Digital image feedback encryption method based on image network
An encryption method and digital image technology, which is applied in the field of information technology security, can solve the problems of encryption algorithms that are difficult to know plaintext attacks and chosen plaintext attacks, and the statistical characteristics of plaintext and ciphertext are not complicated enough.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0101] Experimental environment: The hardware testing platform of this experiment is: Inter(R) Core(TM) i7-4500U CPU, main frequency 1.8Ghz, memory 8.0GB; software platform is: Windows10 operating system and Matlab2012a. The simulation image uses a Lena image with a gray level of 256 and a size of 256×256.
[0102] Embodiments of the present invention will be further described below in conjunction with the accompanying drawings.
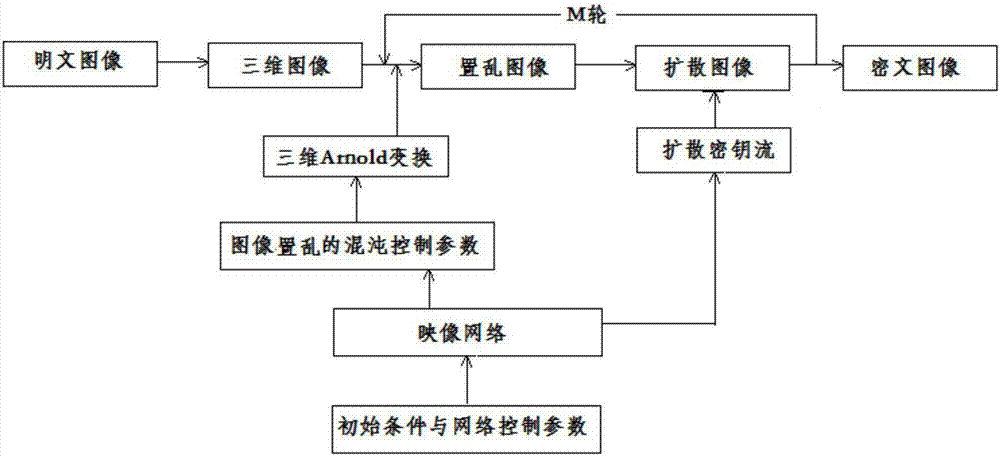
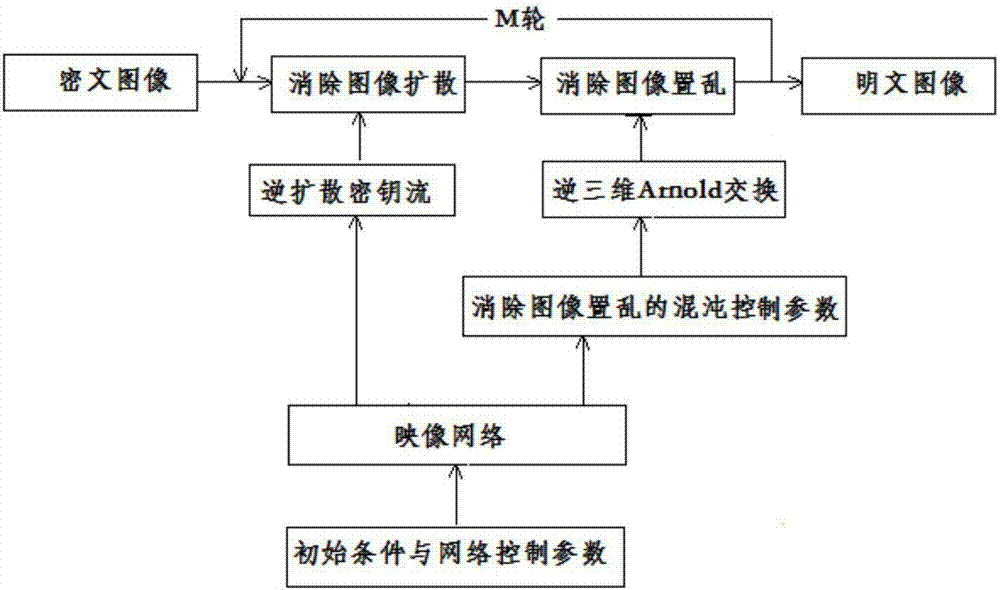
[0103] The digital image feedback encryption method based on the image network that the present embodiment provides includes figure 1 The encryption process shown and figure 2 The decryption process shown includes the following steps:
[0104] 1) For a digital plaintext image with pixels h×w and gray level G, obtain its two-dimensional pixel value matrix PI_1, and convert the two-dimensional pixel value matrix PI_1 into a three-dimensional pixel value matrix PI_2, whose size is t×t×t, when When it is an integer, otherwise fix(·) represents ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More