SDN framework integrating threat processing and route optimizing and operating method
A working method and threat processing technology, applied in the field of network security, can solve problems such as network security, achieve the effect of ensuring communication quality, realizing efficient detection and flexible processing, and reducing coupling correlation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
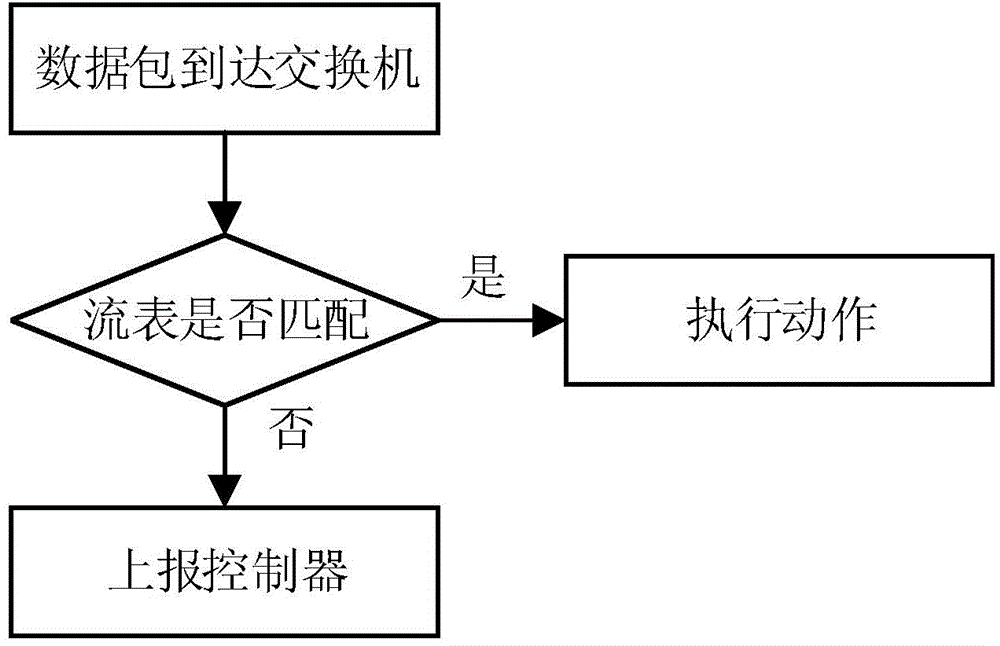
[0063] figure 2 A block diagram of the SDN network architecture of the present invention is shown.
[0064] Such as figure 2 As shown, a kind of SDN network framework, comprises: application plane, data plane and control plane; Wherein data plane, when being positioned at any IDS (being intrusion detection equipment) equipment in the data plane detects the message of DDoS attack characteristic, namely Report to the application plane through the SSL communication channel; the application plane is used to analyze the attack type, and customize the corresponding attack threat processing strategy according to the attack type; the control plane provides the attack threat processing interface for the application plane, and provides the most Optimal path computation and / or attack threat identification interface.
[0065] Among them, the characteristics of DDoS attack are defined as: spoofing of link layer and Internet layer addresses, abnormal behavior of Internet layer and trans...
Embodiment 2
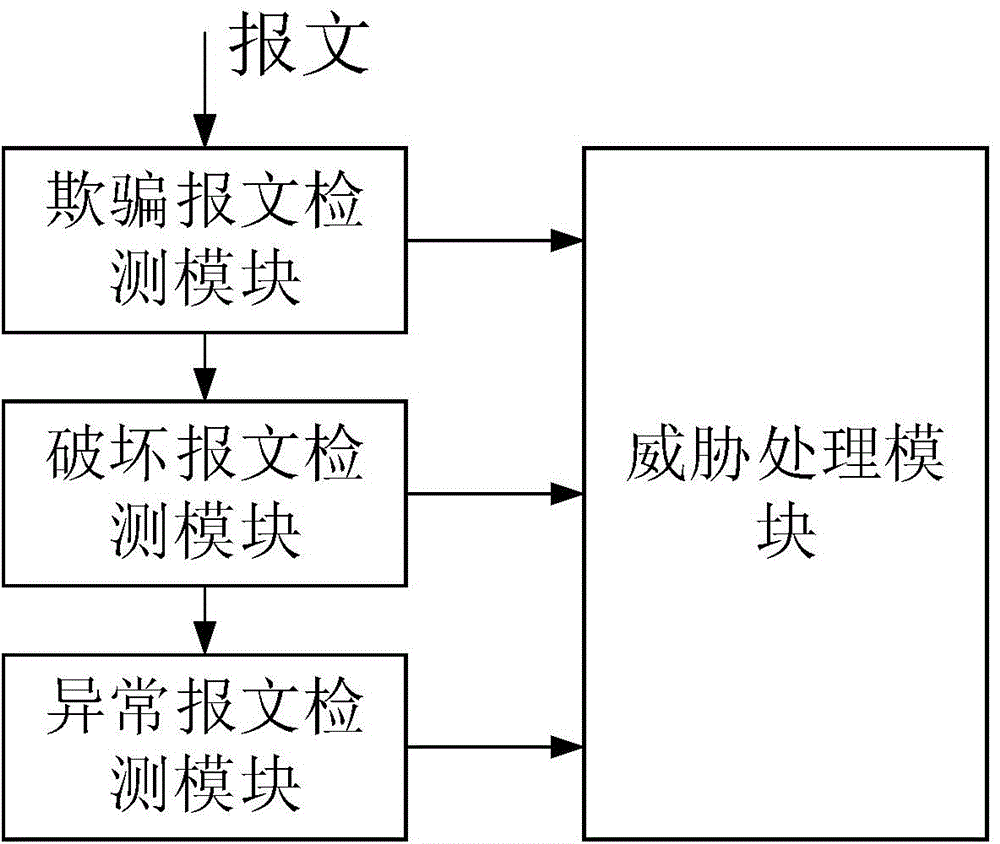
[0072] image 3 A structural block diagram of the SDN system of the present invention is shown.
[0073] Such as image 3 As shown, a working method based on the DDoS threat filtering SDN system includes: when any IDS device detects a message with a DDoS attack feature, it reports to the IDS decision server through the SSL communication channel; According to the reported information, the IDS decision server formulates a processing policy corresponding to the message with DDoS attack characteristics, and then shields the message through the controller or redirects the traffic of the switch access port corresponding to the message to the traffic cleaning center to filter.
[0074] Figure 4 A functional block diagram of the SDN system is shown.
[0075] Such as Figure 4 As shown, further, the IDS equipment includes:
[0076] Spoofed message detection module detects spoofing behavior of link layer and Internet layer addresses;
[0077] Destroy the message detection module...
Embodiment 3
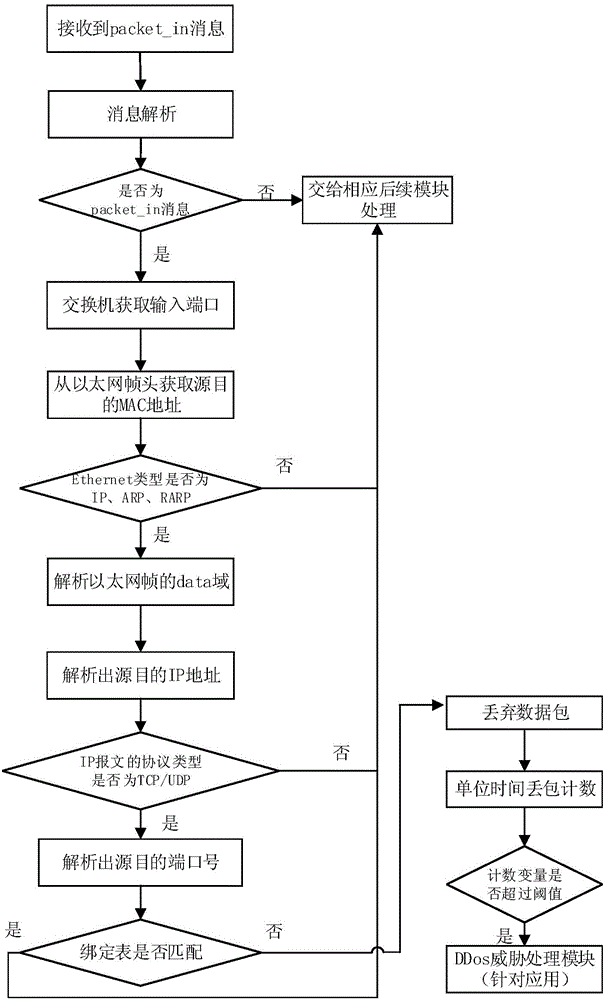
[0163] Based on Embodiment 1 and Embodiment 2, a working method of an SDN system that integrates threat processing and routing optimization can effectively reduce the workload of the controller through distributed detection and centralized processing. Improved detection efficiency and data transfer rate.
[0164] The working method of the SDN system integrating threat processing and routing optimization of the present invention comprises the following steps:
[0165] Step S100, network initialization; Step S200, distributed DDoS threat monitoring; and Step S300, threat processing and / or route optimization.
[0166] Further, the devices involved in network initialization in step S100 include: a controller, an IDS decision server and distributed IDS devices;
[0167] The steps of network initialization are as follows:
[0168] Step S101, the IDS decision server establishes a dedicated SSL communication channel with each IDS device (this step S101 is an optional implementation)...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More