Data assessing control method based on blockchain
An access control and blockchain technology, applied in digital data protection, electrical digital data processing, special data processing applications, etc., can solve problems such as poor data access controllability and large blocks
- Summary
- Abstract
- Description
- Claims
- Application Information
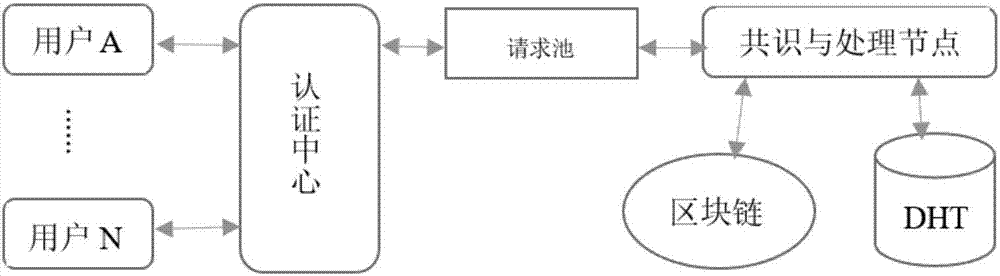
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
[0059] 1. User registration. After the user registers successfully, generate the public key PUKu, private key PRKu, shared key SKu and predefined access rights list Alu; agent generation generates public key PUKa, private key PRKa, shared key SKa and predefined access rights list Ala; other After the institution or user registers successfully, generate public key PUKo, private key PRKo, shared key SKo and predefined access authority list ALo. Users exchange public keys and shared secrets with agents; organizations exchange public keys and shared secrets with agents.
[0060] 2. Consensus and processing nodes process user registration information. The agent calculates according to its own information PUKa, Ala user registration information PUKu, Alu, institution registration information PUKo, Alo,
[0061] Take the hash value of (PUKu, PUKa) as the index Iu of the storage tuple (PUKu, PUKa, ALu, Pu) (P represents the hash value of encrypted user data, which is empty at this t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More