of classification is to measure software defects and analyze the process causes of software defects, improve the software process, prevent software defects, improve software quality, and improve the maturity of the organization's software development capabilities.
[0029] Design idea of the present invention comprises:
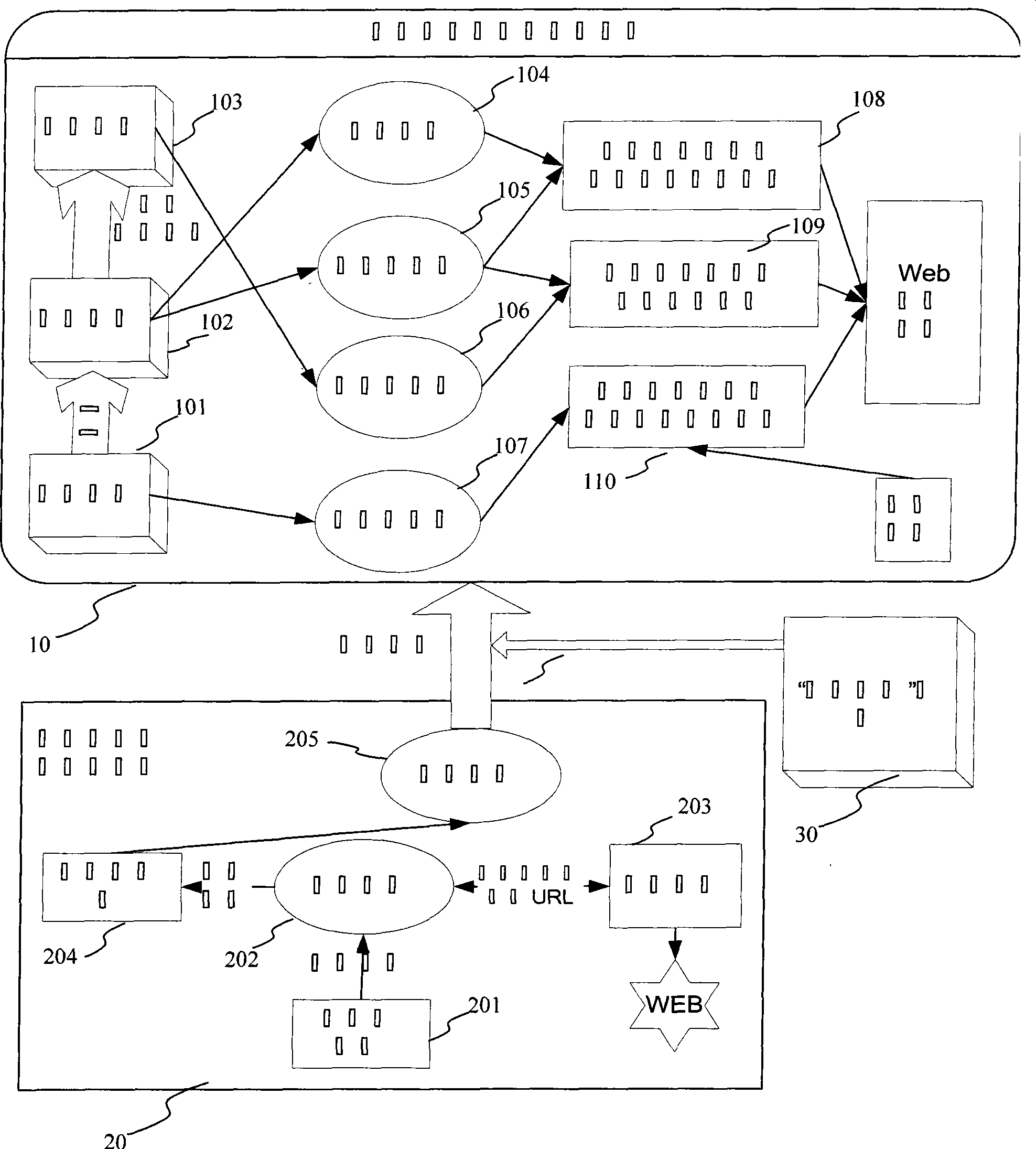
[0030] 1) Study the classification system of attack patterns and software defects, summarize the mapping relationship from attack patterns to software defect structures, and give a formalized security softwar...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More