Outsourcing decryption method of attribute-based encryption based on ciphertext policy
A technology of attribute encryption and ciphertext, which is applied in the field of outsourced decryption of attribute-based encryption based on ciphertext strategy, and can solve problems such as occupying large network bandwidth resources
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The technical solutions of the present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. The following examples are implemented on the premise of the technical solutions of the present invention, and detailed implementation methods and processes are given, but the protection scope of the present invention is not limited to the following examples.
[0034] In order to better understand the method proposed in this embodiment, a corporate encrypted file sharing event is selected. In the event, there is a data owner, two access users (user A has the attributes of "technical department and manager"; user B has the attributes of "personnel department" and "supervisor") and a shared file m.
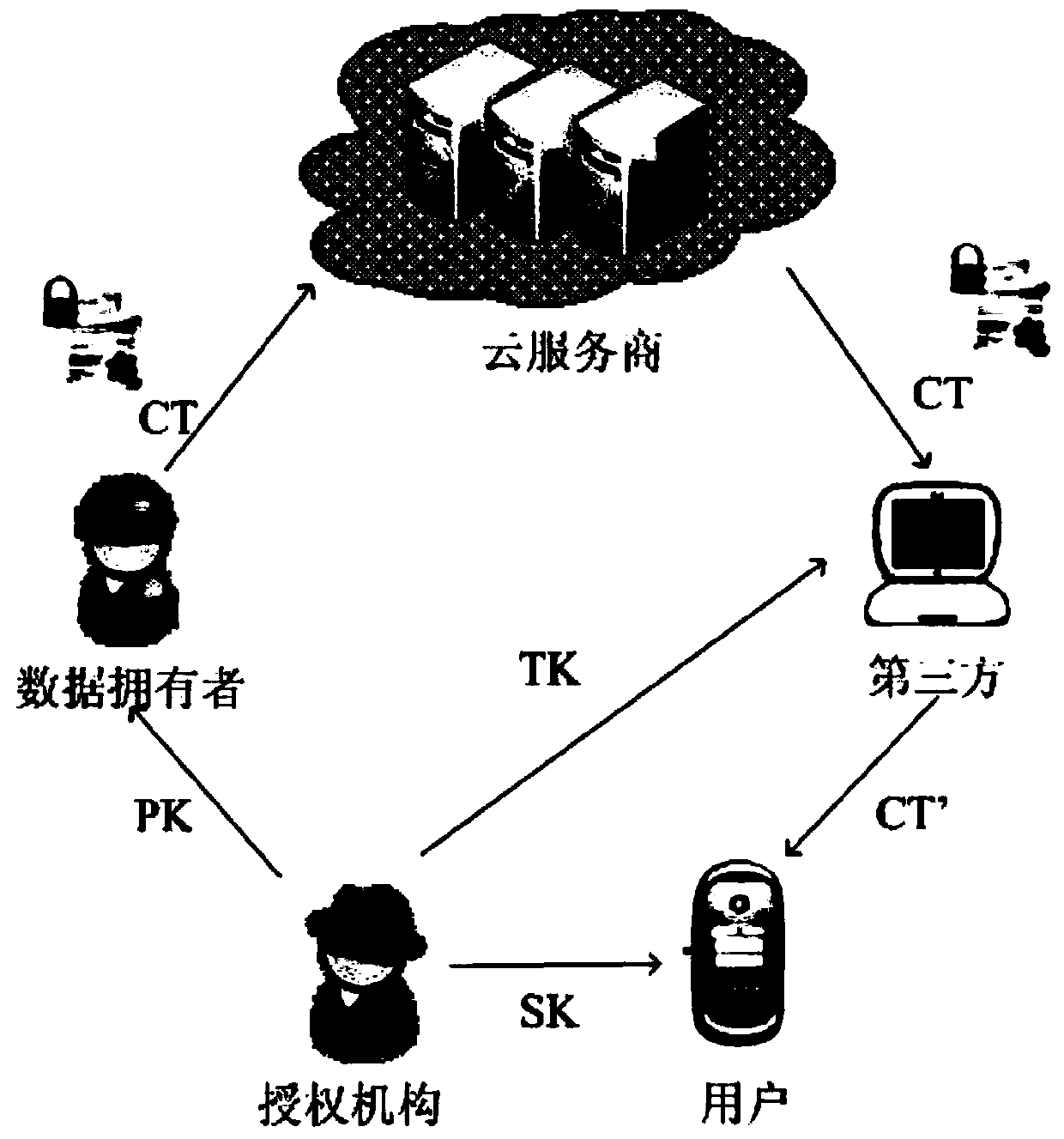
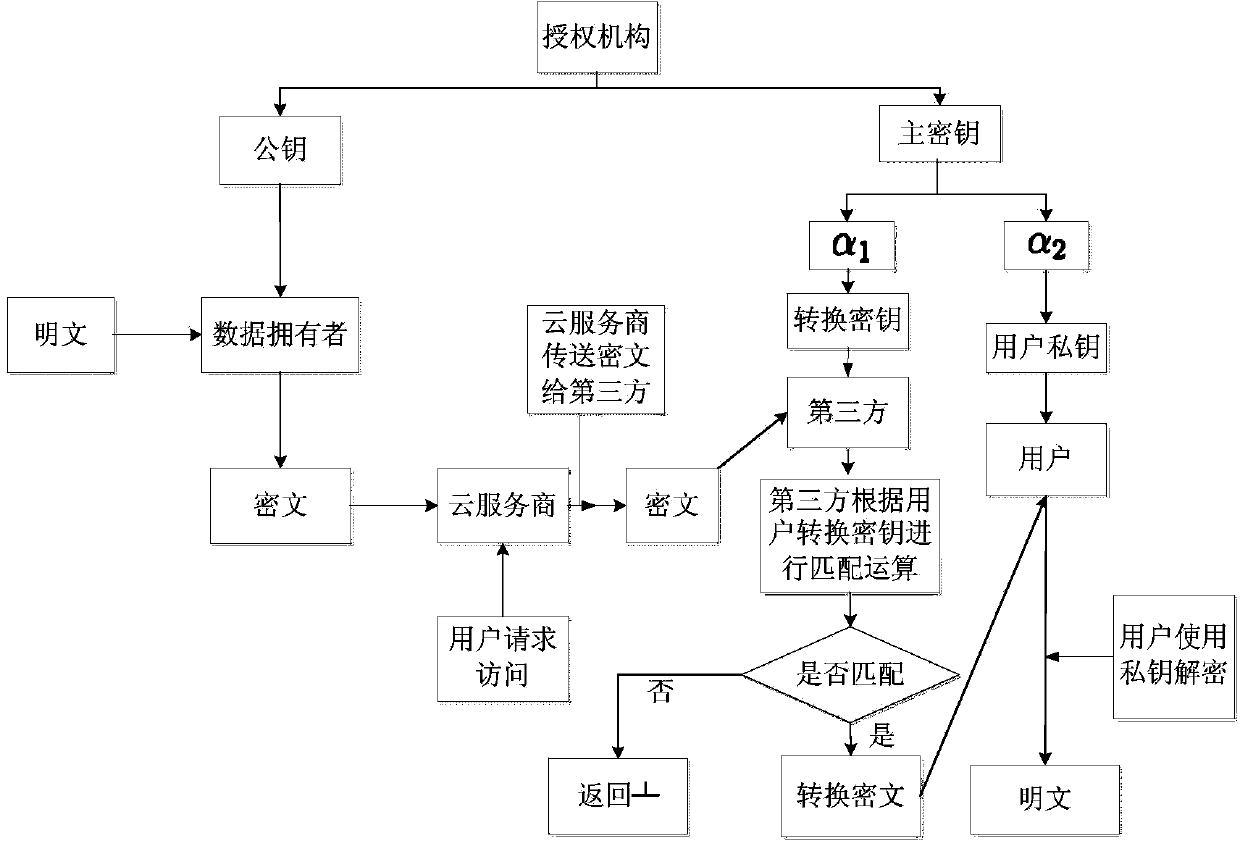
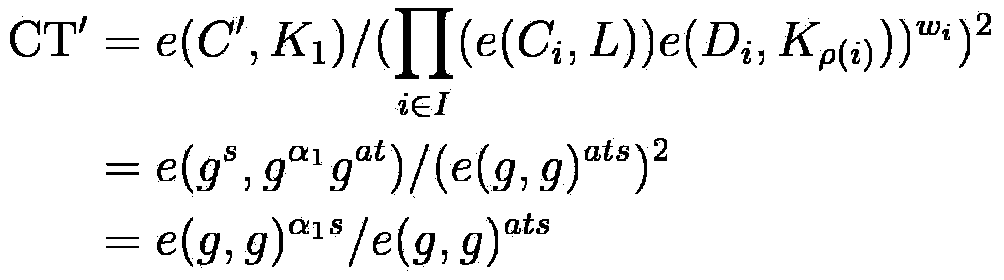
[0035] As the method structural diagram of the present invention ( figure 1 ), the specific implementation steps of this embodiment are as follows:
[0036] 1. System initialization
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More