Group key management method supporting user identity authentication
A technology for user identity authentication and group key, applied in user identity/authority verification, public key for secure communication, and key distribution
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0024] In order to facilitate those of ordinary skill in the art to understand and implement the present invention, the present invention will be described in further detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the implementation examples described here are only used to illustrate and explain the present invention, and are not intended to limit this invention.
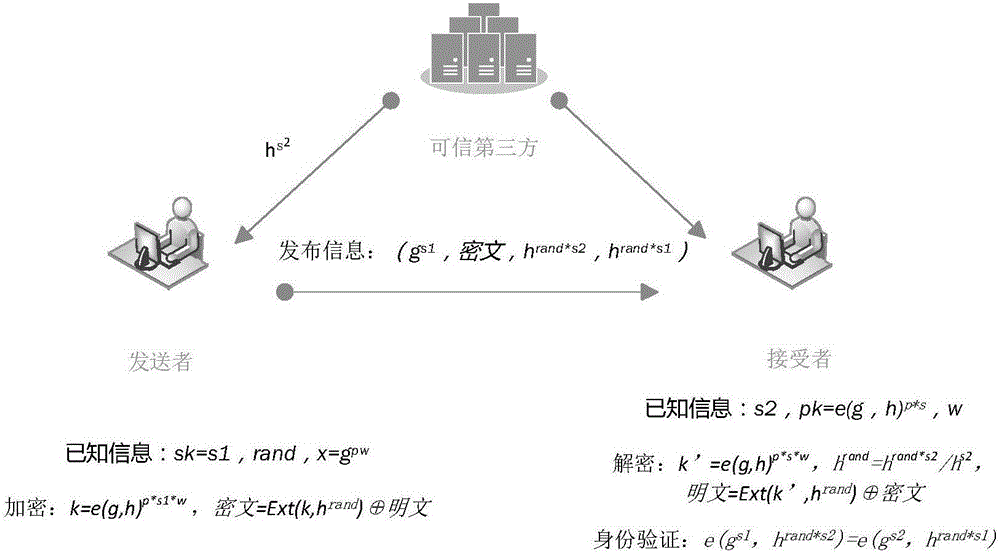
[0025] The present invention mainly solves the problems of data source authentication and key management in the multicast system, and provides a simpler and more convenient public-private key system. The present invention provides a group key management method that supports user identity authentication, Including the three roles of trusted third party, message sender, and message receiver. Users in each multicast system can have two roles of message sender and message receiver. Through the UHPS algorithm, the public-private key algorithm and a set of key upd...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More